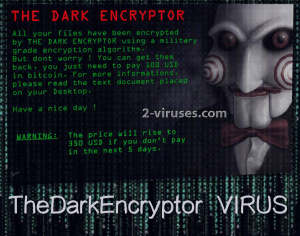
TheDarkEncryptor ransomware virus is a sample that integrates a picture of a notorious Jigsaw, also known as Billy the Puppet. The virus explains that the encryption process is done with a military grade encryption algorithm: we guess that it is either one of the ciphers of AES or RSA. A screen locker is also triggered and the face of Billy accompanies the preliminary instructions for victims. The .tdelf extension should be appended to all encoded executables.
They are advised to access either a .txt or .html file, placed on the desktop. It is supposed to contain more information, like the exact bitcoin wallet of hackers. At first, the demanded ransom is 100 US dollars which equals 0.03572 BTC (bitcoin payment system is required to be used for the transaction). However, if for the next five days (after receiving the demands) victims have not yet completed the terms, the ransom will be increased to 350 US dollars. This equals 0.12500 BTC.
A RansomWare.exe file has been labeled as the payload of this crypto-virus. It will presumably extract additional files into infected operating system and create favorable conditions for the ransomware to thrive. The optimum system should have its Windows Registry Keys modified and anti-virus programs, if present, weakened.
After algorithms for encryption are applied to various types of digital files, users won’t be allowed to run them. Important documents, presentations, articles, precious memories in forms of photos and video material can be corrupted by the TheDarkEncryptor virus. Regardless of how desperately you might need your files, paying the ransom is never the right solution. We can recall a number of instances when the ransoms were obediently paid, but hackers were unable to decrypt files or disappeared after receiving the money they were after.
Therefore, even if you do send bitcoins to the indicated wallet, your files could remain in the same idle state. It is better to try to restore files in ways that do not cost a cent. If this variant begins to severely damage users’ files and infecting a number of victims, security researchers will attempt to find a free solution. For now, this sample has not been reported in action.
Decryption options, removal and transmission of crypto-viruses
There are several tricks that could be exploited for a free recovery of files. One of them is the option of restoring Shadow Volume Copies. Most of the creators of ransomware program viruses to delete these copies. However, not all variant carry such a command: you should check whether the investigated virus does. On the other hand, you could try to restore encoded digital data with tools that have already been generated for this purpose.
One of the best solutions is to store files in multiple locations. If one of them becomes unavailable or corrupted, you will be able to retrieve files from the alternative source. Since ransomware infections are booming, it would be very beneficial to place valuable digital information into online backup storages or at least in USB flash drives.
Before you start completing either one of these strategies, you should remember that the crypto-virus has to be eliminated first. You can do this by running a scan with a powerful security tool. Spyhunter or Hitman should be able to find all sources of malicious activity and delete them.
For more information about the manual removal and alternative decryption options, you should look at the very end of this page. Every single one will be discussed in more depth.
Now, we should address the last important topic: distribution of ransomware. The latter infections usually arrive in devices from various emailing services. There is a very good chance that hackers will commence campaigns of malicious spam. Such deceptive email letters could be delivered to random accounts: be careful not to download attachments or follow links that are found in letters from unknown senders.
Thedarkencryptor Virus quicklinks
- Decryption options, removal and transmission of crypto-viruses
- Automatic Malware removal tools
- How to recover TheDarkEncryptor virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover TheDarkEncryptor virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover TheDarkEncryptor virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before TheDarkEncryptor virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of TheDarkEncryptor virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to TheDarkEncryptor virus. You can check other tools here.Step 3. Restore TheDarkEncryptor virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually TheDarkEncryptor virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover TheDarkEncryptor virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.









