It seems that the cyber crooks, developing ransomware viruses, never get tired. There is this new Cryakl ransomware scaring the pants off unsuspecting users. Even though it utilizes the strong asymmetric encryption algorithm, cybersecurity experts have been able to crack it.
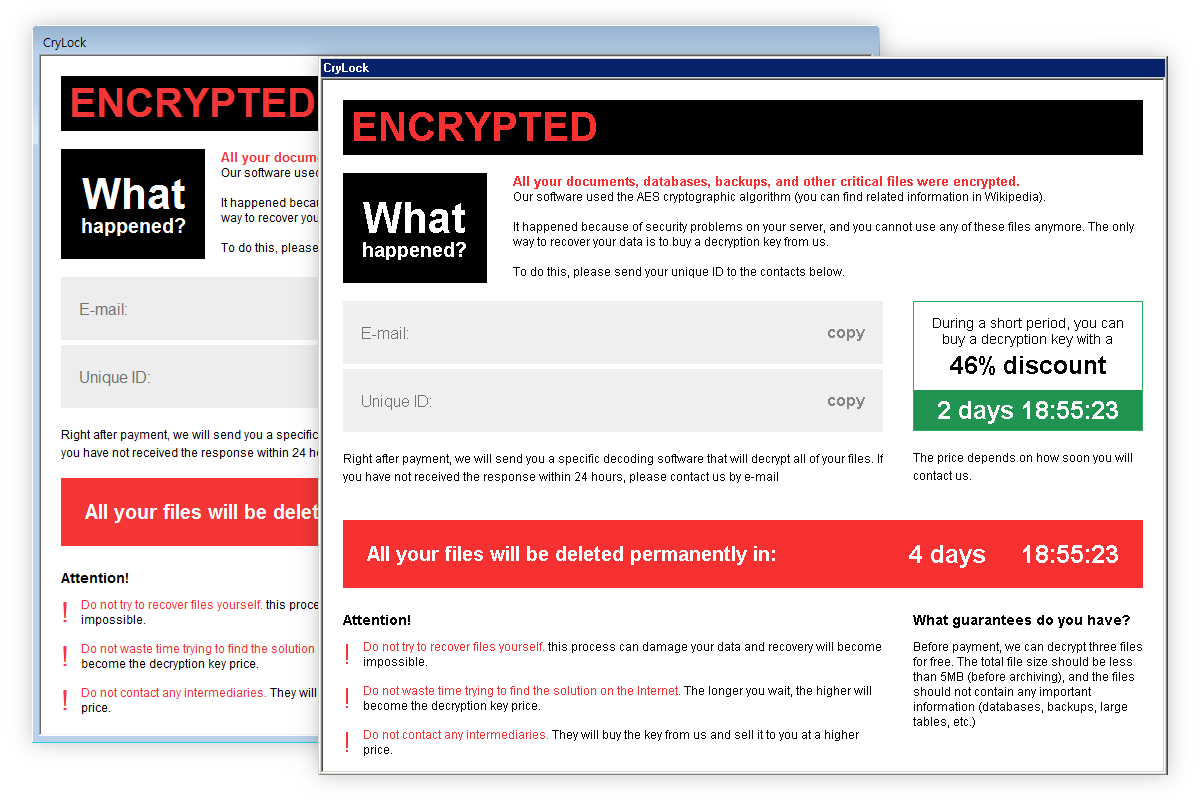
Unfortunately, Cryakl has improved since then, rebranded as CryLock, and continues to attack computers and corrupt files. Victims are asked to pay thousands of dollars if they want to get their files back.
Cryakl Ransomware quicklinks
- About Cryakl/CryLock Ransomware
- How does Cryakl/CryLock Ransomware Spread?
- How to Decrypt Files Encrypted by Cryakl Ransomware?
- Automatic Malware removal tools
- How to recover Cryakl (CryLock) Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Cryakl crypto-malware encrypted files
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
About Cryakl/CryLock Ransomware
The executable of Cryakl crypto-malware is named schvost.exe. Once this file is on your computer’s system, it will begin to pave the way for the encryption procedure. When the system is completely devoured by this virtual piranha, the encryption process is begun. The files, having the following extensions, are targeted:
.dif, .dip, .djv, .djvu, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dtd, .dwg, .dxf, .eml, .eps, .fdb, .fla, .flv, .frm, .gadget, .gbk, .gbr, .ged, .gif, .gpg, .gpx, .gz, .h, .htm, .html, .hwp, .ibd, .ibooks, .iff, .indd, .jar, .java, .jks, .jpg, .js, .jsp, .key, .kml, .kmz, .lay, .lay6, .ldf, .lua, .m3u, .m4a, .m4v, .max, .mdb, .mdf, .mfd, .mid, .mkv, .mml.
Cryakl file-encrypting virus appends ”.cryakl” extension to the filename extension of every encrypted file. For example, document.doc is changed into document.doc.cryakl. It gives 72 days, that are 3 days to pay the ransom and to get the decryption key to decrypt the corrupted data. The ransom note is very laconic.
