Every now and then, shady programmers develop ransomware viruses that are not characterized as particularly greedy. Their course of action might seem smoother, but in fact, they are just the same as other infections that should not be underestimated. New variants are getting released daily and we are working hard to keep you updated with the latest releases. A specific new example has recently gone up to the stage to reveal its identity. The discovered “jewel” can be indicated as Crypto Wire ransomware. Its main objectives include: infiltrating into users’ devices, encrypting files with AES encryption and demanding a quite solid amount of bitcoins in exchange for decryption. Why did we began with the concept that some ransomware viruses do not demand gigantic ransoms? It seemed relevant to us since Crypto Wire virus requires victims to send 0.29 bitcoin. Despite the agreeable number, it is still approximately 200 dollars (to be more exact, 199.35). We are convinced that you will manage to find better ways to spend it. Sending money to crooks is not only wasteful, but also dangerous. Amounts of cash that are delivered to shady programmers can be exploited for further scamming strategies. Basically, by sending bitcoins to the makers of viruses, you are portraying a role of a sponsor and financing the next Crypto Wire virus. However, this ransomware attempts to steal more from the rich part of the society. If payload reaches a computer, belonging to a some sort of company, the demanded ransom is going to be raised.
About Crypto Wire Ransomware
Crypto Wire virus won’t be a pleasant gift to receive. It is wrapped in deceptive paper and tied with a poisonous string. Security researchers were efficient enough to determine some details about this variant quite quickly. Victims that get infected receive a file with a long name: 5684f8b6422ec02116b5ae28480756005e58cd4cfc5701d94fa180ea06de96d6. It is small and almost unnoticeable if you are an amateur in computer technologies. Who would randomly decide to check their computer for viruses manually? Categories that usually contain executables of malware are AppData, Temp, Roaming, Common. Of course, we do not expect you to check these folders on your own. It would be much more understandable to employ anti-malware tools for an automatic scanning.
Let’s move on to the way Crypto Wire virus functions after its successful infiltration into a device. Like any other this type of virus, it has been noticed as the responsible force for files that were strongly influenced by AES algorithm for encryption. After the targeted data begins to be completely unusable, victims will come to a realization that their device has been invaded by an insane ransomware virus. The ruined data will be “marked” with a new extension: .encrypted. Malicious processes will begin immediately after the payload of Crypto Wire virus is dropped. This variant will make it its business to alter your Windows Registry Keys for one specific purpose: so its payload would be able to run and launch processes like scanning for files and later on, encryption. Fundamentally, all of the necessary efforts are put in motion to make Crypto Wire beneficial to its creators. We do not have a lot of information regarding the dispersion of this variant and we cannot strictly say how many victims has this variant influenced. Infection has set its mind on targeting all file types that are most commonly found in users’ devices. Some examples can be found below:
PNG .PSD .PSPIMAGE .TGA .THM .TIF .TIFF .YUV .AI .EPS .PS .SVG .INDD .PCT .PDF .XLR .XLS .XLSX .ACCDB .DB .DBF .MDB .PDB .SQL .APK .APP .BAT .CGI .COM .EXE .GADGET .JAR .PIF .WSF .DEM .GAM .NES .ROM .SAV CAD Files .DWG .DXF GIS Files .GPX .KML .KMZ .ASP .ASPX .CER .CFM .CSR .CSS .HTM .HTML .JS .JSP .PHP .RSS .XHTML. DOC .DOCX .LOG .MSG .ODT
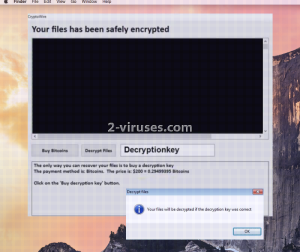
Of course, this is just a small drop of the files that can be selected for the encryption process. AES algorithm can pick from a wider range of extensions than mentioned above. However, there are other criteria for the files to be chosen: it has to be smaller than 30 MB. Surprisingly, encryption is not the only activity to fear from Crypto Wire virus. The remaining data can be be jeopardized in other methods: overwriting or deletion. After the encoding is completed, Crypto Wire will make its existence as clear as day and start demanding money for the decryption. A presented screenshot illustrates appearance of the possibly displayed ransom note.
How is Crypto Wire Ransomware Distributed?
Crypto Wire can explore a number of methods for distribution. It can travel with infectious letters in email inboxes. Before opening a random letter, always make sure that its source is reliable. If email addresses seem quite peculiar, then it would be the best to delete that email or ignore it. However, this is not the only possible method of Crypto Wire virus to be send around. Be very cautious while browsing online since a lot of the online material can be invested in tricking and infecting you. The amount of content that might be infectious is making us continue to forewarn people about it. One wrong step can lead to a ransomware virus or slightly different type of malware.
How to Decrypt Files Encrypted by Crypto Wire?
According to a thorough analysis by security researchers, Crypto Wire virus is very likely to delete Volume Shadow Copies. Of course, you can check if this is really true by following our couple tips below. As for other possible actions of decryption, we can recommend you to test whether universal file-recovery tools would do any good. If not, then you should wait for analysts to figure out a way to crack the codes of Crypto Wire virus. As for the visitors that, luckily, have never encountered a ransomware virus, we can give a couple tips that the situation would remain like this. Always use a powerful anti-malware tool to detect and remove viruses. Spyhunter or Hitman are one of the possible programs to try out.
Crypto Wire Ransomware quicklinks
- About Crypto Wire Ransomware
- How is Crypto Wire Ransomware Distributed?
- How to Decrypt Files Encrypted by Crypto Wire?
- Automatic Malware removal tools
- How to recover Crypto Wire ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Crypto Wire ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Crypto Wire ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Crypto Wire ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Crypto Wire ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Crypto Wire ransomware. You can check other tools here.Step 3. Restore Crypto Wire ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Crypto Wire ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Crypto Wire ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








