The Dark web is a controversial place, full of wicked goods. Hackers might be fond of this palace of shady products, but it is crucial to remember that people are not to explore this area without legitimate reasons. Security researchers occasionally swing by to stay informed about the new available threats. Now, they have detected a RaaS (ransomware as a service) merchandise which allows amateur hackers to take advantage of a fully-functional ransomware virus. Ranion is the title which has been used to refer to this service. Even thought this seems like a tough recipe for trouble, creators of Ranion ransomware are explaining their product as completely educational. Basically, what we are expected to believe is that people that are to choose from different package deals are not to exploit it in any illegal manner. To find out more, read the full article.
Detailed description of Ranion ransomware a.k.a RaaS
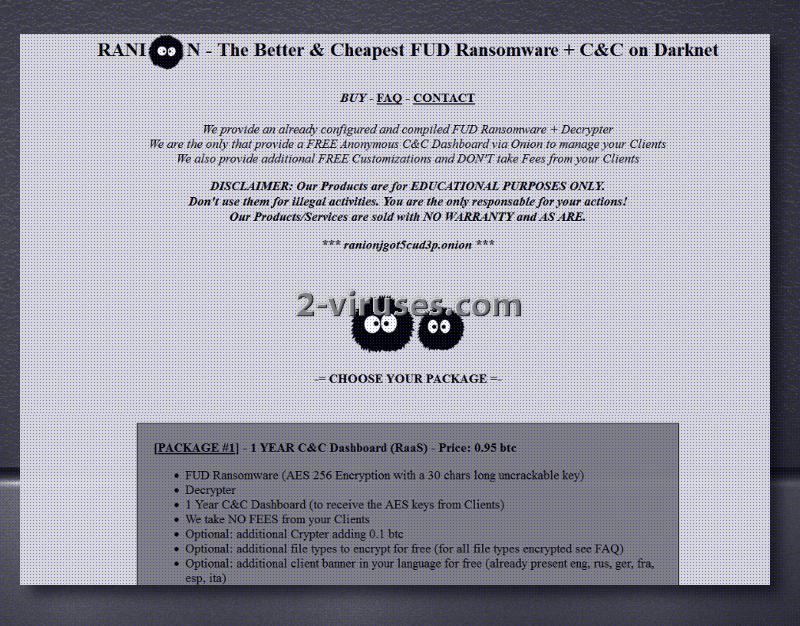
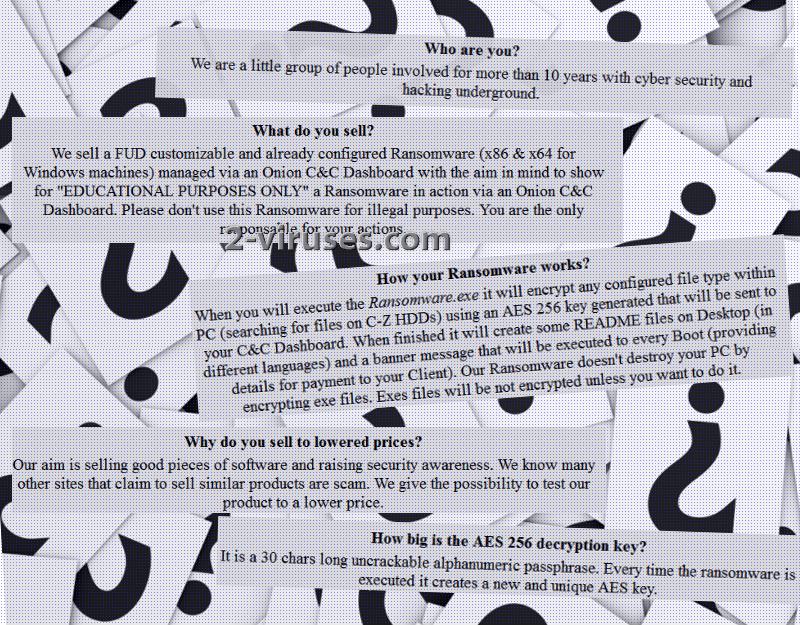
Ranion ransomware is identified to produce a sophisticated virus which is also explained to be FUD (fully undetectable). Together with the main payload, hackers also provide a tool for decryption. People that are behind this are introducing themselves as a small group of hackers that have been focused on the cyber world and hacking for more than a decade. Ranion ransomware does not require any skills and basically anyone can explore its capacities. The matter of whether you should do this is a different subject to discuss. This free-of-charge service should not tempt you: you are better off without getting involved in ransomware projects, even if this is is explained to be produced solely for educational purposes. Ranion virus can also be customized by different buyers and the capacities for individual modifications depend on the package that gets chosen. Despite whichever is chosen, the creators of Ranion do not obligate its users to share their received ransoms with them.
