TeamXRat (or Xpan, the earlier version is called Xorist) ransomware is no longer a threat. The cyber security researchers of Kaspersky Lab have managed to decrypt this cyber bug. It was detected as Trojan-Ransom.Win32.Xpan.a and PDM:Trojan.Win32.Generic. This cryptomalware was developed by Brazilian hackers, who call themselves TeamXRat or CorporacaoXRat (CorporationXRat in English). TeamXRat ransomware virus is aimed at the local companies and hospitals, as well as individual users. It utilizes the asymmetric AES-256 encryption algorithm in CBC (Cipher Block Chaining) mode. The previously employed TEA (Tiny Encryption Algorithm) was abandoned.
About TeamXRat Ransomware
The latest version of TeamXRat ransomware is written in C++ and uses STL as a console application, which is deleted after the encryption has been implemented. The program is packed in the UPX executable packer. It appends the following registry entry – HKLMSYSTEMCONTROLSET001CONTROLNLSLOCALE – to check the default language of the system. It can be assumed that the program code was designed to first detect whether the default language is Portuguese and, then, decide, whether to encrypt the data stored on the system or not. TeamXRat encrypter also deletes Proxy settings located in HKCUSOFTWAREMICROSOFTWINDOWSCURRENTVERSIONINTERNET SETTINGSZONEMAP.This may be done to block access to certain web servers or for anonymity purposes, or both.
There will be no doubt, whether your computer is infected with TeamXRat file-encrypting virus or not. Following the installation of this cyber threat and its successful encryption of your data, your desktop wallpaper will be replaced with the following image file:
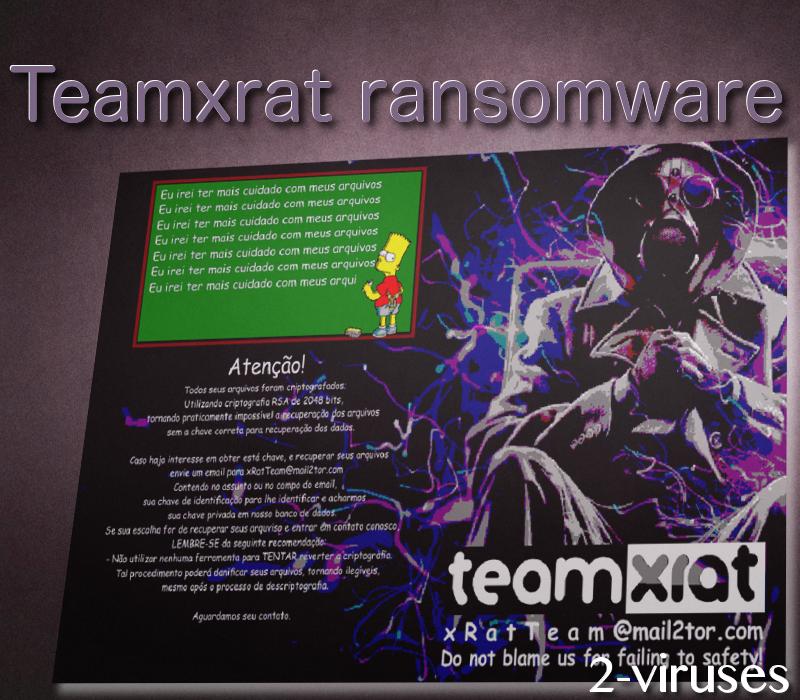
The files targeted will be any files except from .exe and .dll files, as well as certain blacklisted files. The filename extension appended to these files is: ___xratteamLucked. Como descriptografar os seus arquivos.txt (How to decrypt your files.txt in English) file of the ransom note, when opened using msg.exe, discloses such ransom message in Brazilian Portuguese:
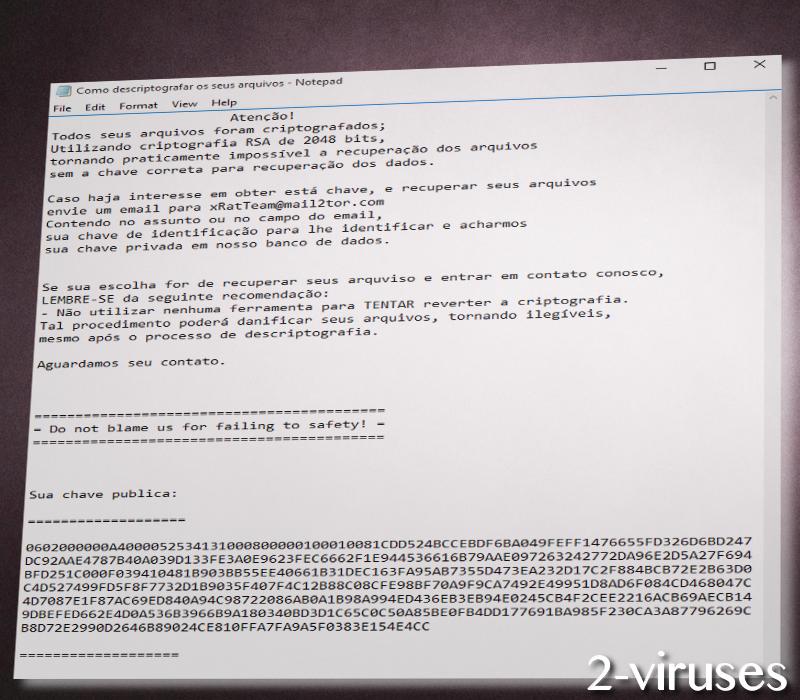
The contact e-mails provided are [email protected], [email protected] or [email protected]. [email protected] contact e-mail, provided by the earlier versions of the ransomware, is currently inactive. The active e-mails are supposed to be used for contacting these hackers to pay the ransom of 1 BTC (bitcoin), which is 604.76 USD, as of the moment of writing this article. The public RSA-2048 key, which is of MSBLOB format, needs to be sent to receive the instructions for payment. The crooks call it a donation you are supposed to donate for their, indeed, good deed carried out so that you increase your cyber security in the future.
