Venis ransomware is another new crypto virus. It has its own payment site at the address venis.pw. Another interesting fact about this ransomware virus is that it creates a user profile on the infected PC. It is believed that Venis file-encrypting malware is still in its developmental phase and, thus, we are going to be introduced with the mature version in the future. It is a typical ransomware trojan, as regards the techniques it is being spread. Though, it also has specific features. Read the post to find them out.
The Distribution Techniques of Venis Ransomware
While the primary means for spreading Venis crypto malware remains the same as that of the other ransomware viruses, that are the spam campaigns, this particular virus is also being distributed by deceptive downloads. To be more specific, the developer of Venis trojan has been spreading the malware on the Internet by commenting in various cyber security forums and presenting the executable .DLL file of the virus as the decryptor for the new version of Cerber ransomware.
This is a whole new approach to the distribution tactics of ransomware viruses, which we have not seen before. It is also a very clever tactics implemented. As a consequence, the Internet users must be painstaking attentive to details, as regards the spam e-mails received or the downloads recommended. It is better to regularly clean the spam folder of one’s e-mail box without opening the e-mails, not to mention the clicking on the links present in them or opening the files attached to them. As concerns the applications recommended, pay great attention to the source or the entity, that provides such recommendations. Check the reputation of the forums and make sure that the individual providing recommendations belonged to the moderators.
The Modus Operandi of Venis Ransomware
The new account profile Venis crypto-malware creates on the infected PC is named TEST. This is done through RDC (Remote Desktop Connection), which is available on the Windows operating system. The malware bypasses the Windows Firewall by adding an exception rule implementing the following command:
→netsh advfirewall firewall add rule name=”Remote Desktop” dir=in protocol=tcp localport=3389 profile=any action=allow (PID: 3796)
Venis crypto-locker uses the standard asymmetric encryption to lock the data files. The types of files targeted are the following:
.csv, .doc, .ppt, .xls, .avi, .bak, .bmp, .dbf, .djvu, .docx, .exe, .flv, .gif, .jpeg, .jpg, .max, .mdb, .mdf, .mkv, .mov, .mpeg, .mpg, .odt, .pdf, .png, .pps, .pptm, .pptx, .psd, .rar, .raw, .tar, .tif, .txt, .vob, .wav, .wma, .wmv, .xlsb, .xlsx, .zip
As the majority of ransomwares, Venis file-encrypting virus appends registry entries so that it will be automatically loaded every time the computer is started. Your desktop will be replaced with the image below, after this virus has infected your PC:
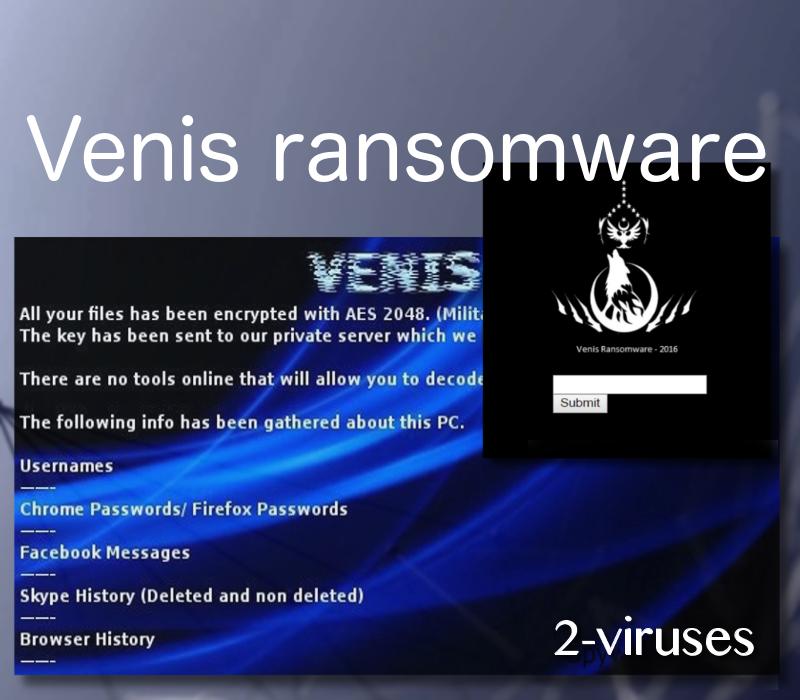
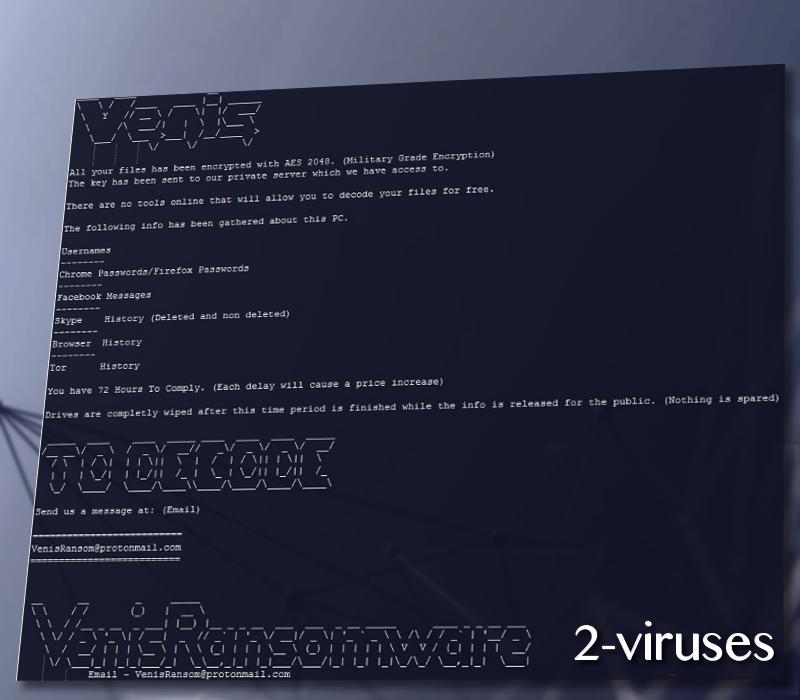
The text of the ransom note:
VENIS
All your files has been encrypted with AES 2048. (Military Grade Encryption)
