Lately, new ransomware infections have been popping one after another without interruptions. ZinoCrypt sample features a label “2017 Edition” and it was first detected in late March. It does not appear to be an extremely modern or improved variant from the ones we have already analyzed. ZinoCrypt virus works with complicated algorithms to harm users’ data, stored in hard drives. After files go through the process of encryption, they will become no good. Influenced data will be marked with .ZINO extension. This variant strongly suggests that no free file-recovery tool will have the capacity to decrypt. Victims are expected to contact hackers via an email address [email protected]. After people contact crooks, we predict that hackers will giveaway their further demands, like, the fee for the special decryption software and unique key.
Short summary of ZinoCrypt ransomware
ZinoCrypt ransomware is a fearsome example of malware and we hope that you won’t be bothered by it. Nevertheless, if your photos, videos, documents, presentations and other types of files happen to be influenced by cryptography, you are welcome to seek assistance with us. Leave a comment below and we will help you in any way we can. First, you should continue on reading this article to find out more about this infection and know exactly what you are up against.
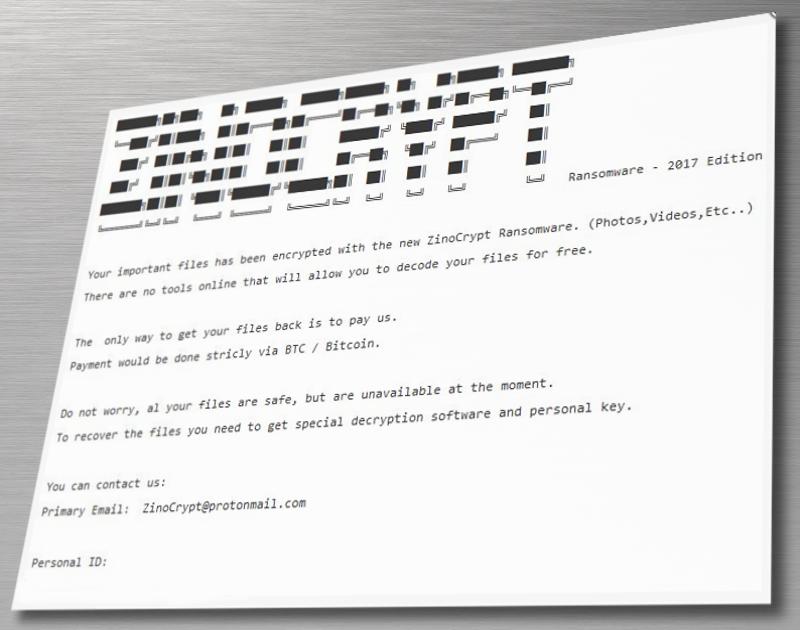
After encrypting files and storing private decryption keys in private servers, creators of ZinoCrypt virus have leverage. They now are able to make demands, which they make evident in the ZINO_NOTE.txt file. This short message contains the most general information, explaining that people have become victims of ransomware and they have to contact [email protected] email address if they wish to learn more about the recovery of files. Ransom note also contains a unique ID number for each compromised device. This personal number will be required to be sent via an email address.
Internet users should fear ZinoCrypt virus and its encryption. Security analysts are not sure whether RSA or AES ciphers are involved in the strategy that virus hopes to complete. However, a temporary belief is that AES algorithm is the one that damages data. As soon as the encryption process goes smoothly, ZinoCrypt ransomware will show itself by adding its original extension to the files and by placing the .txt file with blunt statements.
Repairing files that ZinoCrypt ransomware encoded
Victims of ZinoCrypt ransomware are probably hopeful that we can give good news. Sadly, there is no guaranteed way of restoring files. However, analysts can release a decryption tool any minute. If there are any changes, we are sure to inform you about them. Of course, some victims can consider paying the demanded sum of money to decrypt files with the tools, provided by the creators of ZinoCrypt virus.
In order to become aware of the required sum, people are requested to contact them via email address we have mentioned in the sections above. If you do contact them, you please do not do it for the sake of following their instructions. If you wish to help security researchers generate a free file recovery tool, we advise you to demand that hackers would prove themselves. How? By decrypting a couple of files for free, of course. As soon as you receive the file back, send encrypted and decrypted versions to security researchers.
Schemes to deliver ZinoCrypt ransomware
ZinoCrypt virus is not expected to try out new ropes and introduce new techniques for ransomware distribution. It is more believable that payloads will be added as attachments to spam letters that will reach users’ inboxes. If you happen to receive a questionable email, you should check its reliability before opening it or downloading files it offers. It is no news that exploit kits can play a big part in ransomware transmission as well. Avoid visiting unknown websites.
As for the removal of ZinoCrypt virus, you should do it before trying to recover data. Just in case, copy all of the encrypted files. Run scans with Spyhunter, Malwarebytes or other anti-malware tool you prefer. After eliminating the detected malware threats, you can check whether Shadow Volume copies were deleted by the ransomware. If not, it is possible to restore files for free. You will be informed about other options if you continue to read this article.
Zinocrypt Ransomware quicklinks
- Short summary of ZinoCrypt ransomware
- Repairing files that ZinoCrypt ransomware encoded
- Schemes to deliver ZinoCrypt ransomware
- Automatic Malware removal tools
- How to recover ZinoCrypt ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover ZinoCrypt ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover ZinoCrypt ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before ZinoCrypt virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of ZinoCrypt ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to ZinoCrypt virus. You can check other tools here.Step 3. Restore ZinoCrypt ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually ZinoCrypt virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover ZinoCrypt ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.