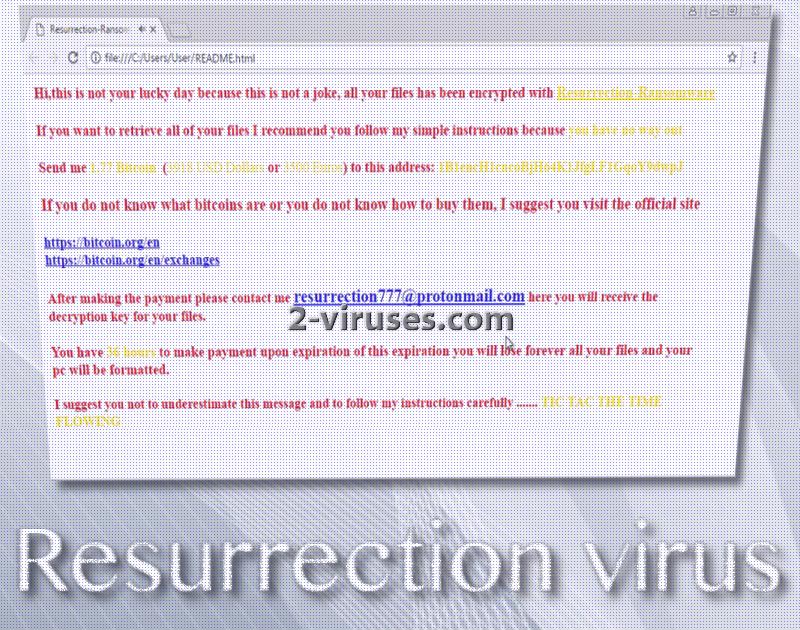
Resurrection ransomware virus is a Harry-Potter-themed infection. The ransom note, found as a .html file, will launch in the preferred browser and play an additional audio track. The music, similar to the worldwide franchise, will accompany the ransom note, beginning with words “Hi,this is not your lucky because this is not a joke, all your files has been encrypted with Resurrection ransomware”.
The letter elaborates further that for the sake of restoring files, victims have no other option but to pay 1.77 BTC which is actually 4577.17 US dollars and not 3918 US dollars as the ransom note mistakenly implies. After this huge amount of money reaches the indicated bitcoin wallet, victims are instructed to make contact with [email protected].
This crypto-virus is based on the popular Hidden Tear project. Like most of these variants, ransomware exploits AES algorithm of encryption to make digital files completely unusable. Digital data, influenced by the cryptography cipher, will be joined by a .resurrection extension. What is more, there is no reason to pay the demanded ransom as security researchers have evaluated this infection to be decryptable if necessary.
Two payloads have been detected to belong to this ransomware infection. If you notice WindowsFormsApp1.exe file or shiva.exe file, then, crypto-virus might be currently making a path for file-encryption to take place. The first version is much more difficult to detect, while the second was discovered by the majority of security tools.
Its course of action is probably similar to variants that we have discussed before. It finds deceptive means of infiltration, then the payload modifies Windows Registry keys, extracts additional files, may contact its C&C server, scans hard drive for files to encrypt, initiates file-encryption and leaves a ransom note. README.html file will be placed in the C disk, User folder. If you happen to become threaten by this variant, we advise you to remain rational. Paying such a gigantic (or even small) ransom is never the smart decision.
Ransomware prevention
There is actually no need to spend hours thinking about possible methods for decryption. If you have become infected with this variant, we are advising you to contact researchers from Bleeping Computer and they might help you recover your encrypted digital data. Since this variant is found to be quite easy to treat, we do not encourage wasting money.
However, not all victims of ransomware viruses have a chance to be offered instant assistance and help. For some, the decryption process might take a while. Therefore, we do hope that you do not rely solely on security analysts. You should take the matters into your own hands and find ways how to secure your files from being encrypted. This can be done by storing files into more than one location, like backup storages or USB flash drives. Both of these places will protect your files from algorithm ciphers.
Additionally, ransomware viruses that are not decryptable might be taken care of in other ways. For instance, users can check whether Shadow Volume Copies are still undamaged and ready to be restored. There are also multiple universal file-recovery tools that can help you recover lost data.
After securing your files, you should always try to remain safe from malware in general. Avoid installing programs you do not recognize, also be prepared to always refuse offer from unknown sources. This also includes email messages from unfamiliar senders. If those letters contain attachments or URLs, this should discourage you from interacting with message, especially if the person that send it is not recognized.
For the removal of malware, it would be better to run a full security scan. Crypto-viruses can be tricky to eliminate. Therefore, we think that a stronger option should be selected. Manual removal can have negative impact on an operating system, but if you are still determined to run it: leave a comment below if you have any questions.
Resurrection Virus quicklinks
- Ransomware prevention
- Automatic Malware removal tools
- How to recover Resurrection virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Resurrection virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Resurrection virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Resurrection virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Resurrection virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Resurrection virus. You can check other tools here.Step 3. Restore Resurrection virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Resurrection virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Resurrection virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.