How has TeamXRat Ransomware Infected Your Computer?
TeamXRat crypto malware is installed manually via hacked RDP (Remote Desktop Protocol) and, after its successful installation and encryption performed, it is also manually cleaned up from the system. Brute force RDS attacks are more likely to occur on remote desktop servers which are ‘‘protected’’ by weak passwords and which have MS15-067 and MS15-030 vulnerabilities in the RDP protocol. When such an attack has taken place, the antivirus software of the system is instantly disabled and the infection gathers momentum.
How to Decrypt Files Encrypted by TeamXRat Ransomware?
As we have said at the beginning of the post, the Kaspersky Anti-Ransom team was able to crack the code of TeamXRat malicious program. Contact the technicians of Kaspersky at their support page support.kaspersky.com. We cannot give you a word of honor, but the decryptor is likely to be free, as this security software provider has a history of releasing free decryption tools for decrypting ransomware threats. The decryption tool is not available publicly so that the developers of TeamXRat virus will not be able to see the flaws of the source code of their program and, consequently, would not be able to fix them. So copy your infected files and apply Spyhunter or Malwarebytes professional antivirus software to remove TeamXRat trojan from your PC. If you are willing to perform the elaborate task yourself, follow the manual removal instructions posted below.
Teamxrat Ransomware quicklinks
- About TeamXRat Ransomware
- How to Decrypt Files Encrypted by TeamXRat Ransomware?
- Automatic Malware removal tools
- How to recover TeamXRat Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover TeamXRat Ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover TeamXRat Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Xpan Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Xorist Ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to TeamXRat Ransomware. You can check other tools here.Step 3. Restore Xpan Ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Xorist Ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover TeamXRat Ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








