A Polish ransomware infection has dipped into the pool of malware and is preparing for a swim. Presumably its main targets are people from Poland since not all of the people might understand the Polish language. According to the ransom note that gets placed into the infected device, all of the data has been encrypted with AES-256 algorithm for encryption. It leaves links to several pages so the victims would learn more about the ransomware infections in general. Since the expected audience to receive these viruses is Polish surfers, the recommend domains present content in this language. People can engage in a conversation with hackers via two email addresses: [email protected] or [email protected]. You should never voluntarily contact hackers since their skills will only attempt to convince you that the only way to restore files is to surrender and obediently submit the requested fee. More information about the Polski crypto-virus can be found in the following sections. We will answer questions, concerning its activity, decryption and distribution.
Polski virus: a nightmare for Polish people
How do you begin to explain a ransomware virus? One of the primary mentions should include its distribution, but we are to speak about it in the following sections. We can already establish that crypto-viruses never play fair and their manners are completely rude. It infects devices in a completely unacceptable way, but people are partially responsible for falling for their tricks. Polski virus chose to mingle around Polish people and bring terror to this country. This is one of the first variants to aim at such audience. Let’s move on a more vital topic: what are the recognized habits of Polski virus?
Ransomware creators have a clear-cut objectives in their minds. After storming into a device, Polski virus will skyrocket to pursue its other goals. It will bring forward its payload in one of the folders, but its mere presence is not enough: it has to be launched. To speed things up, ransomware will lay down the law: new Windows Registry Keys are to run Polski virus after every reboot. Polski virus will not be noticed as a trespasser until it attains good outcome out of its following procedures. One of them is to contact the C&C server and provide it with essential information about the new victim. Then the search for files for encryption can take place.
After that, the selected files are going to get encrypted with a cipher and their original extensions are going to be appended with .aes mark. Then, two files are going to be placed in the device, explaining the situation: !!! – – ODZYSKAJ-PLIKI – – !!!.txt and !!! – – ODZYSKAJ-PLIKI – – !!!.html. In order to be informed about the fee for decryption, people are to write letters to either [email protected] or [email protected]. In addition to these contacts, hackers also leave an 8 digit phone number as a helpline: 61621122. Whatever you do, you are discouraged from engaging in a conversation with the creators of Polski virus. 72 hours are given for victims to contact them and pay the ransom. If the time period hits zero and the ransom is still unpaid, the demanded fee is supposed to double. The primary price is 249 dollars, but after 72 hours, it is going to be 498 dollars. Remember; we do not recommend paying the ransom!
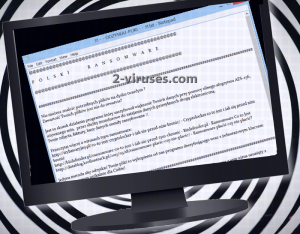
An English translation of the ransom note:
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
P O L S K I R A N S O M W A R E
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
#################################################################You cannot find the necessary files on your hard drive?
The content of your files does not open?This is a result of the program that encrypted the most of your data using strong AES-256 algorithm. Used min. uniformed services for disguising data, transmitted electronically.
Your photos, music, records, databases have been encrypted!!Read more about ransomware viruses:
http://trybawaryjny.pl/co-to-jest-cryptolocker-i-jak-sie-przed-nim-bronic/ – Cryptolocker what it is and how to prevent it
defend
http://bitdefender.pl/ransomware-co-to-jest-i-jak-sie-przed-tym-chronic – Bitdefender.pl – What is ransomware
http://datablog.krollontrack.pl/2015/03/18/ransomware-placic-czy-nie-placic/ – Ransomware pay or not to pay?The only way to recover your files is buying the decryption program from us with a single key,
generated uniquely for you!################################################## ################
By the time you read this whole thing selected files will be encrypted and the virus itself disappeared from your computer.
Key composed of dozens of characters is needed to decrypt data from the disc is available only for us!You can endlessly try to install another antivirus program,
Format the operating system, however, that will not change anything!
If you do not follow our instructions, you will not recover files that were on the HDD.################################################## ################
Once you choose to recover your data, please contact us via e-mails: [email protected] or
[email protected]
You can also contact us via: 616211222 Files Decrypt free to prove that we can do it!
For the rest, unfortunately, you have to pay!Price for decrypt all files: $ 249
Warning ! Do not waste your time, time is money for 72 hours the price will increase by 100%!################################################## ################
Modus operandi: restoring encrypted data
Ransomware viruses are not easy to figure out: it might take some time before the free tool for decryption is going to be released. Until this joyful moment arrives, we are advising you not to panic. Your files are ruined by Polski virus? We can remind you of a couple of methods that might help you. First of all, you can check whether this variant removes Shadow Volume Copies. If not, it is possible to restore them. In addition to that, if you have uploaded your files in backup storages or placed them in other locations, your retrieval of files won’t be a complicated process. However, if none of these options work, you can tryout universal file-recovery tools that might function. Learn more about this option in the section below.
What are the sources of Polski virus?
Ransomware viruses can be found in various places: social networking sites, email inboxes, even websites: you just have to know where to look. Fake messages or posts can very frequently lead to websites or transmit files that are malicious. In addition to that, domains can be affected by exploit kits, capable of helping ransomware viruses spread. Lastly, email inboxes are indicated to be as one of the most prevalent sources to contain ransomware. Spam letter campaigns can be attempting to trick people with fake messages and vile attachments. Since this Polski ransomware aims to inflect on Polish people, it is possible that the messages that get spread are going to be in this language as well for the sake of appearing more believable.
Polski virus must be slew: you can either do this manually, or select an easier automatic option. The latter one needs an anti-malware tool to be possible. Spyhunter or Hitman will certainly remove this virus. Before you do this, it is advisable to copy the encrypted data since ransomware might be programmed to delete it.
Polski Virus quicklinks
- Polski virus: a nightmare for Polish people
- Modus operandi: restoring encrypted data
- What are the sources of Polski virus?
- Automatic Malware removal tools
- How to recover Polski virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Polski virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Polski virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Polski ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Polski virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Polski ransomware. You can check other tools here.Step 3. Restore Polski virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Polski ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Polski virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.