The key has been sent to our private server which we have access to.
There are no tools online that will allow you to decode your files for free.
The following info has been gathered about this PC.
Usernames
——–
Chrome Passwords/ Firefox Passwords
——–
Facebook Messages
——–
Skype History (Deleted and non deleted)
——–
Browser History
——–
Tor History
You have 72 Hours To Comply. (Each delay will cause a price increase)
Drives are completely wiped after this time period is finished while the info is released for the public. (Nothing is spared)
TO DECODE
Send us a message at: (Email)
==========================
[email protected]
As the coders of Venis ransomware declare, apart from encrypting your drives, their malicious code acts as a spyware as well. They claim that your usernames, passwords, FaceBook and Skype messaging history, your browsing history – all this information has been leaked. And if you do not pay them in 72 hours, all the data stored on the drives, as well as the sensitive and personal information gathered, will be deleted and leaked respectively. The contact e-mail provided is [email protected], which is hosted on the encrypted e-mail service ProtonMail – a popular e-mail service among the developers of cryptomalwares (see Parisher, TeamXRat, etc. ransomware). While the size of the ransom is left to be puzzled out by the user himself by contacting these hackers. Thus, we may speculate that in each particular case the ransom payment may be different.
How to Restore Your Files and to Remove Venis Ransomware?
Venis locker deletes the Shadow Volume Copies, so you have to rely upon your external backup entirely. If you did not think about the creation of additional copies of your data stored on the computer, you can always try to make use from data restore software such as Recuva, R-Studio, etc. In any case, there is a good chance that the decryptor by security researchers is going to be released.
Engage in the above mentioned activities only after the imaging of the corrupted drives and the removal of the virus have been carried out. To remove the malware run Spyhunter or Malwarebytes anti-malware applications. The removal will be achieved faster and no malicious components will be left on the system. The manual instructions are to be found below.
Venis Ransomware quicklinks
- The Distribution Techniques of Venis Ransomware
- The Modus Operandi of Venis Ransomware
- How to Restore Your Files and to Remove Venis Ransomware?
- Automatic Malware removal tools
- How to recover Venis Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Venis Ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Venis Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Venis Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Venis Ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Venis Ransomware. You can check other tools here.Step 3. Restore Venis Ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Venis Ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Venis Ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








