Adonis ransomware virus was written while using an Autoit programming language. The primary objective of Autoit was to generate automatic scripts for Windows applications, but over the years, its importance and means of utilization have shifted. We have already analyzed a couple of malware samples that were created with the Autoit language. In this article, we observe a vicious file-encoder.
However, the initial assumption was proven to be incorrect as this ransomware infection does not fully encrypt files. Therefore, it also does not have an original extension which would be appended to executables that get spoiled. We do express concerns that this infection might still be in development. This would mean that a more functional sample will be detected.
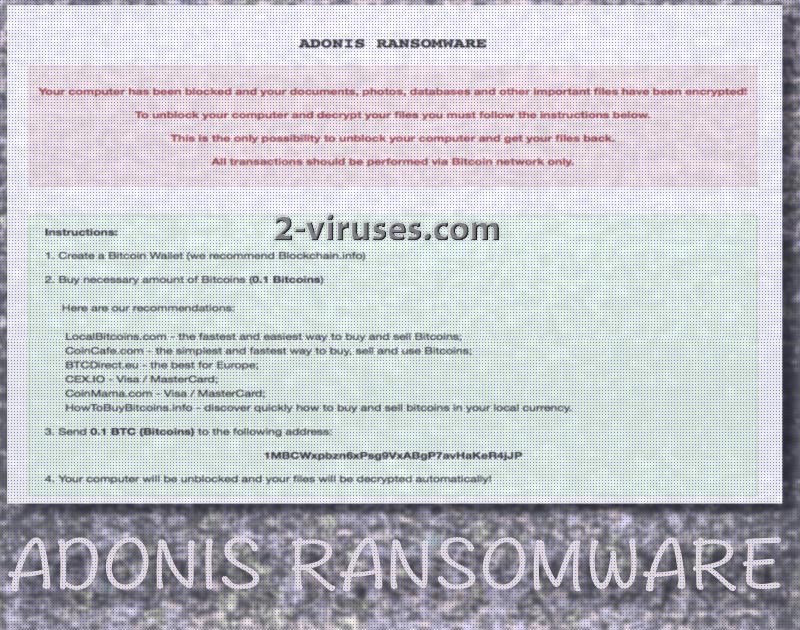
If this ransomware reestablishes its activity, we are sure to inform you about these changes. Even if Adonis virus is improved and starts encrypting files, we discourage users from paying 0.1 BTC which is demanded as the ransom. This sum translates into 225.03 BTC. Obviously you should not waste a cent to follow the rules that hackers have enlisted.
This infection does not point out an email address which should be contacted after that compulsory payment has been made. It is explained that all files will be decrypted automatically. Since no actual encryption takes place, all of these threats are empty. Paying the ransom would be an extremely ill-advised idea as this ransomware infection is a fake one, meaning that it only pretends to encrypt your files while actually, this process is not implemented.
No need to pay, only to remove the infection
To retrieve the control over your device and to clean it from malware, we are encouraging you to get an anti-malware tool which will help with both of these tasks. Firstly, it will initiate a removal of all malicious traces. Then, it will continue to protect you from similar inconveniences in the future. We are recommending Spyhunter or Hitman for these objectives. They will certainly provide the necessary protection.
Even though this specific infection does not encrypt files, there are plenty of those who do. It is extremely easy to catch a malware infection these days: you should protect your digital data before encryption algorithms are applied to them. Store valuable information in backup storages. We can assure that there is a number of facilities to choose from: find the best suited for you. On the other hand, you can make copies of your executables and stored them in USB flash drives. By keeping them safe.
The worst idea would be to pay the ransoms voluntarily. We have to warn you that in most cases, encrypted data remains useless even if ransomware victims do decide to make transactions of bitcoins. This is very unfortunate and we hope that you won’t be tempted to do this, no matter how desperately you might need to access your files. By paying the ransom, you are providing financial support to hackers and making sure that even more variants would be produced in the future.
You should come to terms with the fact that most of the online content could be infectious. You could even face harmful content in your emailing account which could be compromised by spam letters, featuring attachments. These files could specifically be interested in functioning as payloads of ransomware.
For this reason, we are discouraging people from opening random letters and believing their content. It is possible that hackers will send email messages that will pretend to be sent from reputable sources. An additional action to avoid would be visiting domains that provide questionable, illegal services. Peer-to-peer downloads also could bring Trojans into operating systems.
Adonis Ransomware quicklinks
- No need to pay, only to remove the infection
- Automatic Malware removal tools
- How to recover Adonis ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Adonis ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Adonis ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Adonis ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Adonis ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Adonis ransomware. You can check other tools here.Step 3. Restore Adonis ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Adonis ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Adonis ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








