There are so many different services that you can find on the Internet: currently, ransomware-as-a-service projects have been starting to bloom. It might be just the influence of spring, but we do hope that hackers won’t continue on trying to turn ransomware-creating into a profitable business. However, we have already written articles about RaaS services, advertised in secret domains. A couple of examples that we have discussed include FileFrozr, PetrWrap, DynA-Crypt or LMAOxUS services. Despite being advertised as a high-quality service for a price of 175 US dollars, after researchers analyzed a sample of Karmen ransomware, it was determined that almost every security tool has the skill to detect this variant of malware.
Characteristics of Karmen ransomware
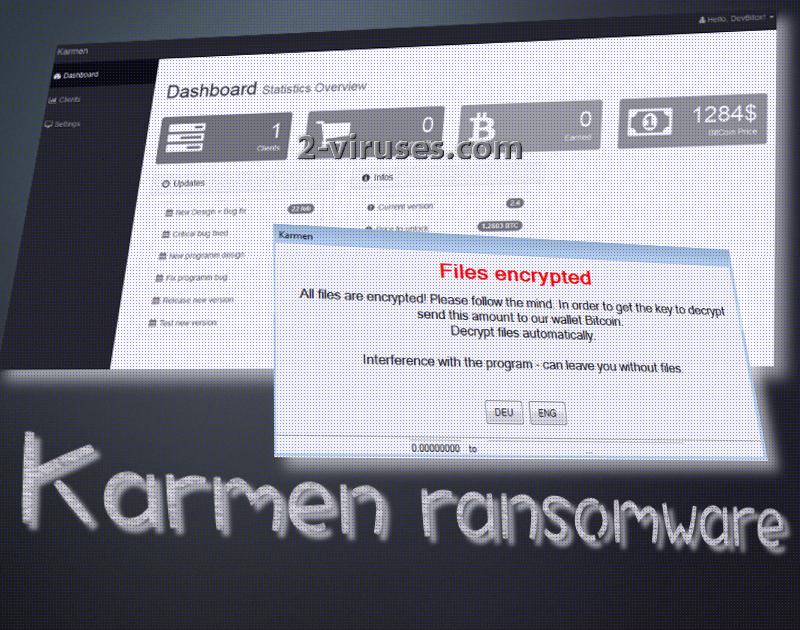
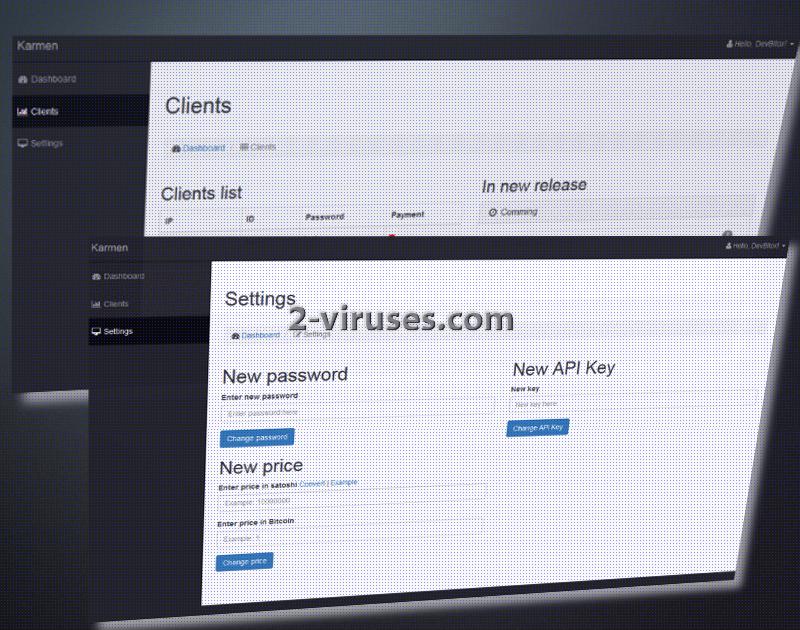
First, we should observe the features that are explained to be provided for the clients that decide to become cyber criminals. Karmen ransomware is indicated to be aiming to infect people from more than one country by displaying the messages with instructions in several languages. As soon as the service is paid for, its new clients will be given a permission to utilize a unique control panel. This will be the tool for people to create an individual version of a Karmen virus. The encryption is implemented while using AES-256 cipher for encryption.
Now, for the downsides of Karmen ransomware and its service. As we have managed to discover, the service that the hackers are explaining to provide are not that worthy of being utilized. It appears that Karmen variants are written based on the open source project HiddenTear. Of course, the founders of Karmen made some alterations, but the base remains the same. The samples also are explained to check whether a computer is protected by sophisticated tools. If the payload found out that an infected device is properly secured from further damage, the malicious executable would presumably self-destruct.
However, if Karmen virus sees no issue in proceeding with encryption, it will certainly begin this process. This sample does not leave .txt or .html files to inform victims about the situation. It appears that a table with a brief explanation is presented instead. People are discouraged from interfering with the encryption process. Instead, they are to enter click on either DEU or ENG buttons. This will potentially lead to a more detailed instructions, indicating a bitcoin wallet and the amount of demanded bitcoins.
Considering that Karmen virus is based on a HiddenTear project, it was possible to assume that it won’t take long for security researchers to discover a way to help victims recover their data. Security researcher Michael Gillespie advises people to use a free decryption tool to resurrect files that Karmen ransomware might have ruined. If that does not help, he advises that people contact him for a consultation.
Tips to secure your files from Karmen ransomware
Obviously, if you have a lot of valuable data, it would be recommended to protect it accordingly. One of the easiest ways is to simply make copies of those files and store them in an additional location. It might be that you will select an online storage for files. Recently, we noticed that not all backup storages are secure, so you are advised to pick your storage carefully. Additionally, you can consider moving your files to a USB flash drive. This option is easy, quick and definitely won’t cost a thing.
Ways that Karmen ransomware could be distributed
Karmen cryto-virus first has to be purchased. As soon as a person obtains a membership, he or she can modify the sample and start looking for victims. It might be that malicious spam campaigns will be selected as the way to spread the malicious file of Karmen. If a new member is more skilled, he/she can exploit vulnerable websites for the purpose of distributing their virus.
If you have become infected with a variant of Karmen crypto-virus, we advise you to contact the security researcher we referred you to. Of course, before doing so you should remove the ransomware from your device and try the decryption tool.
Karmen Ransomware quicklinks
- Characteristics of Karmen ransomware
- Tips to secure your files from Karmen ransomware
- Ways that Karmen ransomware could be distributed
- Automatic Malware removal tools
- How to recover Karmen ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Karmen ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Karmen ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Karmen virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Karmen ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Karmen virus. You can check other tools here.Step 3. Restore Karmen ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Karmen virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Karmen ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.