A belief that only a mature professional can design a crypto-ransomware virus is not always the case. Samples like Roga virus is one of those infections that should have spent more time in the work-shop before actually getting released to spread terror. It is not a complicated ransomware example since it can be solved with a single phrase. Well, maybe suggesting that this ransomware is completely figured out is not a truthful statement. We can fully assist you in getting rid of the lock screen that appears after the infection has successfully implemented modifications to your system. However, the retrieval of files is another subject. For a more detailed explanation about this infection, please continue on reading our article.
Facts about Roga ransomware and the things it does
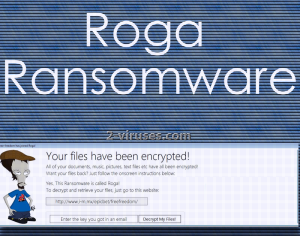
Even if Roga virus would not be featured in a ground-breaking news article, it is still a threat and might disturb Internet users and distract them from other activities. Nobody wants to have their files encrypted, and paying money for decryption is an extremely impractical way to spend money. If you happen to be stuck in a situation in which Roga virus is trying to dominate, you should be prepared to exploit a reliable anti-malware tool and eliminate the threat. It is not determined whether Roga virus’ encryption is fatal to the files. However, it is confirmed that it appends a quite unusual extension to the encrypted data to make it stand out from the rest of the files. .madebyadam is the addition that every encrypted file receives upon becoming corrupted. After removing the ransomware infection from your system with an anti-malware tool, you can attempt to run these files. It is possible that the infection is only going to append the extension and leave files somewhat functional. A bigger threat is the lock screen which does not allow you to check anything. A screen that gives some information about the issue is seen below and you can notice that the creators are being quite cocky about their ransomware.
All of your documents, music, pictures, text files etc have all been encrypted! Want your files back? Just follow onscreen instructions below:
Yes, this ransomware is called Roga!
To decrypt and retrieve files, just go to this website:
http://www.i-m.mx/epicbet/freefreedom/
Enter the key you got in an email
Decrypt My Files!
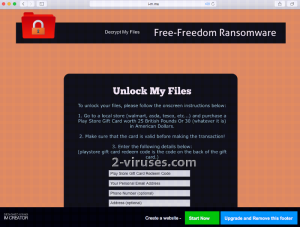
You do not need to find a difficult solution to this screen locker: you simply should type in “adamdude9” and this should help your system fully load. After this, you can check whether your files have been encrypted and whether you are obligated to tryout one of the recovery methods. You can find more about these solutions below. Guidelines include retrieval of Shadow Volume copies or recommendations to utilize universal file-recovery software. Lastly, we should mention that Roga virus seems to be a newer version of Free-Freedom ransomware since in the ransom note, there is a link which leads to a website, related with Free-Freedom.
Decryption of files only costs 30 dollars: can I trust Roga ransomware?
Of course not. You can never put your fate in the hands of hackers as they might disappear without a word. Once they receive the money, there is no need for them to stick around. They won’t feel obligated to professionally restore your data because – guess what – it is not their primary concern. Even though Roga virus seems to require a surprisingly tiny amount of money for decryption, you should not make a deal with the devils behind this infection. We are sure that you are going to get scammed. Even if you don’t: your payment will be taken as a sign of weakness. The more people give in to the powers of shady programmers, the more ransomware infections are going to get released.
How can Roga ransomware reach my device and affect my files?
It is presumable that Roga virus chooses custom methods for distribution. It can be spread in a form of a seemingly harmless executable which is going to be added to a misleading email letter. If you happen to spot a bizarre message in your inbox, make sure that it is legitimate before opening it. Hackers’ spelling is often full of errors that are easily noticeable. In addition to that, hackers might try to gain remote control over your devices and install the payload themselves. In any way, you should keep your system well-protected with anti-malware tools. Spyhunter or Hitman are the programs, capable of eliminating Roga virus so you could move on to the attempts to restore your files.
Roga Ransomware quicklinks
- Facts about Roga ransomware and the things it does
- Decryption of files only costs 30 dollars: can I trust Roga ransomware?
- How can Roga ransomware reach my device and affect my files?
- Automatic Malware removal tools
- How to recover Roga ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Roga ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Roga ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Roga virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Roga ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Roga virus. You can check other tools here.Step 3. Restore Roga ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Roga virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Roga ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.