Radiation ransomware virus (also known as Hell ransomware), according to the assembled information that security researchers have compiled, has been attributed to the collection of infections that do not properly function and are still in progress. Authors of this sample have probably failed to run test-runs that would show them the flaws that the crypto-virus contained. Filenames of the data (that turns out to be suited for the encryption process) does not change; neither do the extensions that the executables contain. The file-encoding process is not taken lightly as it is completed with AES and RSA algorithms.
Investigation of this crypto-virus
ChaseBot.exe (NativeRansomware.exe) is the payload that ends up in operating systems and commences harmful activities like inserting entries into the Windows Registry and checking whether an operating system is vulnerable or protected by sophisticated anti-virus programs instead. The file could be transmitted via a number of places, but the topic of distribution will be discussed in one of the following paragraphs.
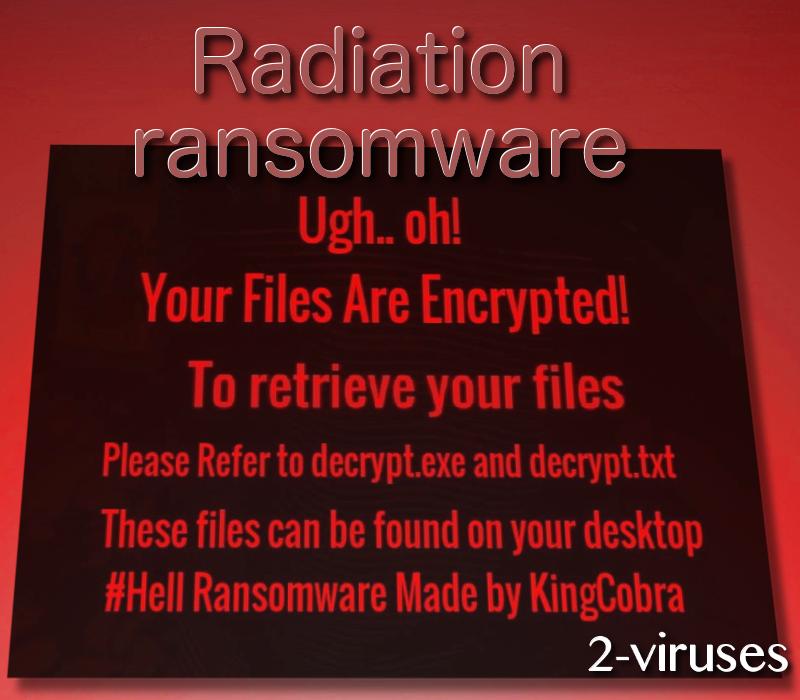
This type of crypto-viruses are more difficult to treat as double-encryption is applied. Furthermore, the infection has been determined to initiate commands that would automatically assign an original wallpaper as the desktop background. In the message, victims are encouraged to open Refer to decrypt.exe and decrypt.txt. However, the person responsible could not help himself or herself and left their nickname at the end, stating that “Hell Ransomware Made by KingCobra”. The same image could be applied as the screen-locker which will prevent users from accessing their operating systems.
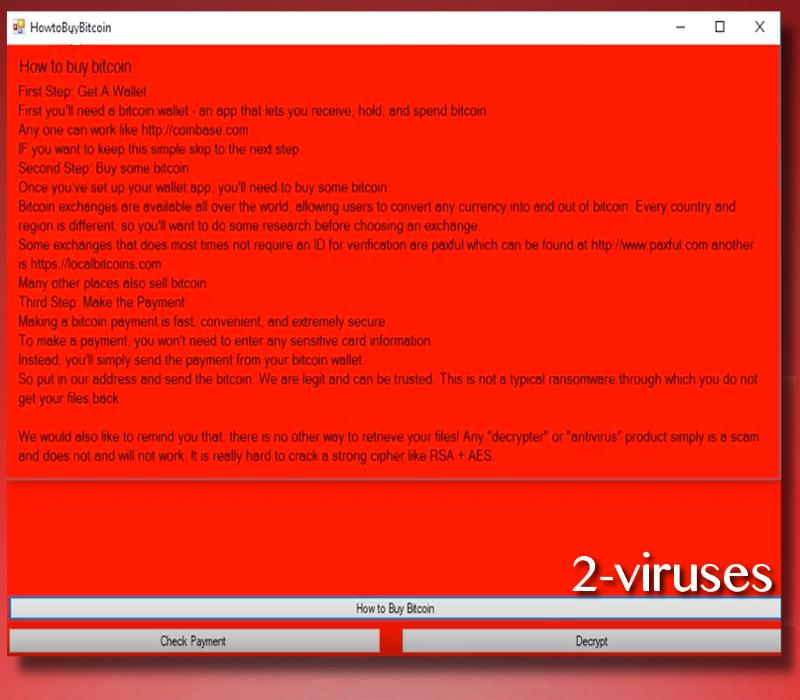
Radiation crypto-virus also contains an additional window that features sections of “How to buy bitcoin”, “Check Payment” and “Decrypt”. After clicking on the first button, you will be presented with a list of steps that are expected to be applied for the purpose of completing a transaction of bitcoins into a hackers’ bitcoin wallet. You are not only discouraged, but also forbidden from buying bitcoins and giving them away to hackers in exchange of your files. The hacker that calls himself/herself KingCobra is not be trusted as he/she can have very little interest in helpings victims (even if they are obedient and pay the ransom).
