Flyper ransomware, just like 8lock8 and EduCrypt ransomwares, has been developed from the source code of Hidden Tear ransomware project. Similarly to the both of the latter cryptomalwares, Flyper utilizes the popular asymmetric encryption algorithm, which is one of the most advanced ciphers recent file-encrypting threats use. While the basics of how this virus operates is going to be revealed in the article, the decryption mechanism is still under development and, unfortunately, cannot be presented. Nevertheless, read to the end to find out other measures you can take to try to get your data back.
About Flyper Ransomware
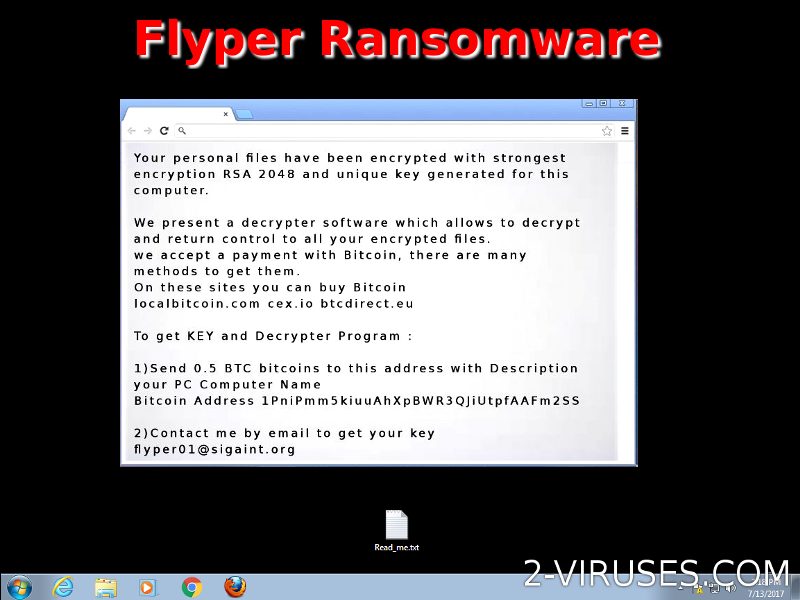
Flyper ransomware encrypts multiple data files. It appends ‘‘.flyper’’ extension to the filename extensions of each encrypted file. For example, ‘‘Photo.png’’ is turned into ‘‘Photo.png.flyper’’. After the encryption has been carried out, ‘‘instruction.txt’’ text file hits every folder of encrypted files with the following message:
0.5 BTC (bitcoins), equaling to 301.45 USD at this particular point in time, is the ransom payment the victim is asked to pay for his (her) data to be retrieved. The unique bitcoin address is 1PniPmm5kiuuAhXpBWR3QJiUtpfAAFm2SS, to which the money, converted to the cyber currency, is to be transferred. The contact e-mail address is [email protected], which serves as the communication tool for reaching out with the hackers, after the ransom money has been transferred to get the private key, which will grant the access to the locked data.
It gives the impression that the cyber crooks behind Flyper crypto-malware were not very concerned with the image of their malicious program or with the message they wanted to convey to, or their attribution to anything. This plain ‘‘You have been hacked!’’ declaration in bright green in the black background is everything they want to tell you.
How is Flyper Ransomware Spread?
Flyper ransomware virus is a malevolent program code, which starts running on one computer’s system, after the victim has opened some infected spam e-mail and clicked on the links embedded or executed the executable file attached to that spam e-mail sent. As you might have understood, Flyper encrypter is distributed through spam e-mail attacks organized by its developers. These attacks are targeted at random users and they are disguised as letters from official institutions such as customs office, etc. The surprise factor triggers the victim to open these e-mails and, eventually, to get one computer’s system infected.
Flyper encoder can also be downloaded on one’s PC by malignant codes such as exploit kits (e.g. Angler, Nuclear, Blackhole, etc.). This particular ransomware virus has not been associated with any exploit so far. But these malign programs are the common distributors of file-encrypting applications. They dwell on questionable sites, such as gaming or freeware sites, etc., or they can even run on legitimate but hacked websites. When, the user visits such web pages of poor destiny, his (her) computer’s system gets infected.
How to Decrypt Files Encrypted by Flyper Ransomware?
As we have already informed you, the community of cyber security researchers are still racking their brains to develop the tool, which would crack Flyper ransomware. In the meantime, you can make use of your external or internal backup. The first one refers to your portable hard disk drives, USB flash drives, etc. The second one refers to the Shadow Volume Copies. Of course, you will not benefit from the both of the latter, if you did not back your data up in either of the mentioned ways. Then, try to apply professional data recovery tools such as Recuva, R-Studio, PhotoRec, etc.
But, first of all, you need to copy your infected drive (if you want to make use from the would-be decryptor by cyber security experts) and remove the malware from your computer’s system. To remove Flyper virus employ powerful tools such as Spyhunter. The removal of ransomwares is a pesky business. Thus, the tutorial for the manual removal for this rogueware, provided below, must be followed carefully and cautiously, as a single mistake may cost you a lot.
Flyper Ransomware quicklinks
- About Flyper Ransomware
- How is Flyper Ransomware Spread?
- How to Decrypt Files Encrypted by Flyper Ransomware?
- Automatic Malware removal tools
- How to recover Flyper Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Flyper Ransomware encrypted files

Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Flyper Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Flyper Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Flyper Ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Flyper Ransomware. You can check other tools here.Step 3. Restore Flyper Ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Flyper Ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Flyper Ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.