It reads as follows:
All your files have been
encrypted by Cryakl virus.All the files were encrypted using
cryptographically strong AES algorithm.Pay us in Bitcoins to get them back.
You have 72 hours.
There’s also an HTA or HTML file that Cryakl creates and leaves in every folder. It might look like this:
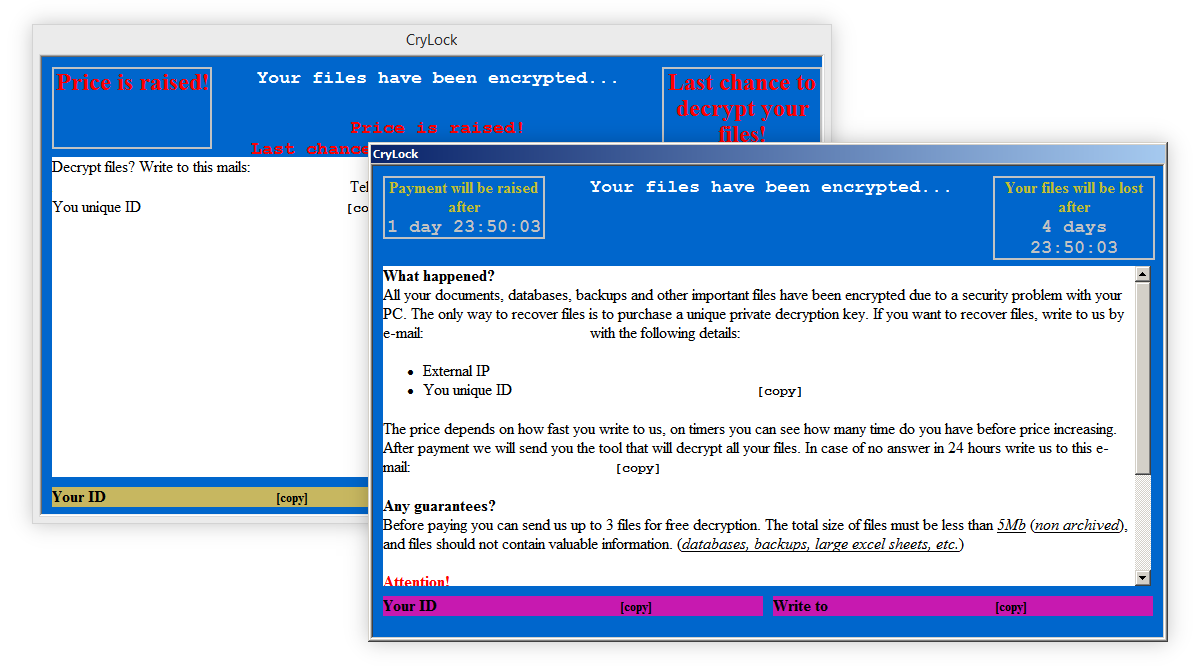
The contact e-mail changes with every other infection. The size of the ransom is not static, either. The victim is told the sum of money they are supposed to pay after they contact the hackers behind Cryakl/CryLock crypto-malware. However, it’s very dangerous to get in touch with these cybercriminals for two reasons:
- They might take your money and not give you your data.
- If you reveal your identity to these criminals, they might target you in the future.
How does Cryakl/CryLock Ransomware Spread?
There are many ways in which ransomware spreads, but Cryakl/CryLock crypto-malware is distributed via two main methods.
The first one involves spambots. These are the programs designed for sending spam. They don’t send typical advertising spam. Malicious spambots employed by ransomware viruses send deceptive letters such as ones informing the victim about unpaid taxes, fines, work documents, and other urgent-looking messages. These emails are meant to scare you or to get you excited. If you open them and download their attachments, CryLock ransomware and other malware are downloaded and installed.
The other method is malicious ads. They let exploit kits, such as Nuclear, Blackhole, Angler, etc. EKs, identify the system’s vulnerabilities to download malware.
How to Decrypt Files Encrypted by Cryakl Ransomware?
Files locked by older versions of Cryakl can be decrypted for free. Cryakl Decryptor has been developed by IT experts of Kaspersky Lab. Feel free to use it. It is provided completely free of charge.
Update of the 9th of February, 2018. Thanks to founders and partners of the “No More Ransom” project, more and more ransomware viruses are becoming decryptable. This time, the Cryakl virus should not be considered a threat anymore. Victims of this malware are able to recover their files for free!
Update as of the 17th of May, 2021. Unfortunately, new versions of Cryakl and CryLocker (versions 1.9.2.1, 2.0.0.0) can’t be decrypted this way.
Data recovery programs (EaseUS) might help restore some data in some circumstances, but your mileage may vary.
Just remember that malware must be removed as soon as it is possible. Apply powerful automatic malware removal tools such as Spyhunter. These professional security scanners will perform a full system scan to detect and eliminate any leftovers by the Cryakl virus. The guide for manual removal of the ransomware is provided just a few scrolls below.
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Cryakl (CryLock) Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Cryakl Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Cryakl ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Cryakl ransomware virus. You can check other tools here.Step 3. Restore Cryakl virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Cryakl cryptomalware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Cryakl crypto-malware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








