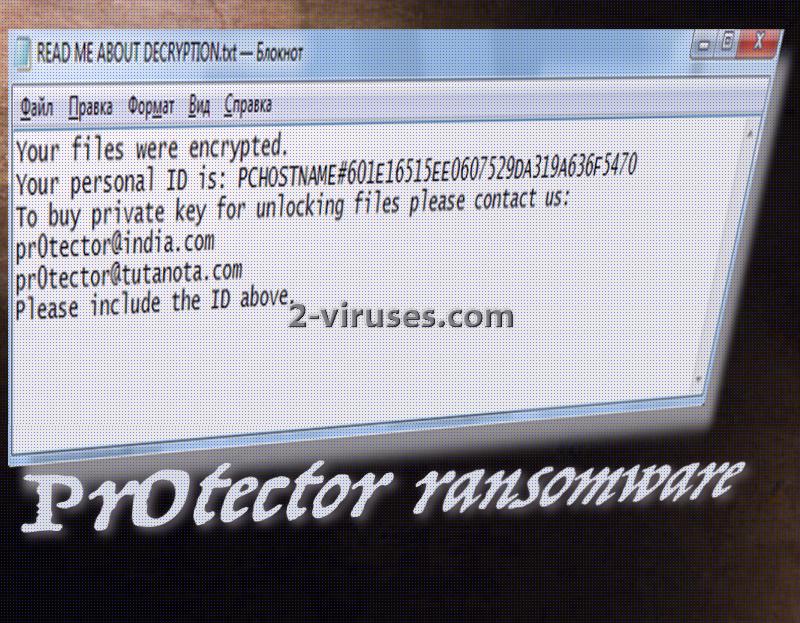
Pr0tector crypto-virus caught our attention as this ransomware is actively distributed and people from all over the world are facing malfunctions because of this variant. According to victims’ complaints, the ransomware might infect devices that belong to business companies or institutions, but is just as capable of infecting personal computers too. Compromised machines are to be assigned a special and unique ID code, which will contain “PCHOSTNAME#” and a random set of numbers and letters. Pr0tector virus does not feature, or at least for now, a screen-locker and provides all of demands in a READ ME ABOUT DECRYPTION.txt file. Hackers indicate than in order to obtain the private key for decryption, victims have no other choice but to write email letters to [email protected] or [email protected]. The message is supposed to share an ID number of a specific victim. According to it, crooks will determine an appropriate fee for decryption.
The latest news about Pr0tector ransomware
The date which is marked by the appearance of Pr0tector ransomware is the 28th of March. Around this time first victims started reporting that their files became inoperative. Additionally, data which is ruined by Pr0tector ransomware is labeled: .pr0tect extension will be appended. Surprisingly, even though the ransom note is written only in the English language, the ransomware is a threat to multiple countries. Countries like Chile and Peru already have people, infected with Pr0tector ransomware.
How does a ransomware infection manage to remain undetected right until the moment it chooses to reveal itself to the victim? Well, since victims of Pr0tector virus are clueless when it comes to explaining the origin of this infection, we think that its payload can be transmitted via vulnerable websites or Trojans. While downloading one file or a program, you can never know whether you won’t be getting an application which is only posing as a harmless executable. After the payload of Pr0tector virus ends up in one of your folders, it will strengthen its position by making modifications to Windows Registry Keys. Due to this alteration, the payload will be able to secretively run in the background while you pursue other activities.
Also, some researchers emphasized that this Pr0tector ransomware might be somehow related with an older virus, Dharma. However, these statements have not been confirmed yet. If they do, this link between two crypto-viruses can help you retrieve your files without paying the ransom. How? Well, if the Pr0tector proceeds similarly to Dharma, it can be decrypted with the decryption tool, designed specifically for Dharma variant.
Methods that are used to spread Pr0tector ransomware
There is a lot of speculation when it comes to distribution of this variant. Researchers emphasize that infected users might have have enabled Remote Desktop (RDP) feature which was not secured properly. It might have been that hackers spotted that a device had this feature and attempted to gain remote control via it. You should not turn on the RDP since it can cause more security issues than you could expect. In addition to that, we should not forget that users might have faced the payload of a Pr0tector virus in an email letter they received. Lastly, weak websites or random advertisements can also be indicated as one of the potential sources of Pr0tector virus.
Pr0tector ransomware: to pay or not to pay for decryption?
Pr0tector ransomware offers people to contact either one of the two email addresses that are indicated in the ransom note. Hackers will presumably provide victims with all of the necessary information to make a payment. However, we should not think that you are to support crooks financially. By sending them money, you will only be sponsoring future ransomware projects. Remember, that there are other ways of trying to recover data. As soon as you remove the infection from your device, try some of the methods we have listed below: maybe they will help. However, before trying to recover files, remove the infection carefully with Spyhunter or Malwarebytes.
Pr0tector Ransomware quicklinks
- The latest news about Pr0tector ransomware
- Methods that are used to spread Pr0tector ransomware
- Pr0tector ransomware: to pay or not to pay for decryption?
- Automatic Malware removal tools
- How to recover Pr0tector ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Pr0tector ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Pr0tector ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Pr0tector virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Pr0tector ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Pr0tector virus. You can check other tools here.Step 3. Restore Pr0tector ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Pr0tector virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Pr0tector ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.