1 year deal costs 0.95 BTC which equals 987.97 US dollars and an alternative 6 month deal is available for 0.60 BTC (623.56 US dollars). The first choice provides the elaborate virus, a decryption tool, one-year access to C&C server and allows people to make some custom modifications to the variant. Optionally offered features include: additional Crypter that raises the ransom up 0.1 BTC and more file types to be encrypted. In addition to that, people from different countries, planning to spread this variant among individuals that do not necessarily understand English, Russian, German, French or Italian, are able to display a customized banner in their preferred language. The same features are applied to the six-month deal, only that access to the C&C server lasts 6 months. Ransomware is explained to be functional on 32-bit and 64-bit Windows devices. The following file types are explained to be available for encryption, but the list might be appended with new extensions if a client desires to extend it.
.sql, .mdb, .db, .accdb, .sln, .php, .jsp, .asp, .aspx, .html, .htm, .xml, .psd, .txt, .rtf, .doc, .docx, .xls, .xlsx, .ppt,.pptx, .odt, .ods, .jpg, .jpeg, .png, .bmp, .csv,.zip, .pst, .ost, .pab, .oab, .msg, .cs, .java, .cpp, .cc, .cxx.
Of course, every user will be able to add a bit of themselves into the ransomware, since they will have to append some individual information. For example, they will to create a bitcoin address and leave it in the ransom note. In addition to that, they are also going to have to add their email addresses (this is going to be the contact that ransomware victims can consult with their abusers). This is not the first time that we encounter RaaS services. We have already discussed Satan ransomware, but it is a little different from this variant. To learn more about this RaaS, click here.
Decryption options for Ranion ransomware
Since this is identified to be an educational project, it is debatable whether it is going to be used in a more malicious manner. For now, there are no or a few reports about this variant to suggest malicious activity. We hope that Ranion ransomware won’t cause any problems for you and if it does, contact security researchers immediately. Of course, all of the released viruses are going to be exploiting AES encryption cipher. Every computer owner should come to terms with the necessity to store their files in backup storages or other secure locations. This should make you completely immune to ransomware infections.
How can your system be infected with Ranion ransomware?
Basically anyone can become the distributor of Ranion virus. After setting up this virus, people will have to distribute its payload in order to try this infection out. It might be that they are going to send misleading email letters which is a relatively simple option. If hackers are more skilled, they might take advantage of various exploit kits and infect people using them. Nevertheless, be cautious and never open odd email emails or visit websites that might be exposed to hacking.
Since this variant has been identified to be fully undetectable, some weaker security tools might not detect it. However, we believe that Spyhunter or Malwarebytes are going to be professional enough to find it. For a manual removal and options for decryption, scroll down.
Ranion Ransomware quicklinks
- Detailed description of Ranion ransomware a.k.a RaaS
- Decryption options for Ranion ransomware
- How can your system be infected with Ranion ransomware?
- Automatic Malware removal tools
- How to recover Ranion ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Ranion ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Ranion ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Ranion virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Ranion ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Ranion virus. You can check other tools here.Step 3. Restore Ranion ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Ranion virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Ranion ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.