PSCrypt ransomware virus emerged a short while ago and Wmodule.exe is indicated as its payload. The crypto-infection has already managed to infect some users; therefore, it should not be regarded as only a theoretical threat. We can find relations of this sample with an another recent one: XData. Both of these menaces targeted people from Ukraine, with PSCrypt virus also aiming to affect people from Russia and Netherlands.
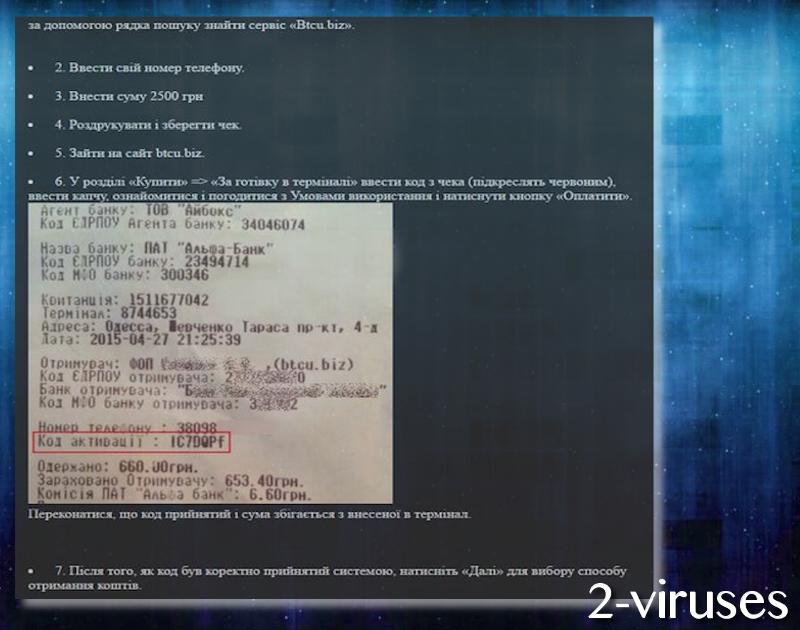
AES algorithm is selected for the job of data-encryption, which is fully completed after .pscrypt extension joins the ruined executables. Another hint that variant targets Ukrainians is that it demands money in the monetary unit of Ukraine. 2500 Ukrainian hryvnias are required for the file-recovery. Approximately, this sum equals 96.029 US dollars. However, the hackers wish that their “earned” payments would be send via the bitcoin system. This means that victims are instructed to purchase bitcoins. In this case, 0.035651 BTC is the fee.
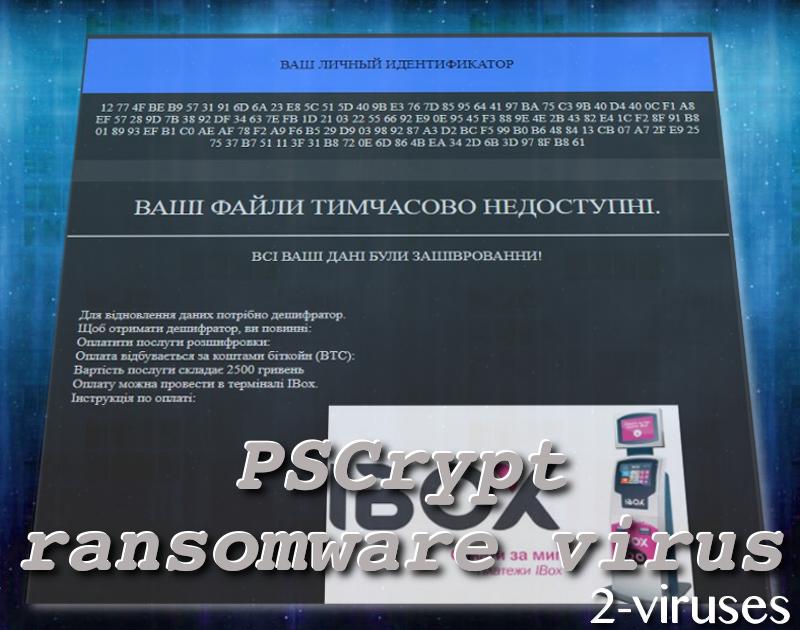
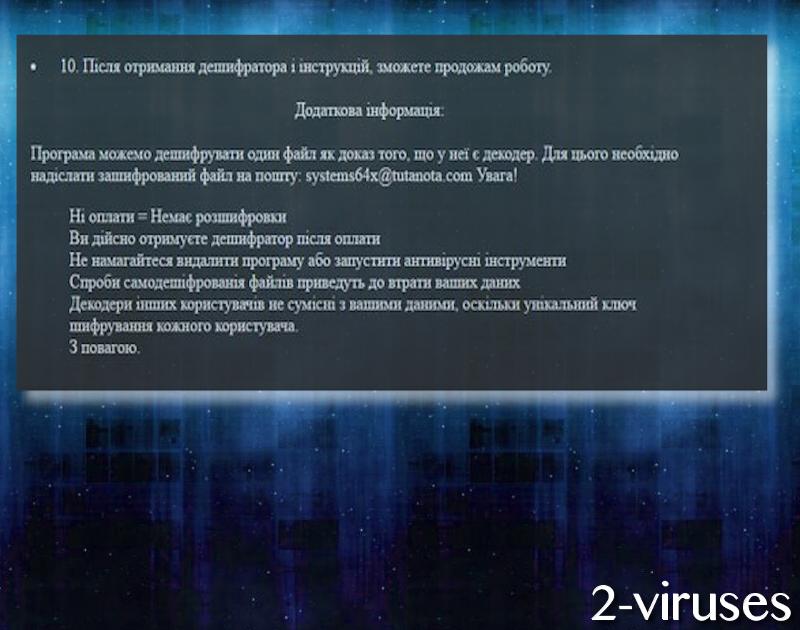
All of the demands are carefully explained in a Paxynok.hmtl file that launches in victims’ preferred browsers. To generalize, we have already indicated the main features that this ransomware has. Looking at the .exe file which has been determined to be the payload, we notice that it is labeled as high-risk. It was noticed that the ransomware changes memory access rights in a remote process, injects entries in Windows Registry keys and probably uses certain measures to remain undetected until the encryption is fully completed.
Currently, security researchers have not provided a free file-recovery tool that could help victims escape the infection without consequences. However, since a number of people have already become infected with this sample, we do predict that a tool will be published. Some users could assume that it is beneficial to try to restore Shadow Volume Copies, but not in the case of PSCrypt. It appears to initiate a command that deletes all these copies.

