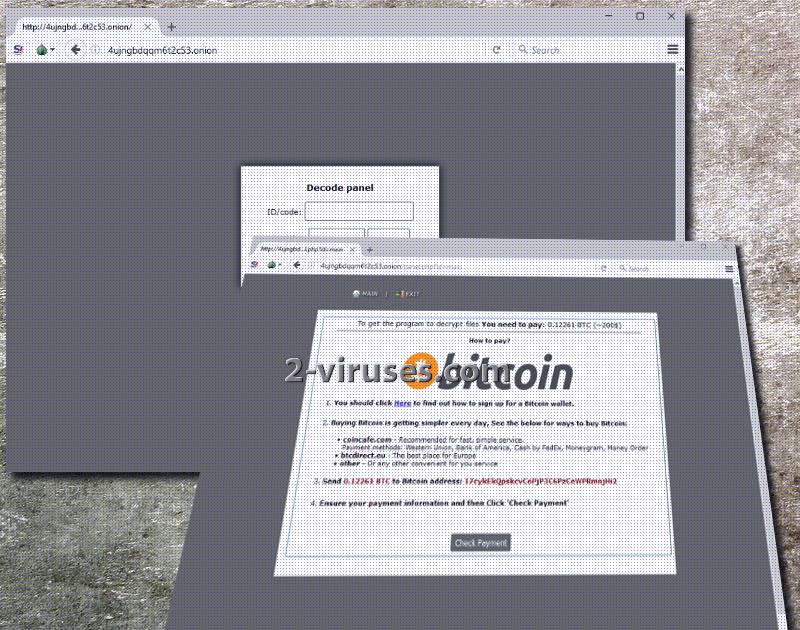
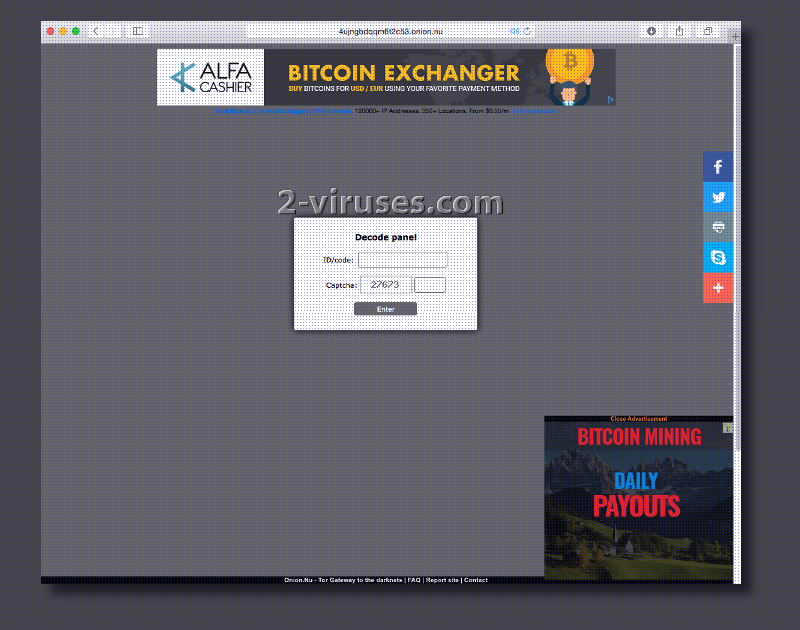
A new UIWIX ransomware has been crafted and aspires to be a moneymaking variant. UIWIX virus controls a website, designed to open up via a TOR browser. Once users enter the domain, a panel will require victims to log into the site with an ID number and re-write the displayed captcha. Then, a page with explicit instructions will appear, from which we derived that this infection requires 0.12261 BTC (224.76 US Dollars) as the ransom for file-decryption. The payment is supposed to reach 17cyklEkQpskcvCoPjP3C6PzCeWPRmnjHi2 bitcoin wallet. This sample is currently active as users have already reported cases when executables were encoded and appended with a unique extension. ._[ID Number].UIWIX is the ending, seen in files that have become impossible to launch.
