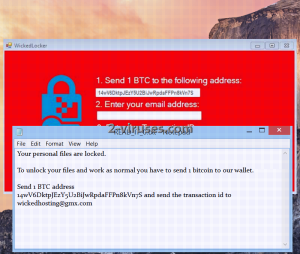
Let us present you a guest that you most definitely were not waiting around for. It is a new crypto-ransomware that threatens the security of Internet users by encrypting files and demanding money for the decryption. It is indicated that files will be functional once again if 1 bitcoin is going to reach the creators of WickedLocker virus. Even if you might think that this agreement has to be followed by both parties, crooks can claim the money and leave your files completely useless. That is why it is always necessary to contact reputable security consultants first and ask for their opinion on this issue. Since ransomware viruses have become an extremely popular trend, analyst are paying more and more attention to their existence and behavior. As for WickedLocker virus, we strongly urge you to continue on reading this article and find the possible methods for the removal and decryption.
About WickedLocker Ransomware
The perfect environment for ransomware viruses to thrive is email inboxes. This is one of the places that you might have caught WickedLocker ransomware. This is a rather stealthy ninja, most usually disguised as a random executable. The payload of the virus can turn out to be a number of things: installer.exe, update.exe or any other seemingly insignificant part of your data. However, main file of WickedLocker virus hides behind an innocent appearance for a very specific reason: to sustain its existence as a secret and to move on to its objectives without interruptions from the user. This variant will go along the same path like any other ransomware and try to reach the necessary points. One of the first modifications are going to be directed to Windows Registry Keys. As WickedLocker virus gets launched with your entire system, it is able to secretively search for files and encrypt them. Security researchers are trying to determine whether AES or RSA encryption is chosen, but the exact cipher is not even that crucial for you to be aware. After the ransomware celebrates victory in encrypting your files, it will add an extension to each encoded file: .locked. It addition to that, users will find a letter of demands as a READ_IT_[number].txt. Do not get tricked into contacting the shady people behind this virus since it won’t lead to a positive outcome. [email protected] is identified as the email address to send questions or concerns. You can forget about begging for your files back since these statements won’t thrill the crooks.
How to Decrypt Files Encrypted by WickedLocker Ransomware?
As we have already indicated, contacting the crooks via the email is a huge mistake. However, paying money for the decryption is even worse. The clever thing to do is to eliminate the ransomware and wait for the decryption to become available with a free program, generated by genuine security researchers. We know that this waiting might seem inconvenient; especially if you require your files to be functional as soon as possible. Despite the inconvenience, you should not forget that paying 1 BTC for the decryption will only allow crooks to continue with their mission of creating ransomware viruses. If victims do not respond to the threats, then it is presumable that after some time, shady programmers will run out of fuel and will have to stop producing so much ransomware viruses. A wish to be immune to these infections is popular idea as well. You can do this by keeping copies of your files in secure storages.
How is WickedLocker Ransomware Distributed?
We have already gave you a small hint about the distribution methods of this variant. Letters that often seem urgent or require your undivided attention are frequently constructed by crooks. If you receive a bizarre message from an Airline company or a notification about a bill, please check if the source of this email is reputable. Crooks construct email address that resemble the original ones, but the difference is most usually clear from the first glance. Delete such letters and NEVER download the attachments inside. It will probably turn out to be just another hoax, crafted to swindle money out of you. If talking about prevention is not the thing that concerns you, we should move to the elimination and decryption. You can run full security scans with Spyhunter or Malwarebytes and remove WickedLocker virus from your sight. Keep the encrypted data safe, until security researchers manage to construct a reliable tool.
Wickedlocker Ransomware quicklinks
- About WickedLocker Ransomware
- How to Decrypt Files Encrypted by WickedLocker Ransomware?
- How is WickedLocker Ransomware Distributed?
- Automatic Malware removal tools
- How to recover WickedLocker ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover WickedLocker ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover WickedLocker ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before WickedLocker ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of WickedLocker ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to WickedLocker ransomware. You can check other tools here.Step 3. Restore WickedLocker ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually WickedLocker ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover WickedLocker ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








