SkyName refers to a crypto-ransomware sample, targeting people from Czech Republic or other locations that might be using Czech language over others. It is possible that upon slithering into a device, a payload of SkyName virus is going to check whether Czech language is set as the preferred one. If it is not, it is presumable that the payload might simply delete itself, no harm done. IT specialists identify that this variant is not fully prepped. Therefore, it is possible that hackers are still going to initiate alterations to the detection version, fix glitches or strengthen the encryption process. SkyName is a crypto-nightmare, which is assigned to a category of those infections that are based on HiddenTear project. Due to this feature, we can assume that SkyName is going to encrypt data in ‘/test’ directory, exploiting AES encryption cipher in this process. Even though the primary goal of this project was to educate people about ransomware that did not stand in the way of hackers taking advantage of it. SkyName virus will hold users’ files in their control and it will be dealt in accordance with every whip of the hackers that originally designed SkyName.
A detailed characterization of SkyName ransomware
A general information about SkyName ransomware was mentioned in the paragraph above: but there are more details that should be explained. Surprisingly, some feature contradict the ones we have indicated the paragraph before. For example, we mentioned that SkyName is not completely finished and hackers might make some modifications to it. One of the issues that programmers are going to intend to fix is the encryption which does not seem to be functioning properly. What does it mean if a ransomware virus cannot pursue its main goal (encryption)? Then, it becomes useless since hackers are not able to create a leverage to take advantage of. Threats that are made in the ransom table won’t be frightening if not a single file is ruined by AES algorithm. However, this release of SkyName might have been a practice run, attempting to help hackers form a strategy, bound to be successful.
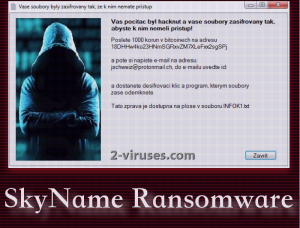
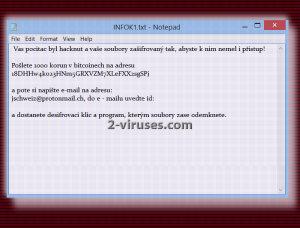
First modifications that SkyName virus initiates in your system won’t be evident. A mere modification in your Windows Registry Keys is not easily noticeable. For this reason, you might not be aware of the fact that the payload of this variant is going to run in the background. During this stealthy stage, virus will scan your system for files that contain extensions, targeted by the sample. For now, we have no knowledge about an extension that would be appended to the encrypted data, since ransomware does not affect files. This might be just a temporary phase and hackers are attempting to fix this glitch as we write this article. We are sure to inform you if there are any changes to this variant and if it begins to be more of a threat to the Internet users. For now, if you get infected with SkyName, you are advised to simply delete it. This is a rough translation of the ransom note:
Your computer was hacked and your files are encrypted so you can access them and did not have access!
Send 1,000 crowns in Bitcoin address
18DHHw4ko23HNm5GRXVZM7XLeFXX2sgSPj
Then you and your e-mail address:
[email protected] to e – mail ID specified: [Redacted] and get the decryption key and program, which in turn unlock files.
The report is available on the desktop file INFOK1.txt
To decrypt or not to decrypt: that is question about SkyName ransomware
Since IT specialists have emphasized that this variant does not actually encrypt files, there is nothing to discuss in this part of the article. However, we are doubtful whether this is the way things will stay: hackers might fix encryption and spread SkyName virus again. Before that happens, you should be prepared. So you could retrieve files, you should upload them into backup storages that are extremely helpful to Internet communities. If a ransomware virus happens to jeopardize your data, it won’t pose as a threat since you will be able to restore files from a backup location. In case SkyName becomes fully functional, the hackers demand 1000 korun for the decryption. Of course, this transaction would be made via bitcoin payment system.
What strategies does SkyName select for distribution?
It is presumable that SkyName virus selects tactics for distribution that are fairly common among such infections. Infectious spam campaigns can be initiated to spread the payload of this variant. If you happen to download an attachment from a questionable email letter, you might jeopardize your device without even realizing the possible consequences. While accessing your inbox, you should bear in mind that your email might be targeted by creators of ransomware. Always judge a received letter before opening it or downloading a file inside it.
Spyhunter or Hitman are the names that you might not be familiar with. However, you should be. Having a reliable anti-malware tool is a necessity when it comes safe browsing. Run regular security scans with these tools. If you infected with SkyName virus, run a scan to detect and remove it. More information about removal can be found below.
Skyname Ransomware quicklinks
- A detailed characterization of SkyName ransomware
- To decrypt or not to decrypt: that is question about SkyName ransomware
- What strategies does SkyName select for distribution?
- Automatic Malware removal tools
- How to recover SkyName ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover SkyName ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover SkyName ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before SkyName ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of SkyName ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to SkyName ransomware. You can check other tools here.Step 3. Restore SkyName ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually SkyName ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover SkyName ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.