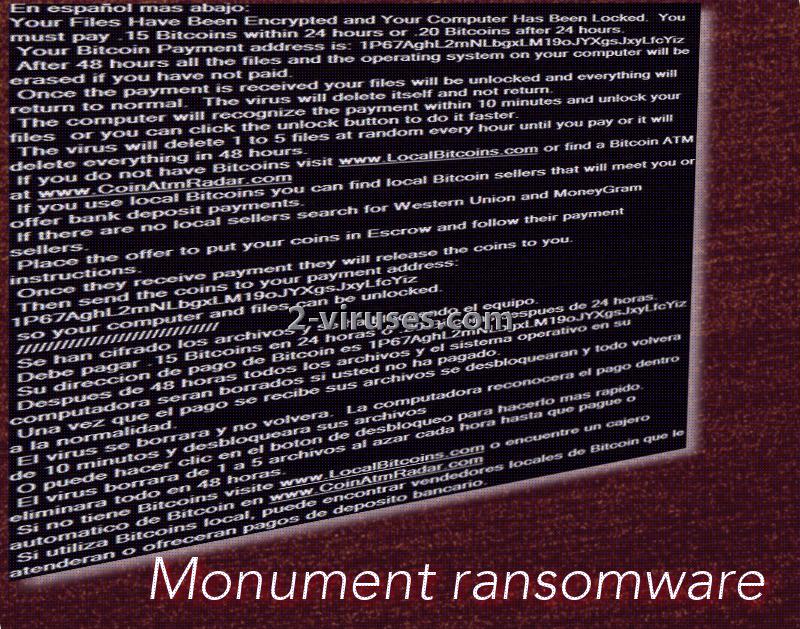
Monument crypto-virus has multiple names that security researchers use to refer to this infection. DarkLocker, Monument ransomware or a virus, closely related with the old JigSaw sample. In addition to that, the recently caught threat contains elements of Spanish language since many of the statements in the ransom note are written in the latter language. Due to the combinations of demands in English and in Spanish, we presume that a wide range of people can be targeted by Monument ransomware. This sample has a screen-locker feature, meaning that your files will not only be encrypted, but sealed. During the first 24 hours of the infection, cyber criminals demand 155.30 US Dollars (0.15 BTC) to be sent to the following bitcoin wallet: 1P67AghL2mNLbgxLM19oJYXgsJxyLfcYiz. After the second day of the infection begins, the ransom will grow to 205.80 (0.20 BTC).
Investigation of Monument ransomware
Monument crypto-virus is not your typical ransomware: it does not only encrypt files, lock access to the system of infected device, but also blames the victim for watching pornographic content online. The screen-lockers features statements, that a person should stop exposing himself/herself to pornography. We have a suspicion that this usually dangerous content can be responsible for the Monument infection. If you visit reprehensible websites that contain pornographic material, you should realize that these sites have precarious advertisements, potentially contaminated by malware.
According to the screen-locker that Monument virus occupies screens with, after an hour passes and a victim has not paid the required fee, from 1 to 5 files can be deleted. Gradually, after 48 hours pass and victim has not filled the indicated bitcoin wallet with bitcoins, his/her data and operating system will be completely wiped out. Since losing all of your valuable information is a really disturbing threat, and the ransom that the hackers demanded is not as steep, people might see no better choice but to pay.
Monument virus, before doing anything else of a particular significance, will see infiltration as its main priority. After the payload has been placed into a decide, Windows Registry Keys will be modified to launch the two files it places into a device: can.exe and winlk.exe. It is yet to be determined which ciphers are to be used for file-encryption. As for the extension that could be appended to the encoded data: we do not notice any reports that would suggest that Monument ransomware adds a unique ending to a corrupted file.
What about the files that are ruined by Monument ransomware?
Monument crypto-virus will encrypt files with one of the popular tools for encryption. In order to prevent files from being gradually deleted, victims are expected to make a transaction of bitcoins. If you are very desperate, we do not think that there is a way of completely discouraging you from paying. However, we can try. It is possible that cyber criminals will be only interested in receiving money and won’t restore your system nor files that have been deleted/encrypted. Since the more time it will take for you to pay the more files are going to be removed, you should try to get access to your system. Recommendations below might help. As long as you were able to have your computer load up fully, you should not hesitate to initiate a security scan and remove the infection. Spyhunter or Hitman
Actions that might lead to Monument ransomware
It is possible that visiting questionable domains might have lead to a ransomware infection. By entering pages that feature a lot of advertisements and automatically redirect visitors to even more shady websites, can be the source of Monument virus. Do not expose yourself to viruses and visit only respectable domains. In addition to that, cyber criminals that designed Monument screen-locker, might be initiating spam campaigns to distribute a payload of their creation. Do not read or download attachments from random letters than end up in your inbox, especially in the spam folder.
Monument Ransomware quicklinks
- Investigation of Monument ransomware
- What about the files that are ruined by Monument ransomware?
- Actions that might lead to Monument ransomware
- Automatic Malware removal tools
- How to recover Monument ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Monument ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Monument ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before DarkLocker ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Monument virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Monument ransomware. You can check other tools here.Step 3. Restore DarkLocker ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Monument virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Monument ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.