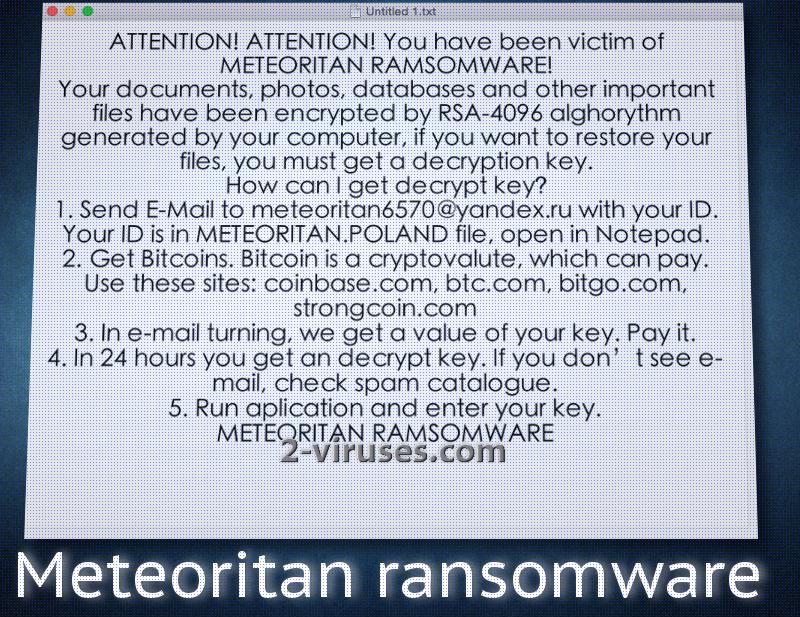
Meteoritan crypto-virus has been revealed to pose as a threat to the Internet user community. This type of malware effects data in one of the worst ways possible: files are encoded with special, sophisticated ciphers. The origin of Meteoritan ransomware could be Poland as there are certain hints that lead to such an assumption. METEORITAN.POLAND file is inserted into victims’ devices and it contains an original ID number. This sample explains that victims can contact its creators via [email protected] email address. Of course, payment for the file-decryption will be accepted via an online payment system which reassures anonymity for both parties. Of course, hackers have stronger reasons to conceal their true identities. If your files are no longer operative, it might be that your device has become severely damaged by a ransomware. Usually, we are able to determine ransomware by different extension, but there are no clear mentions of an extension in case of Meteoritan virus.
Review of Meteoritan virus
As soon as a payload of Meteoritan virus complements its journey successfully, it will be placed in one of the folders. Presumably, ransomware.exe file could be the source of all your problems. In addition to that, virus will insert more than one ransom note. Where_are_your_files.txt and readme_your_files_have_been_encrypted.txt. As we have indicated in the section above, METEORITAN.POLAND contains victims’ ID numbers that are originally expected to be sent to hackers in an email letter. Hackers will respond with more detailed instructions how the events are anticipated to play out. Victims’ will be informed of a specific bitcoin wallet which should be filled with bitcoins.
Despite the fact that the Meteoritan virus claims to corrupt data with RSA-4096 algorithm for encryption, there is a possibility that the ransomware is bluffing. It might be that no files are actually encrypted and virus is making empty threats. However, if you discover that decryption software is certainly required to fix damaged data, remember that obediently executing hackers’ demands is not the only option. It is impossible to determine the exact amount of bitcoins that Meteoritan virus will indicate as the fee. In the ransom note, the ID number of each individual victim is supposed to calculate the exact sum. Presumably, the main factor will be the amount of encrypted files.
Creators of Meteoritan virus cannot be trusted. Even if they claim to provide users with a special software and a decryption key, these promises won’t necessarily be carried out. If this ransomware does corrupt files, it will also place a decryption key in a file called METEORITA.RAMSOM. Please do not consider paying the ransom hackers demand.
Restoring data that Meteoritan virus damaged
Before you believe that Meteoritan virus has actually encrypted all of your data, you should check whether your files were actually damaged. If the encryptions turns out to be true, you still should not think about paying the ransom. There are more option to consider. For example, we do not have knowledge about whether Shadow Volume Copies are eliminated by the ransomware. Please check whether they are left safe and sound. In addition to that, you can try restoring files with file-recovery tools that have been already created for the same purposes. If you are a cautious Internet user, you might have felt the need to store your files in backup storages. If you have, then no ransomware is a threat to you.
Meteoritan virus: how does it travel?
Meteoritan virus can reach devices after their owners were inattentive or simply reckless. You are advised to regularly clean your email inboxes to make sure that there is no spam. If you do notice that an odd letter has been sent to you, please review the email carefully. Before opening it, be certain that its sender is reliable. After you have opened it, look closely at the message. If it sounds shady and features bizarre attachments, then you are not recommended to download such a file.
Before trying to recover your files, please remove Meteoritan infection first. You can do this manually or by simply taking advantage of anti-malware tools. Spyhunter or Hitman won’t leave any malware in your system.
Meteoritan Virus quicklinks
- Review of Meteoritan virus
- Restoring data that Meteoritan virus damaged
- Meteoritan virus: how does it travel?
- Automatic Malware removal tools
- How to recover Meteoritan virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Meteoritan virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Meteoritan virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Meteoritan ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Meteoritan virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Meteoritan ransomware. You can check other tools here.Step 3. Restore Meteoritan virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Meteoritan ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Meteoritan virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.