Even though some crypto-ransomware viruses include references to Japan in their titles (JapanLocker, KawaiiLocker) they do not seem to be targeting people from this country. However, Takahiro Locker seems to be focused on the latter audience as its ransom note and the lock screen present texts, written in Japanese characters. Anti-malware tools are able to successfully detect this virus. It travels as a Trojan, tricking people to voluntarily download its payload. That is why security programs find these malicious entries: W32/Scar.NZLN!tr, Trojan.GenericKD.3222895, Ransom_TAKALOCKER.A. Different applications can detect it differently, but the issue remains. It is a dangerous ransomware virus and you should regularly run security scans to check the state of your device.
About Takahiro Locker ransomware
The word “Takahiro” actually means a masculine Japanese name. However, security researchers are more concerned with the virus that has been identified as Takahiro Locker virus. It is not a completely new infection since it has been around since the summer of 2016. After it proceeds with the most common ways for infiltration, it moves onto other equally crucial goals that can lead to a fatal outcome of losing all of your files. In order to be launched together with all of your applications, Takahiro Locker virus has to program its payload to make changes to Windows Registry Keys. Entries that are responsible for launching software are altered to include the malicious executable.
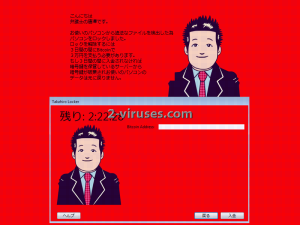
As long as the payload functions uninterrupted, it initiates scans and looks for files to encrypt. During this process, infected victims might suffer from slowly-running computer. However, this hint is not always received. Takahiro Locker virus, if left untreated for a necessary amount of time, will encrypt your files. This specific variant does target a relatively small number of extensions, but the selected ones are the most popular among computer users. Then, after encryption is finally completed and the payload has done most of its job, it still has to contact the Command and Control server of its creators. They are informed about a new victim and some parts of his/hers technical information can be sent as well. In the ransom that is presented, the language seems so unfamiliar that we are convinced that many people are unaware what is says. The following content is found in the lock screen:
Hello,
this is Tang, a Lawyer.
You have made an illegal file transfer, so I have locked your PC.
To unlock your files, you need to pay 3 Bitcoins within 3 days.
You need to have 30,000 Japanese Yen, to transfer them to Bitcoins and send them to me.
If you don’t pay within 3 days, the key for decryption will be deleted from where the server is stored and the data of your PC can no longer be returned.
Click the button “Next”.
You might guess that the actual author(s) of this ransomware are no lawyers or anything even closely related with that. Any rule-abiding person would recognize that demanding money for decryption of ruined files is a cyber crime. Please do not believe the ridiculous accusations that are placed on you by Takahiro Locker virus.
How to Decrypt Files Encrypted by Takahiro Locker Ransomware?
As seen from the ransom note, Takahiro Locker virus waits 3 days for users’ transaction of bitcoins. The demanded 30,000 yen is an amount of 289.1037 US Dollars. The fee in yens strikes as much bigger, right? This is quite confusing: the indicated number of bitcoins is 3 but it is not right because the demanded sum is claimed to be 30,000 yen. Either way, paying this sum is not a recommended decision. This won’t lead to positive outcome and you will only be wasting your precious money. Right now, security researchers have not found a way to crack the codes of Takahiro Locker virus. But please wait and never think about paying the demanded fee.
How is Takahiro Locker Ransomware Distributed?
Takahiro Locker virus might have gotten into your device after you downloaded an attachment from one of your emails. If your inbox regularly gets letters that are bizarre, then it might be that you are being targeted by creator of ransomware. Please never open such letters and delete them. It would be advisable to keep your inboxes clean. Before opening an email, entering the domain it suggests or downloading an attachment, always make sure that the letter has reached you from the right source. If not, then delete it immediately.
Spyhunter or Hitman will help you to take care of Takahiro Locker virus. This has to be done to secure your device. More information about decryption and removal can be found in the sections below.
Takahiro Locker Ransomware quicklinks
- About Takahiro Locker ransomware
- How to Decrypt Files Encrypted by Takahiro Locker Ransomware?
- How is Takahiro Locker Ransomware Distributed?
- Automatic Malware removal tools
- How to recover Takahiro Locker ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Takahiro Locker ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Takahiro Locker ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Takahiro Locker ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Takahiro Locker ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Takahiro Locker ransomware. You can check other tools here.Step 3. Restore Takahiro Locker ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Takahiro Locker ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Takahiro Locker ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








