Sage ransomware is written from the source code, which is the code of TeslaCrypt. It is one of the many encrypting trojans, but despite the fact that Sage crypto-malware does not have some specific features does not make it a less threatening cyber pest. The name of this ransomware threat fits the program code it denotes perfectly well – there is no decryption service provided by the front of cyber security engineers. For the time being, users are invited to get to know what has already been discovered about Sage file-encrypting virus.
The Specifications of Sage Ransomware
Sage crypto-locker implements the asymmetric encryption scheme to render the data containers on the compromised machine useless. The following types of data files can get encrypted by this encrypting malware:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, .doc, .epub, .docx, .fb2, .flv, .gif, .gz, .iso, .ibooks, .jpeg, .jpg, .key, .mdb, .md2, .mdf, .mht, .mobi, .mhtm, .mkv, .mov, .mp3, .mp4, .mpg, .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt, .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2
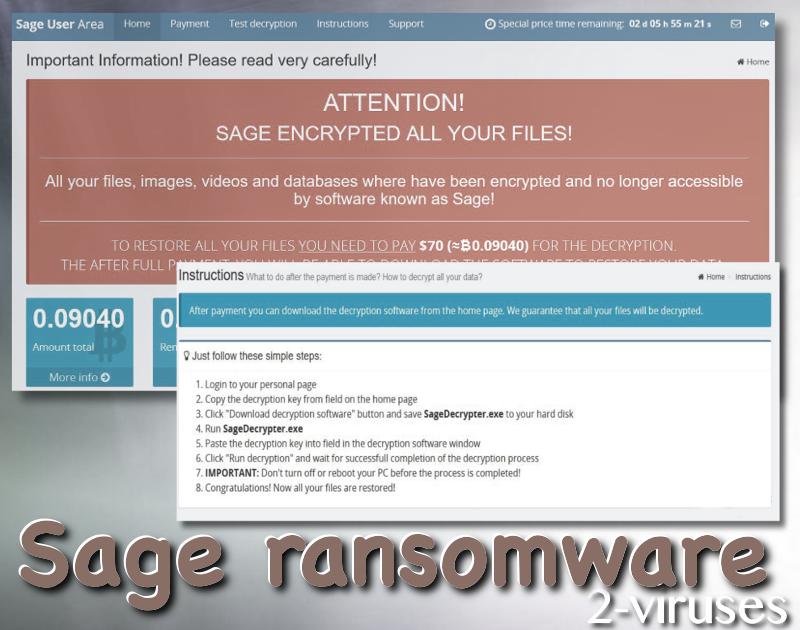
The extensions of the latter files are appended the extra extension, which is the name of the encrypting program. For example, the Movie.avi file, after having been encrypted, is renamed as Movie.avi.sage. The same is done with all of the targeted files, which have been locked. After all of the aimed at data has been encrypted, which means that the process of encryption has been ended, the affected user is provided with the following two files: !Recovery_[your ID].txt and !Recovery_[your ID].html, which enclose the following note of the ransom:
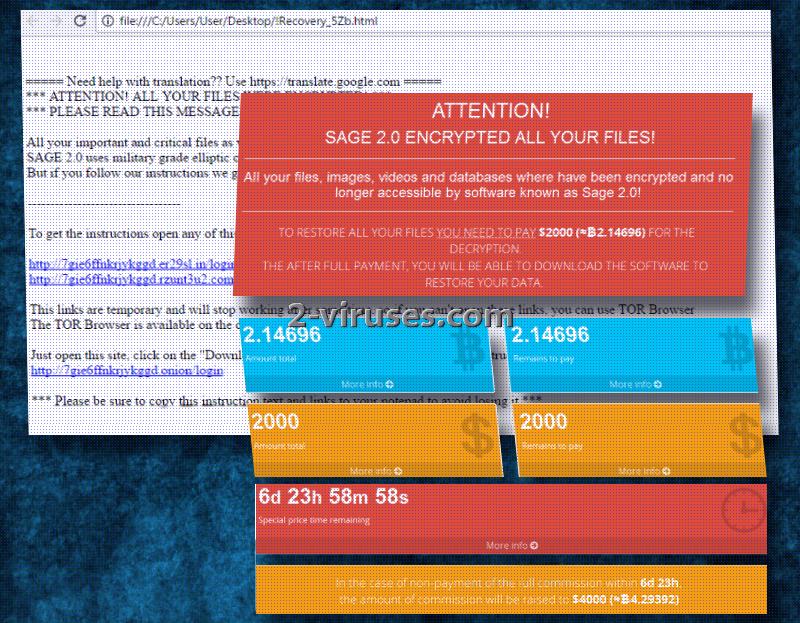
ATTENTION!
Sage encrypted all your files!All your files, images, videos, and databases were encrypted and made inaccessible by software known as Sage.
You have no chance to restore the files without our help. But if you follow our instructions files can be restored easily. Instructions on how to get your files back are stored on every disk, in your documents and on your desktop. Look for files !Recovery_[your ID].txt and !Recovery_[your ID].html
If you can’t find this files, use the program “Tor Browser”(you can find it in Google) to access the (onion)web site http://qbxeaekvg7o3lxnn.onion to get your instructions
560 USD to 1120 USD is the range of the ransom, which the creators of Sage file-locker expect from the victims. The first sum of money is the initial payment, while the second amount is the price the tortured users have to pay one week after the encryption.
Have You Been Hit by Sage Ransomware?
What you need to do, if your computer has been infected with Sage ransomware infection, will be explained now. Firstly, you need to make the image of the affected data. If none of the following data recovery methods fits your situation, you will need to wait for the decryptor from security experts, for which you need to have those copies. Then, you need to remove the ransomware. Sage virus should be surmounted by Spyhunter or Malwarebytes antivirus apps. You can find the manual removal instructions at the end of the article, but they can be quite troubling to implement. Moreover, apart from the actual ransomware, there can be additional malware programs installed on the system, which will not be taken into account, if you aim at removing the sole malware manually. In addition to all this, your PC will still lack the protection and similar cases of infections can occur.
Only after having removed the malware, it is the time for the recovery of the data. For this purpose check VSS (the Volume Shadow Copy Service), if it has been running and if this system restore function has not been affected. Use the removable drives, if they were not plugged in during or after the infection before the removal of the virus. If you have been storing your data in online storages, make use of that. There is also data recovery software available, such as Recuva, etc., which can be applied.
The source of Sage ransomware has not been identified yet. Thus, be very careful, especially, if you do not have an updated and trustworthy security software set on your device up. The common sources of ransomware infections are the spam e-mails, fake downloads, compromised websites and infected advertisements.
Update of the 24th of January, 2017. A new version of this ransomware, appending the same extension (.sage), has been detected. Sage 2 uses the same payment site but has improved its distribution since it targets more users than before. Travels via spam letters.
Sage Ransomware quicklinks
- The Specifications of Sage Ransomware
- Have You Been Hit by Sage Ransomware?
- Automatic Malware removal tools
- How to recover Sage Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Sage Ransomware encrypted files

Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Sage Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Sage Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Sage Ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Sage Ransomware. You can check other tools here.Step 3. Restore Sage Ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Sage Ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Sage Ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








