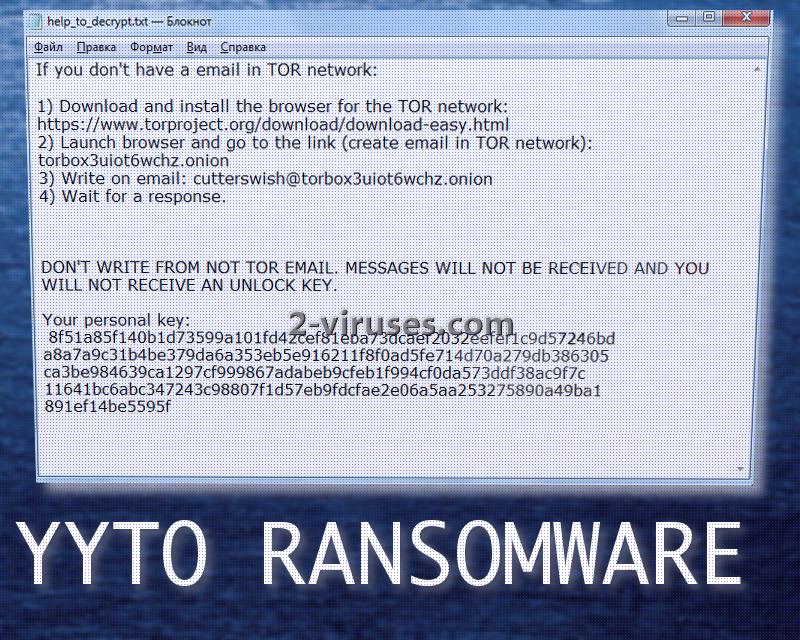
YYTO ransomware virus is a recently-developed ransomware infection and people are already reporting that their personal computers are compromised by this variant. According to the victims who required some assistance, we have been informed that virus does not feature a lock-screen It places two files: help_to_decrypt.txt and read_to_txt_file.yyt that encourage users to download TOR browser and open a website which will load only with this application. Torbox3uiot6wchz.onion transfers users to a concealed mailbox service. Victims are supposed to sign up and write a letter to [email protected] address. It is not explained which information should be included in this email. However, at some point, hackers will require to receive users’ personal keys (included in the .txt file).
The payload of this ransomware is indicated to be this long executable: dbf2973ead796b962bf6f1b2a98a7fc3d6f771417864f757ba7cd27dfa8d2c17.exe. After analyzing this file, we concluded that it attempts to remain undetected with the following processes: queries kernel debugger information and writes to a desktop.ini. Malicious file also contains abilities to collect details about the infected operating system and extracts additional files that have suspicious rights, like abilities to delete other data. It is focused on infecting Windows operating systems.
.YYTO extension is appended to the digital data, ruined by this variant. If your files are currently unusable and this mark is incorporated into them, you should realize that a ransomware virus has managed to invade your computer. The authors do not immediately indicate the ransom, required in exchange of the private key for decryption. It could be that it will differ for individual victims, according to the amount of encoded data.
One of the victims indicated that this virus could be delivered via malicious spam campaigns. It appears that the person received some suspicious letters that pretended to be originating from legitimate companies. The messages contained convincing information and even profile pictures. However, the victim elaborated that the message contained a link to a specific website.
When the mouse cursor was placed on the URL, it showed that the actual destination was completely different than indicated. While attachments are more popular for ransomware-distribution, it is recognized that links, leading to malicious websites, could also be responsible for the infiltration of such viruses.
At the moment of writing this article, security researchers were still analyzing the sample and attempting to find possible methods for file encryption. It might be just a matter of time until a free file decryptor will be released and opt to help those in need. Until then, you could try recovering files differently. For instance, if you have stored you digital files in backup storages or USB flash drives, all you have to do is retrieve them. Only remember that before doing so, you should eliminate all traces of malware from your operating system. It is possible that files could be re-encrypted once you recover them.
For this reason, we encourage you to run a full security scan with Spyhunter or Hitman and see what the results will signal.
We have already explained the suspected way that this ransomware travels, but it could also use other means as well. For instance, it could also deliver email letters with attachments or be automatically delivered once you visit a suspicious website. Stop being reckless and downloading programs or files via peer-to-peer networks because you could have your operating system compromised by malware. Ransomware are the most vicious type of them all as it will prevent you from accessing data and will also have the nerve to require money.
In the last sections of this article, we have explained the manual removal option and other possible techniques of decrypting files. If you are eager to return files back to their original state, you can try the enumerated recommendations. In some cases, they help.
Yyto Ransomware quicklinks
- Automatic Malware removal tools
- How to recover YYTO ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover YYTO ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover YYTO ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before YYTO ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of YYTO ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to YYTO ransomware. You can check other tools here.Step 3. Restore YYTO ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually YYTO ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover YYTO ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.