JeepersCrypt ransomware virus is categorized as a Portuguese malware since its screen-lock displays demands in this language. Let’s go straight to the pleasant part: JeepersCrypt variant was not created by professionals and its structure appeared to have been quite weak. As a consequence, it is now assigned to the group of ransomware infections that have already been solved. A universal tool for decryption, called StupidDecryptor, has been efficiently modified to detect and decipher files that have been affected by JeepersCrypt and got appended with .jeepers extension. It is possible that Perseus Trojan is involved in the distribution of this malware as this is suggested by results that security tools inform victims about.
Description of JeepersCrypt ransomware
JeepersCrypt crypto-virus gives a limited amount of time to make a transaction of bitcoins. In 24 hours, the sum of 0.02 BTC is expected to be transferred to hackers. However, they do not immediately inform victims of the wallet which is to receive the payment. Crooks demand that people would contact [email protected] email address first.
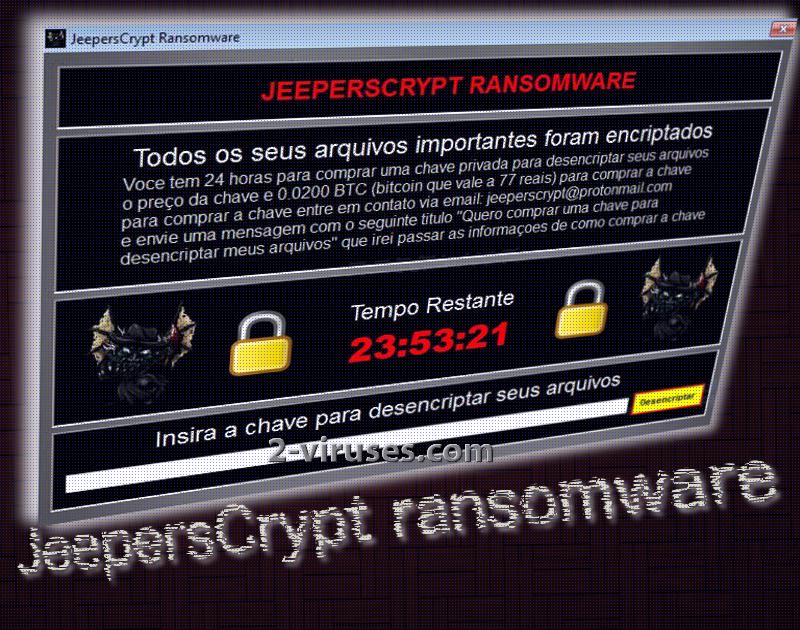
A letter called ‘I want to buy a key to decrypt my files’ is supposed to reach hackers. Since individual victims won’t receive different ID numbers, it is presumably that ransomware uses static keys which will act as universal decryption codes for all infected people. For this reason, it was relatively uncomplicated to solve this sample. We should also mention that JeepersCrypt ransomware does not appear to be extremely greedy as its ransom is only 24.95 US dollars. However, since this sample is easily decryptable, there is no reason to abide by the rules that hackers insist on.
Despite the fact that JeepersCrypt ransomware is not a sophisticated virus, it is still a threat. People might act irrationally and make transactions of bitcoins if they do not search for more information on the Internet. Since this malware blocks access to the computer and displays a ransom note instead, people can be eager to send 25 US dollars and get it over with. Before encryption with ciphers can be successfully executed, it is important that the virus would modify Windows Registry Keys. Entries will be altered so the JeepersCrypt.exe payload would join the list of software applications that get automatically launched after a computer device is rebooted.
We have not been informed about which algorithm for encryption is utilized by JeepersCrypt ransomware, but since it was not a complex variant, we guess that sole AES was employed for the job. However, thanks to poor-skilled hackers, security researchers are able to defeat their ‘masterpieces’. Click here to download the free tool to decrypt all of your data.
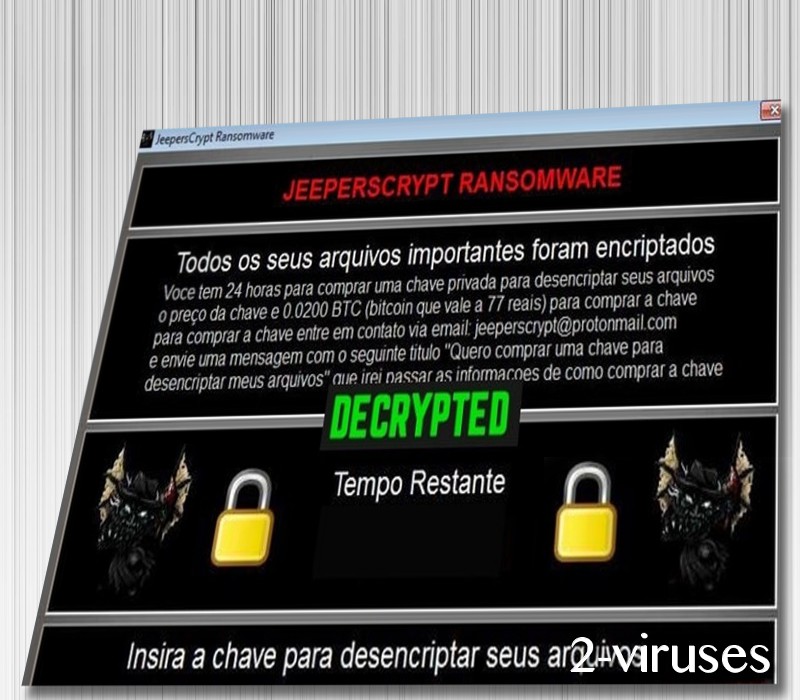
How can I decrypt files that JeepersCrypt ransomware has ruined?
Thanks to competent security analysts, there is a functional tool to restore files that have been appended with .jeepers extension. All you have to do is download StupidDecrypted and run it. However, remember that before you can complete decryption without any obstacles, the infection itself has to be thoroughly removed. For this task, exploit anti-malware tools that will detect malicious executables and offer assistance in their removal. To fight off ransomware, you have to run a device in Safe Mode and then run a full security scan. More information about the possible methods to remove JeepersCrypt virus are mentioned right after this article.
How can I become infected with JeepersCrypt ransomware?
As for the future, please be more careful. It is possible that JeepersCrypt sample could be transmitted via Trojans that appear to be harmless programs, but are actually concealing malicious files. This virus could be found in email letters, containing vile attachments. During your browsing, you should also remember that some websites could turn out to be quite vulnerable to exploit kits. However, if you have sophisticated security tools in your device, malware is more unlikely to harm you. For protection from malware, we recommend using Spyhunter, Plumbytes or Malwarebytes anti-malware tools.
Jeeperscrypt Ransomware quicklinks
- Description of JeepersCrypt ransomware
- How can I decrypt files that JeepersCrypt ransomware has ruined?
- How can I become infected with JeepersCrypt ransomware?
- Automatic Malware removal tools
- How to recover JeepersCrypt ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover JeepersCrypt ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover JeepersCrypt ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Jeeperscrypt virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of JeepersCrypt ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Jeeperscrypt virus. You can check other tools here.Step 3. Restore JeepersCrypt ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Jeeperscrypt virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover JeepersCrypt ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








