MoWare HFD ransomware virus is a hot off the fire infection, but its structure and trademarks are not considered modern. It is a sample, purely based on Hidden Tear open source project which does not suggest that its creators are skilled programmers. One peculiar aspect is that instead of using AES or RSA encryption algorithms, this variant encrypts digital data using XOR encryption routine. The ransomware also contacts hosts from Germany. This the country that authors might be from. Additionally, it sends DNS requests to two domains Safakguvenkaya.com and Google.fr. Currently, the ransomware does not encrypt files, but the possible extension has been determined to be .H_F_D_locked. Variant might still be in development mode, which means that it is unknown whether a more functional version of this won’t surface.
If the ransomware is improved and it begins to encode files without any structural flaws, more than 600 file-types are going to be the potential digital data to ruin. If we will be informed about changes in the activity of this infection, we are sure to provide you with the latest details. Since some preliminary analysis has already been established, it is evident which executables would be targeted. In theory, infection has the capacities to taint all of your documents, pictures, PDF files, video material, music and other more rare files. Since the types of targeted data are diverse, the computer can run into certain obstacles after some essential processes get encrypted.
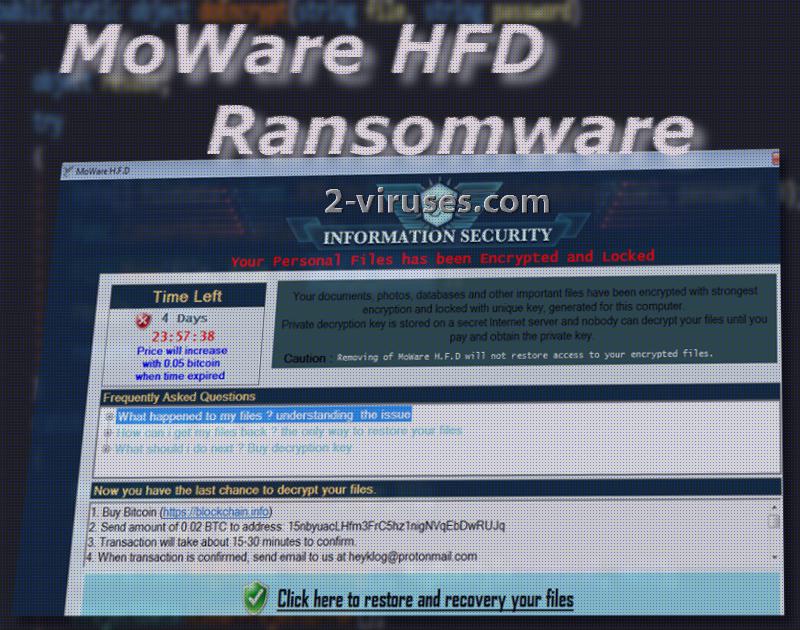
After the encryption process, ransomware will launch a original window, providing the main information to the victims. Infection also gradually increases the ransom amount. It will start from the 0.02 BTC (55.36 US Dollars) and will be enlarged to 0.05 BTC (174.47 US Dollars). 15NbyuacLHfm3FrC5hz1nigNVqEbDwRUJq bitcoin wallet belongs to hackers and welcomes every submission from scared victims. Since infection does not appear to successfully complete file-encryption, there will be no reason at all to pay the demanded ransom.
Hiddentears.exe is proven to be the payload of this infection. Its analysis revealed that it monitors specific registry keys for changes and even opens file with deletion access rights. This means that it can mark files to be deleted. This might happen when the ransomware will be attempted to be deleted from an operating system. Therefore, even though the ransomware won’t encode files, it might cause some security issues during the process of its removal.
Therefore, the process of restoring files and getting rid of the infection should be handled very carefully. Before you try to recover files, it is crucial to eliminate every trace of malware. If you do not do this, even if you are successful in the file-recovery process, the ransomware might just encrypt digital data again. To avoid triggering any buttons that might start automatic removal of files, we advise victims to move files into an additional location like a flash drive. Then, run a security scan with Spyhunter or Malwarebytes to delete MoWare HFD ransomware from your device completely.
One of the most beneficial decisions is to store files in backup storages before an infection manages to corrupt your data. Having the most essential digital in multiple places will help you retrieve files if samples in one of them get corrupted or deleted. Flash drives also work in favor of the user.
It is also important to grasp the notion of ransomware distribution. While the latter virus might not be distributed rapidly, these infections have a way of compromising systems. Malicious payloads could be uploaded into random websites, advertisements, and users’ interactions with this content could trigger an automatic download. For this reason, stop visiting potentially hazardous domains. Additionally, spam campaigns could deliver email letters to random accounts. These messages will contain malicious attachments or require users to visit domains that are actually distributing malware.
Moware Hfd Ransomware quicklinks
- Automatic Malware removal tools
- How to recover MoWare HFD ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover MoWare HFD ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover MoWare HFD ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before MoWare HFD ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of MoWare HFD ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to MoWare HFD ransomware. You can check other tools here.Step 3. Restore MoWare HFD ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually MoWare HFD ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover MoWare HFD ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