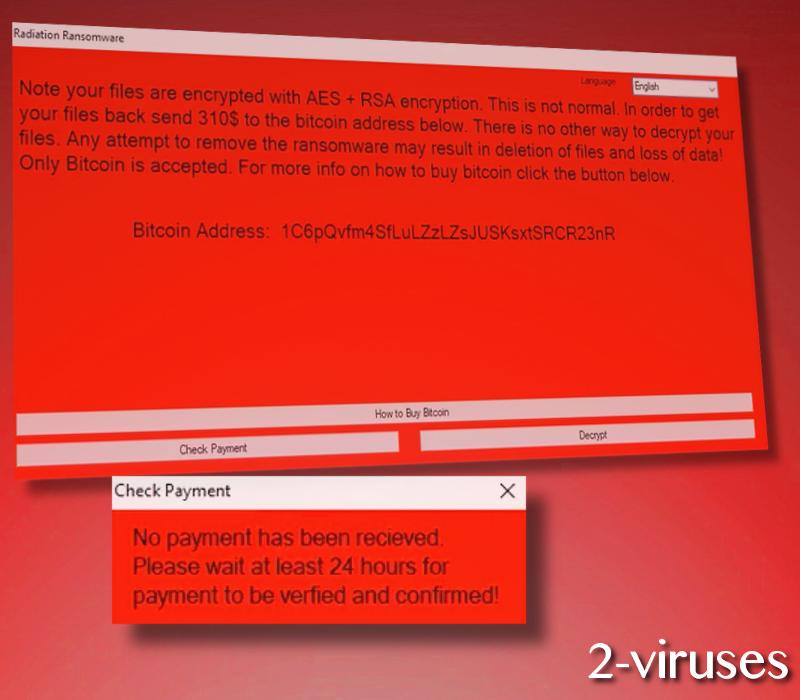
There are more promising techniques to explore for file-recovery and it does not include paying the ransom that hackers demand. You could check whether the crypto-virus deleted Shadow Volume Copies or leaves them out of vicious plans. Additionally, there are tools that have been known to help when ransomware infections corrupt executables. However, since Hell ransomware is probably not distributed yet, it depends whether its activity will actually begin or reach specific level. If it does, we are sure that security researchers will focus on this variant and attempt to generate a solution that does not require users to pay 310 US dollars which equals 0.12491 BTC.
We have promised to elaborate more on the subject of ransomware-distribution. One of the most obvious techniques is that the infection’s payload will be transmitted via spam letters. We have not discovered an exact campaign that would persuade people to download the harmful executable of the latter crypto-virus. Nevertheless, this does not mean that the infection is not going to be fully-developed and its activity won’t begin to be more noticeable. Additionally, infections can also utilize exploits kits, find vulnerabilities in devices and exploit them for the sake of delivering malware.
As for the removal process of crypto-viruses, a manual option is to be selected by people that have some experience in similar objectives. On the other hand, average users are welcome to run scans of their operating systems. This will help them discover every threat that might be affecting their operating system. Spyhunter or Hitman are the professional applications that will help you stay safe in the future as well.
Radiation Virus quicklinks
- Investigation of this crypto-virus
- Automatic Malware removal tools
- How to recover Radiation virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Radiation virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Radiation virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Hell ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Radiation virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Hell ransomware. You can check other tools here.Step 3. Restore Radiation virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Hell ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Radiation virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








