Smash! Ransomware is a new malicious program detected by MalwareHunterTeam. It uses the imagery from Super Mario Bros, a platform video game by Nintendo, namely, the image of the Super Mushroom, holding a knife. Though it calls itself a ransomware and acts in the ransomware-like manner, it cannot be regarded as one of the most dangerous cyber threats that ransomware viruses are. Smash! virus can still be called a developmental version at best. It would be incorrect to name it a crypto-locker, crypto-malware or file-encrypting virus, as neither it encrypts files nor locks them. Smash! malware in its current version can be most accurately named a screen locker.
How does Smash! Ransomware Operate?
Once, the payload of Smash! Ransomware has been downloaded on the compromised computer, the victim is displayed six welcome pop-up windows, which appear one after another. These pop-up messages contain the following greetings:
Welcome
Hi and welcome toWelcome
Smash! RansomwareWelcome
I thought i would lay here all alone.Welcome
But now…Welcome
Your are here!:)WeHSnX
So Welcome to HELL. Pay or your files die!
All these pop-ups have the OK button at the right bottom corner. If you hit the OK button on the last pop-up, you will be shown another pop-up message, which stands as a kind of ransom note. The pop-up is the following:
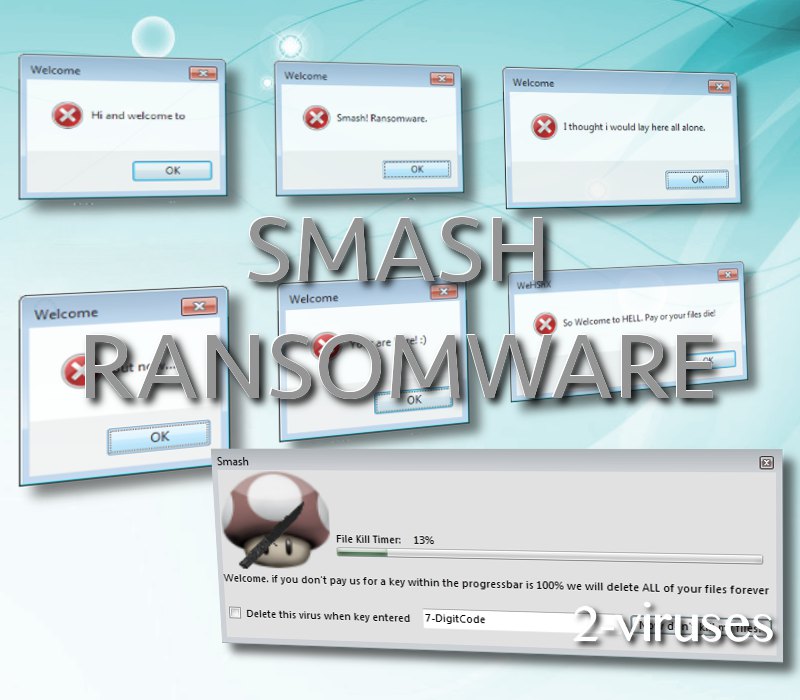
As you can see from the window, you are asked to enter a seven-digit code to supposedly get rid of the virus. There is also the File Kill Timer above the code field, next to the picture of the Super Mushroom. But, as strange as it is, you are not provided with any instructions on how to make the payment required. No bitcoin address, no contact e-mail, nothing.
Furthermore, many functions of Smash! virus are not coded. That is to be said about he function of the Now don’t kill my files! button, which is inactive. This function is empty:
private void Button1_Click(object sender, EventArgs e)
{
}
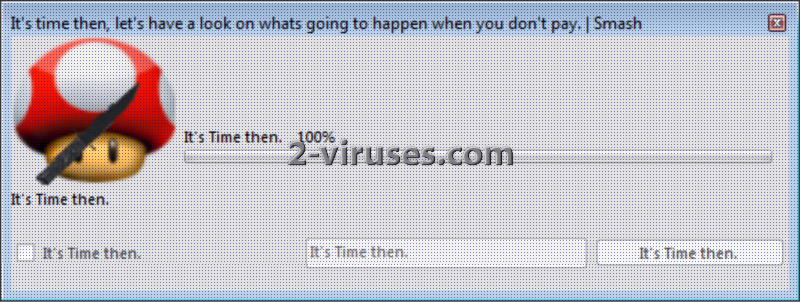
When the progress bar reaches 100%, another pop-up window is opened. This screen contains another timer, which supposedly indicates the amount of files having been deleted. The pop-up is the following:
While, in reality, none of your files is being deleted. It is merely a false warning. Yet this malware application does have some malicious features. Smash! virus can block the certain programs: Regedit (the Windows Registry Editor), the Task Manager and CMD (Command) Prompt. Again, the virus will display pop-up messages, if you try to run the above specified applications. These pop-ups will state the following:
Taskmgr not available.
No TaskManager for you.Regedit not available.
No Registery Editor for you.
How to Remove Smash! Ransomware?
It is not difficult to tackle with Smash! Ransomware. You can simply restart your computer, as this virus does not have an autostart function to be loaded when you have rebooted your PC. Nevertheless, the malicious elements of the program still remains on the system. Thus, you need to remove them. The tools, which can clean the system are the following: Spyhunter. These are top rated malware removal utilities, thus, the software which we can recommend the most. The manual removal of ransomware constituent parts can be executed by reading the guide, which follows the post.
How is Smash! Ransomware Spread?
The ways and means of the distribution of Smash! malware are still obscure. However, it is the most likely that this malware is the upshot of interacting with spam e-mails, malicious advertisements and visiting compromised domains. How to know, which e-mails should be opened and which not, which ads should be followed and which not and which websites can be visited and which not? There is no need for extensive explanations. Spam e-mails must be regularly moved to trash, advertisements are to be ignored, and such sites as that of the torrents, adult content, free gaming sites, etc. are better to be passed around. Cannot resist the temptation? You will have to deal with the consequences.
Smash Ransomware quicklinks
- How does Smash! Ransomware Operate?
- How to Remove Smash! Ransomware?
- How is Smash! Ransomware Spread?
- Automatic Malware removal tools
- How to recover Smash! Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Smash! Ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Smash! Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Smash! Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Smash! Ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Smash! Ransomware. You can check other tools here.Step 3. Restore Smash! Ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Smash! Ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Smash! Ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








