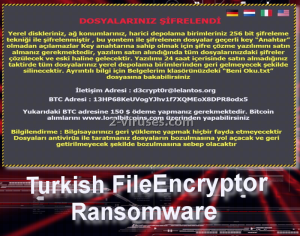
Just last week we encountered a novel crypto-virus that chooses its victims from Turkish-speaking countries, but can display its main message in other languages like German and English. Inspiration to create this variant might have derived from the older CTB-Locker infection. The main message (lock-screen) that both of these variants display appear to have some evident similarities, but this is where the association ends. Turkish FileEncryptor virus is after 150 US dollars and will expect people to voluntarily hand this fee over. In the ransom note, it is explained that victims have to send the appropriate amount of bitcoins (according to the current currencies, 0.14792 BTC). It is also indicated that AES of the length of 256 bits will be applied to data. Corrupted files are also supposed to feature an .encrypted extension, clearly showing which executables were ruined. To our knowledge, filenames are left as they were.
Basics about Turkish FileEncryptor ransomware
Turkish FileEncryptor was named like this because of the file it launches after arriving into devices. FileEncryptor.exe is expected to initiate and complete encryption of valuable data. From taking a look at the table that gets opened, we guess that it is possible that RSA algorithm can be involved in the proceedings of Turkish FileEncryptor virus. This variant appears to feature a lock-screen which shows the image, similar to the one of CTB-Locker.
Users are discouraged from restarting their devices and attempting to recover their files or remove the ransomware. All of these efforts are explained to end in a permanent loss of files. However, paying a ransom is not an option as well as hackers might ignore their victims after payments are send to indicated bitcoin wallets. In this case, hackers require to receive profit in this account: 13HP68KeUVogYJhvlf7XQMEoX8DPR8odx5.
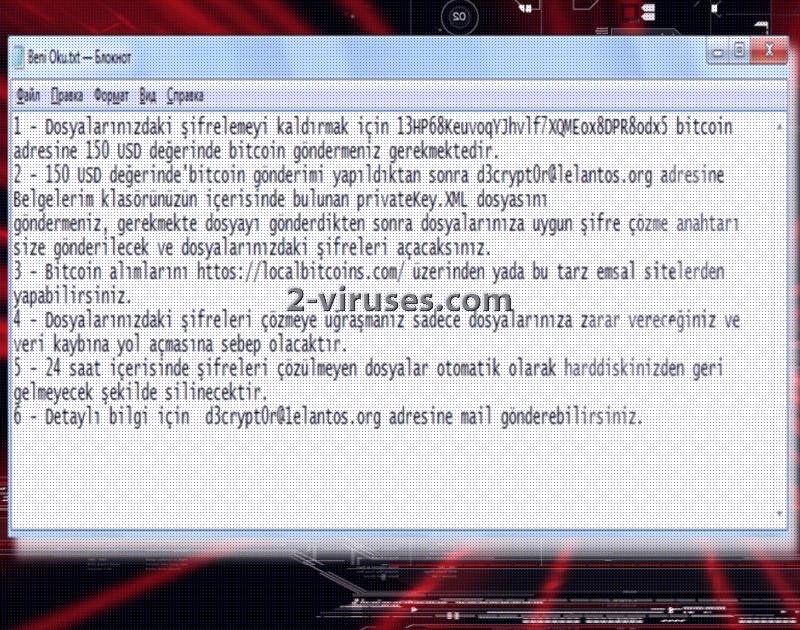
Hackers also indicate an email address in case victims wish to inform them that the payment has been made or to contact them for any other reason. The lock-screen is not the only note that Turkish FileEncryptor virus leaves: it also inserts a .txt file called Beni Oku.txt which means Read me.txt. Before running encryption in full speed ahead, ransomware has to insert entries in Windows Registry keys for the sake of moving on to its main objectives.
As we have already mentioned in the introductory paragraph, .encrypted extension is added to every file that becomes a ruined by AES cipher. If access to your device is blocked and you notice the lock-screen above, there is no doubt that you have caught a TurkishFileEncryptor ransomware. Since it displays buttons, translating the ransom note in other languages, virus can be aiming to influence people from multiple countries.
Restoring files that Turkish FileEncryptor ransomware ruined: is it possible?
With the amount of ransomware viruses that are released every week, security researchers have a difficult time addressing each and every threat. For now, Turkish FileEncryptor ransomware is not decryptable, but we are hoping that a free tool with be released. We are unaware whether this variant is distributed very eagerly, but it if is, this might speed things up in creating the decryptor. Until now, we advise you to try other file-recovery options. Of course, victims might be scared to try them out as hackers indicate that every attempt might end in losing all of the files. How can you escape this fate? After rebooting your device in Safe Mode, you should immediately copy all of your files and place them in a secure location. Then, proceed to remove the ransomware. This can be done with reputable anti-malware tools. It is crucial to firstly remove the infection, and only then proceed to the file-decryption. Spyhunter or Malwarebytes will help you to remove Turkish FileEncryptor virus. Ways to recover files can be found in the sections above.
How does Turkish FileEncryptor virus reach computers?
Payload of a Turkish FileEncryptor virus can be found in spam letters that are sent from bizarre sources. Most of the time, hackers attempt to write letters that would allegedly discuss important affairs. However, you should always be attentive and never open email letters that appear unreliable. To make sure that a letter is not a scam, always look at the email address it originated from. It is usually easy to determine whether it is legitimate or not. In addition to that, ransomware could be delivered via exploit kits. Therefore, try to avoid unknown websites.
Turkish Fileencryptor Ransomware quicklinks
- Basics about Turkish FileEncryptor ransomware
- Restoring files that Turkish FileEncryptor ransomware ruined: is it possible?
- How does Turkish FileEncryptor virus reach computers?
- Automatic Malware removal tools
- How to recover Turkish FileEncryptor ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Turkish FileEncryptor ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Turkish FileEncryptor ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Turkish FileEncryptor ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Turkish FileEncryptor virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Turkish FileEncryptor ransomware. You can check other tools here.Step 3. Restore Turkish FileEncryptor ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Turkish FileEncryptor virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Turkish FileEncryptor ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.