Reyptson ransomware virus has come to infect Internet surfers and take their digital files as hostages. AES-128 cipher is utilized against users’ executables and after the file-encoding is concluded, the content of documents, photos, videos and other material becomes damaged to the point that it is not identifiable from previous encounters.
Research about this cryto-virus
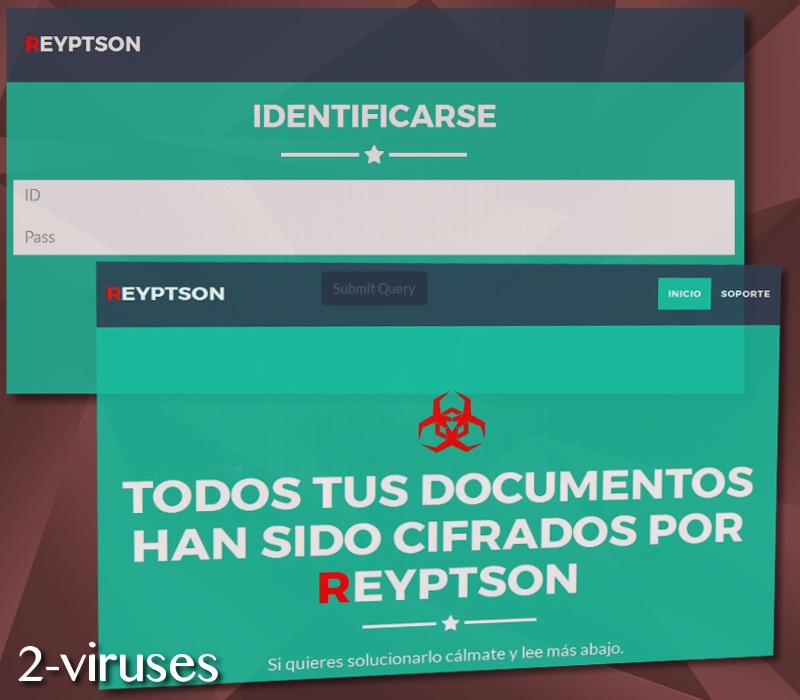
The authors of this infection could be Spanish hackers as all of the content of the new windows, websites and .txt files is written in this language. We also could predict that people who speak Spanish are the main victims. This could be implemented by transmitting executables that would be understable and relevant to Spanish-speaking users.
However, Reyptson.exe payload reads information about supported languages: this could mean that the crypto-virus checks whether the Spanish language is selected as a preference. If not, this could mean that the ransomware is programmed to self-destruct. The infection does not replace the original file-extensions, but appends .REYPTSON after it.
From the way that the ransomware is being detected, it could be that Zusy, a bank Trojan, could be involved with the distribution of the infection. Knowing the fact that Zusy is targeting banking accounts, there is a chance that the infection will be involved in an underground activity of not only file-encryption, but also the attempts to figure out credentials to banking accounts.
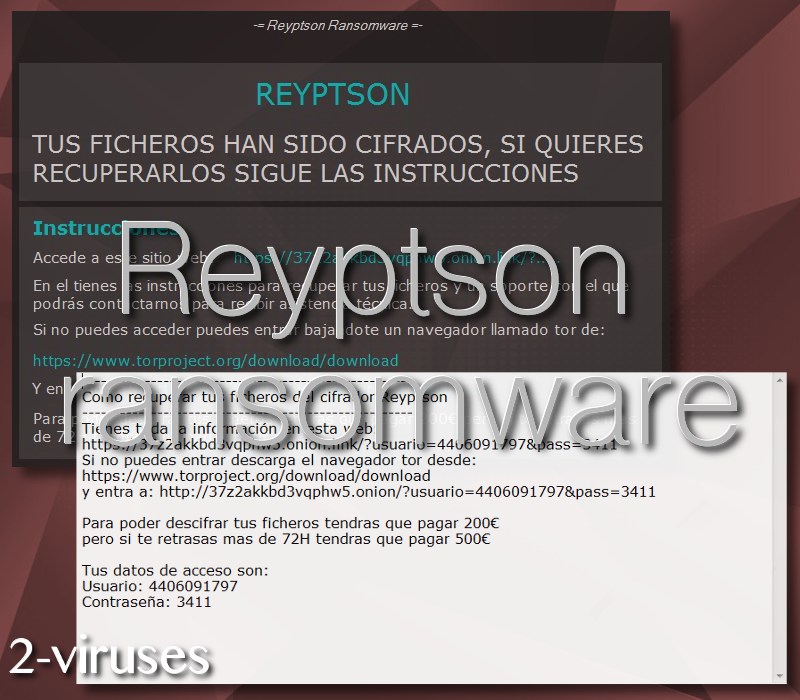
At first, Como_Recuperar_Tus_Ficheros.txt is placed on victims’ desktops and it contains the basic aspects about the infection. In this .txt file, victims will also be introduced with the information, regarding an ID an a passcode to enter unique websites (that belong to hackers). In addition, crypto-virus is to launch a new window, containing similar details, but contains new info as well, like the amount of the ransom. According to it, the infection will begin with a fee of 200 US dollars (0.09572BTC). However, since victims will be reluctant to pay, after 72 hours the ransom is expected to reach 500 US dollars (0.24230 BTC).
