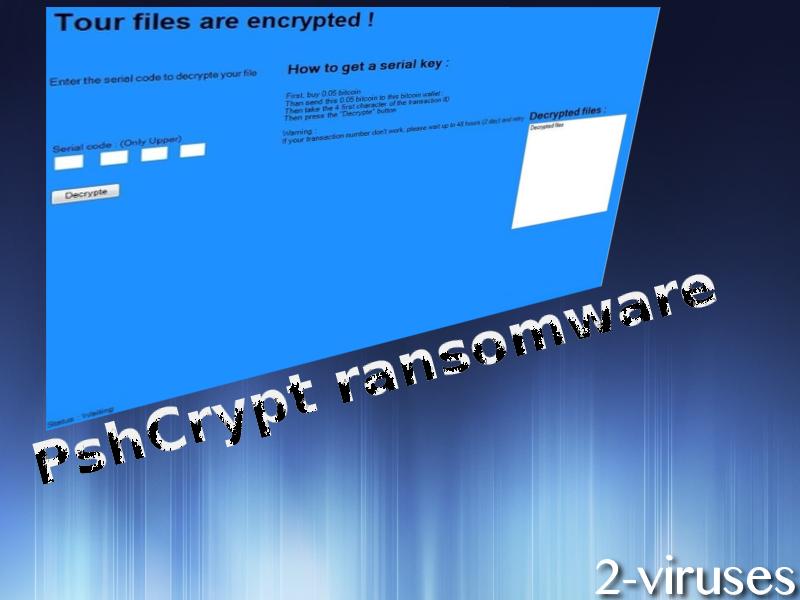
PshCrypt ransomware virus is a brand-new infection that uses a .psh extension and includes inappropriate clues in its structure. This variant is not an advanced version and security analysts did not take long to figure out that it is decryptable. The payload of this infection is d723f6a6867a19f838d1678177fafea5.virus and hackers might have persuaded users into downloading it while it was imposing as a different type of file. XExplorer.exe has been determined to also be related with this virus, which means that the payload can be transmitted as a Trojan, pretending to be an installer for Internet Explorer. If you have become infected and the ransomware displays a blue lock-screen, there is a very easy way to recover your files. All you have to do is type in a ‘HBGP’ combination in the places where the serial code is demanded.
How does PshCrypt ransomware proceed?
PshCrypt virus does not fall from the tree that holds other ransomware infections. This type of malware has a specific step program which is applied to the majority of variants. There are no clear identifications about which algorithm for encryption is selected by the creators of PshCrypt, but we have our reasons to believe that nothing more than an AES cipher should be exploited. Hackers expect victims to easily give away money for a chance of retrieving their data back to their original state. 0.05 BTC is the sum that crooks are collecting, and this is not a steep price to pay when compared to demands from other ransomware infections. In more understandable terms, the ransom is approximately 63.35 US dollars.
After PshCrypt virus is planted into a device, it will initiate modifications into Windows Registry Keys by slipping in additional entries that will make the payload run automatically. The payload itself will be placed in one of the folders. In theory, the presence of a ransomware infection could be detected after reviewing Windows Task Manager, but people might not be capable of separating legitimate processes from potentially dangerous. This becomes even more complex when infections hide behind regular processes that are normally featured in the Task Manager.
Luckily, there is no reason to stress about this ransomware infection. If access to your computer is blocked and a screen-locker makes demands for bitcoins, you should simply enter ‘HBGP’ code and your files should be decrypted. More and more instantly decryptable samples have been released, meaning that the number of wannabe-hackers is increasing. If you have any difficulties with the decryption process, leave a comment below and we will assist you.
Tips to bypass PshCrypt ransomware
Like any other ransomware, PshCrypt can be avoided if you navigate your browsing wisely. You should install updates/software from only reputable sources in order not to be tricked by Trojans. Peer-to-peer downloading also is a problem since you can be lured with a promise of a new movie/game/application while in fact; it will install something completely different. Additionally, domains that are adult-oriented and distribute pornographic content are also one of the leading sources for crypto-viruses. Malicious spam letters could also be transmitted to random people in the hopes of tricking them into downloading files that have hidden macros. For example, you might be offered to download a .pdf, which will conceal .doc, and that ,doc will hide a malicious payload.
Back up your data and PshCrypt ransomware won’t stand a chance
If you store your files in more than one location, you will immediately become immune to ransomware infections and have no trouble in retrieving your data. There are a lot of storages to choose from, but if you are looking for the easiest one, you can simply plant valuable data in your flash drive. However, do not keep your USB connected to your device at all times. If a ransomware manages to slip into a device, some of the variants are able to cipher data that are found in the drive.
Once the files are encrypted, you should direct your focus to the removal of PshCrypt ransomware. This can be done with Spyhunter, Plumbytes and Hitman. For more information about universal methods for decryption, look below.
Pshcrypt Ransomware quicklinks
- How does PshCrypt ransomware proceed?
- Tips to bypass PshCrypt ransomware
- Back up your data and PshCrypt ransomware won’t stand a chance
- Automatic Malware removal tools
- How to recover PshCrypt ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover PshCrypt ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover PshCrypt ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before PshCrypt virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of PshCrypt ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to PshCrypt virus. You can check other tools here.Step 3. Restore PshCrypt ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually PshCrypt virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover PshCrypt ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