It would be best that users would grasp the necessity to backup their data. This can be done by selecting an appropriate online storage. On the other hand, you could also protect data by simply uploading copies of your valuable digital files into USB flash drives. Keep them safe and you will have a privilege to quickly retrieve files in case of their tragic loss. One small tip: do not keep USB flash drives plugged into your device as it could allow a crypto-virus to encode data in it.
Malware infections like this have a very specific way of distributing. If you would pay close attention to your email inbox, you would notice that many deceptive emails end up in the Spam folder. This saves you from potential dangers, but not always. It is possible that malicious spam campaigns will manage to convince you that opening a specific file is a wise idea. However, remember that it is very risky to download attachments from email letters. If you notice a .doc file, it is possible that you will later on be required to activate macros, which will allow ransomware to enter.
Before victims tryout the file-recovery methods we have enumerated below, it is necessary to get rid of all of the malicious files. Even though this crypto-virus threatens to delete the key for decryption in case victims attempt to run anti-malware tools, it is possible that they are bluffing. You should never be naive enough to believe that hackers will be decent enough to provide their victims with the promised recovery option. Spyhunter or Malwarebytes are all prepared to protect you from malware. It will not only protect you from viruses in the future, but help you find all traces of malicious behavior now.
Pscrypt Virus quicklinks
- Automatic Malware removal tools
- How to recover PSCrypt virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover PSCrypt virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover PSCrypt virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before PSCrypt virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of PSCrypt virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to PSCrypt virus. You can check other tools here.Step 3. Restore PSCrypt virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually PSCrypt virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover PSCrypt virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