We have mentioned that a unique ID and passwords are generated. They are to be inserted into 37z2akkbd3vqphw5.onion.link which contains all of the information about infection in one convenient place. While you would assume that it shall be only reachable via TOR browser, you would be mistaken: the website loads on all of the regular applications as well.
Decryption/removal options, distribution of ransomware
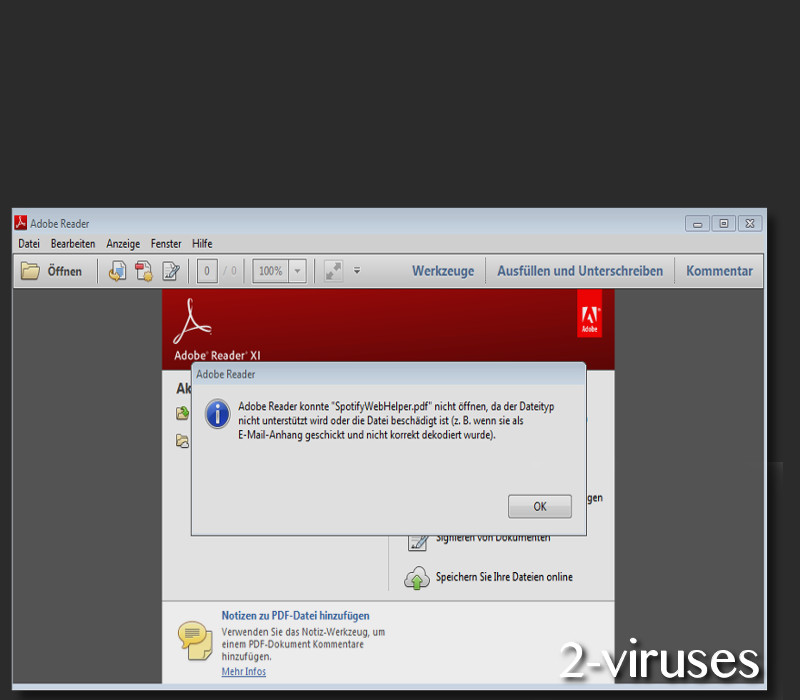
The infection generates a lot of new folders that will appear to be related with the Spotify service. It could be that ransomware will transmit files that will pose as belonging to the respectable service. In random email accounts, attachments like SpotifyWebHelper.pdf could be received. According to security researchers, these files do not open appropriately and are completely fake.
If you notice that odd letters have found way into your account, check their reliability before deciding to reply or to download included attachments. If a message pretends to be from Spotify service, you should check whether sender’s email address belongs to the official service. If it only looks similar, it could be that hackers have selected you as a target.
As for the decryption, currently we do not have a guaranteed option. Developers of free file-recovery tools have not constructed a plausible cure. Until this happens, do not even consider paying the ransom. Hackers could trick you by having very little interest in helping you even if you do send the required amount of bitcoins. Since 72 hours are given before the ransom increases, you should try to remove the infection.
Copy the encrypted data and place it somewhere safe as ransomware could try to remove all data if it feels threatened by anti-viruses. Removal of the crypto virus is also important if you plan to decrypt your files (or at least try to). In the sections below, you will find more information about the manual removal of ransomware and ways to recover damaged digital data. For an automatic detection and elimination, you are advised to run a scan with Spyhunter or Malwarebytes.
Reyptson Virus quicklinks
- Research about this cryto-virus
- Decryption/removal options, distribution of ransomware
- Automatic Malware removal tools
- How to recover Reyptson virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Reyptson virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Reyptson virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Reyptson virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Reyptson virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Reyptson virus. You can check other tools here.Step 3. Restore Reyptson virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Reyptson virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Reyptson virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