Distinctive features of this crypto-virus
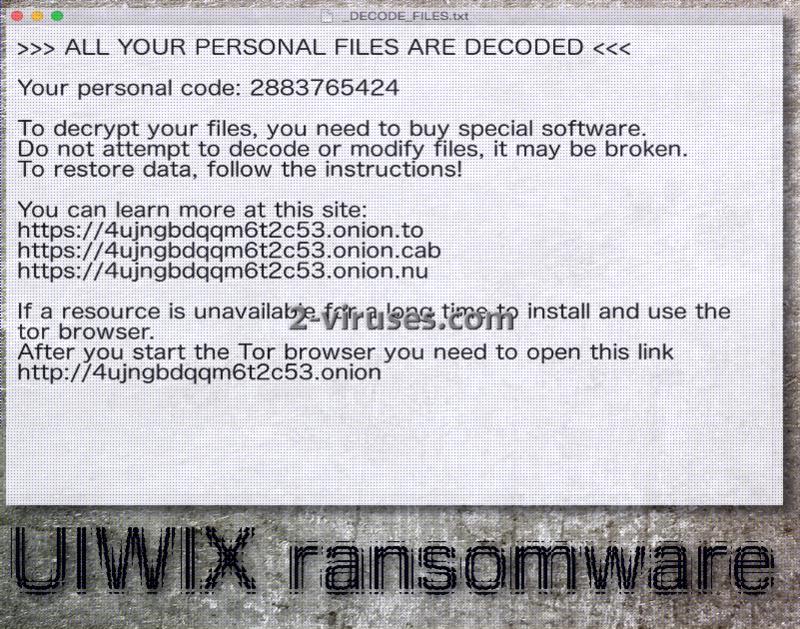
Authors of UIWIX ransomware variant selected AES algorithm for encryption to spoil data. An exact executable that would be indicated as the malicious payload is not yet determined. However, a hidden file that executes detrimental activity is usually named as an ordinary executable. It slips entries into Windows Registry Keys and hopes to remain undetected until encryption process is concluded. After ransomware successfully withholds digital data from being used, a file _DECODE_FILES.txt will be noticed on computer desktops.
In this .txt file, victims will be instructed to perform two procedures. First of all, they should download TOR browser, but this is not completely necessary. There is a link 4ujngbdqqm6t2c53.onion.nu which will load on Safari, Google Chrome or any other browser. From whichever application you access the website that hackers control, its content will be identical. It will contain information about how a transaction of bitcoins has to be made. However, we do not recommend completing instructions that are indicated.
Recognizing an activity of a ransomware infection is quite difficult. Processes are usually done in a secretive manner, attempting to conceal the presence of a crypto-virus for as long as possible. Since its process could be hiding behind a regularly-looking name, you won’t immediately diagnose it as malicious. However, you should still check your Windows Task Manager and try to find currently running processes that seem suspicious. Your only other option is to have a sophisticated security tool that will pinpoint the infection before it is already too late.
To detect a malicious Trojan infection, you are advised to run a security scan with a top-notch security software. Spyhunter or Malwarebytes will help you to recognize malicious activity in an operating system. Before you attempt to restore files, you should get rid of this infection. According to victims after receiving the .txt file with instruction, they removed all of the malicious processes. Encrypted data appeared to have been unaffected by this removal.
File-recovery options
UIWIX ransomware could perform commands that would result in deletion of Shadow Volume Copies. You should check whether these copies remain intact. Additionally, try tools that are able to help victims of different ransomware samples. They might not work, but it is worth a shot. Dealing with encrypted data is difficult. If you wish to have a fast solution, we insist that you upload your data in backup storages. These services will prove themselves convenient if a ransomware infection strikes. Furthermore, you could simply store files in USB flash drives and this will also be a good solution.
How does ransomware infect operating systems?
One of the most popular methods for ransomware distribution is malicious spam campaigns. Deceptive letters that contain a payload of a crypto-virus is very frequently selected as the preferred strategy. However, this is not the only way to become infected. For instance, you could be exposed to infectious content in social networking sites. Additionally, ransomware can be spread via exploit kits, misleading advertisements and other online content.
Uiwix Ransomware quicklinks
- Distinctive features of this crypto-virus
- File-recovery options
- How does ransomware infect operating systems?
- Automatic Malware removal tools
- How to recover UIWIX ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover UIWIX ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover UIWIX ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before UIWIX virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of UIWIX ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to UIWIX virus. You can check other tools here.Step 3. Restore UIWIX ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually UIWIX virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover UIWIX ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.