Not long after New Year’s eve we have the first ransomware of 2016. It is called Ransom32 and it’s not like all other ransomware. Cyber security researchers revealed that Ransom32 is the first ever ransomware powered by JavaScript. While majority of old ransomware was hazardous only for Windows OS, Ransom32 can infect all most common operating systems – Mac, Windows and Linux OS.
Ransom32 even has a dashboard that helps cyber criminals to set preferred Bitcoins account (for ransom payments) and monitor income from users with infected computers.
It’s worth to mention that Ransom32 is distributed by the name Chrome.exe – developers try to trick users this way. That’s why you should download Chrome web browser only from official sources.
Ransom32 is plain simple so anyone can download and use it. It comes in a form of WinRAR archive that extracts automatically once inside of victim’s computer. Immediately after that, most of files are encrypted with 128-bit AES encryption.
About Ransom32 ransomware
Cyber criminals usually distribute this ransom via emails. You might notice an e-mail from unknown sender with attached file. Its a common practice that those emails fall into spam category, so you should not open them. However, if it happens so that email like this shows up on your inbox, do not open attached files if you are not aware whether they are legitimate or not.
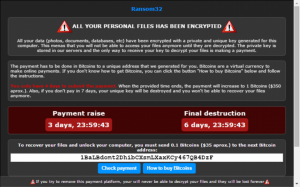
If you open this malicious attachment, WInRar file with Ransom32 in it will automatically extract. That’s it – your files are encrypted and there are no known method to decrypt them. Here’s how your desktop will look like after the encryption:
It says:
“ALL YOUR PERSONAL FILES HAS BEEN ENCRYPTED. All your data (photos, documents, databases, etc) have been encrypted with a private and unique key generated for this computer. This menas that you will not be able to access your files anymore until they are decrypted. The private key is stored in our servers and the only way to receive your key to decrypt your files is making a payment.
The payment has to be done in Bitcoins to a unique address that we generated for you. Bitcoins are a virtual currency to make online payments. If you don’t know how to get Bitcoins, you can click the button “How to buy Bitcoins” below and follow the instructions.
You only have 4 days to submit the payment. When the provide time ends, the payment will increase to 1 Bitcoins ($350 aprox.). Also, if you don’t pay in 7 days, your unique key will be destroyed and you won’t be able to recover your files anymore.
So as you can see, you will be asked to pay around $35 in Bitcoins. However, there are no guarantees that you will retrieve your files after the payment, so we suggest to think twice before doing that. They also added timer to force people make payments.
Ransom32 can encrypt basically all files, such as:
*.jpg, *.jpeg, *.raw, *.tif, *.gif, *.png, *.bmp, *.3dm, *.max, *.accdb, *.db, *.dbf, *.mdb, *.pdb, *.sql, *.*sav*, *.*spv*, *.*grle*, *.*mlx*, *.*sv5*, *.*game*, *.*slot*, *.dwg, *.dxf, *.c, *.cpp, *.cs, *.h, *.php, *.asp, *.rb, *.java, *.jar, *.class, *.aaf, *.aep, *.aepx, *.plb, *.prel, *.prproj, *.aet, *.ppj, *.psd, *.indd, *.indl, *.indt, *.indb, *.inx, *.idml, *.pmd, *.xqx, *.xqx, *.ai, *.eps, *.ps, *.svg, *.swf, *.fla, *.as3, *.as, *.txt, *.doc, *.dot, *.docx, *.docm, *.dotx, *.dotm, *.docb, *.rtf, *.wpd, *.wps, *.msg, *.pdf, *.xls, *.xlt, *.xlm, *.xlsx, *.xlsm, *.xltx, *.xltm, *.xlsb, *.xla, *.xlam, *.xll, *.xlw, *.ppt, *.pot, *.pps, *.pptx, *.pptm, *.potx, *.potm, *.ppam, *.ppsx, *.ppsm, *.sldx, *.sldm, *.wav, *.mp3, *.aif, *.iff, *.m3u, *.m4u, *.mid, *.mpa, *.wma, *.ra, *.avi, *.mov, *.mp4, *.3gp, *.mpeg, *.3g2, *.asf, *.asx, *.flv, *.mpg, *.wmv, *.vob, *.m3u8, *.csv, *.efx, *.sdf, *.vcf, *.xml, *.ses, *.dat
How to avoid Ransom32 ransomware
There are several things you should do to keep your computer save. First of all, always protect your system with active and trustworthy anti-malware application. We suggest to use either Spyhunter or Malwarebytes. You should also make regular backups of most important data stored on your system. Eventually, you should not open questionable email attachments.
If your computer is already infected and you don’t know what to do, take a look at our instructions below.
Ransom32 Ranswomare quicklinks
- About Ransom32 ransomware
- How to avoid Ransom32 ransomware
- Automatic Malware removal tools
- How to recover Ransom32 ranswomare encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Ransom32 ranswomare encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Ransom32 ranswomare encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Ransom32 ranswomare has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Ransom32 ranswomare
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Ransom32 ranswomare. You can check other tools here.Step 3. Restore Ransom32 ranswomare affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Ransom32 ranswomare tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Ransom32 ranswomare encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








