Philadelphia ransomware is a new variant of Stampado ransomware, developed by The Rainmaker and sold on the Dark Web. This RaaS – ransomware as a service – application can make practically anyone a hacker for 400 USD. The Rainmaker announced about his new malicious piece of work in the forums, specifically on the AlphaBay Tor criminal site, laying down his utopian plans to victimize 20,000 users the first day Philadelphia cryptomalware is released. However, this new version of RaaS is not as deadly as its developer wants you to believe. Philadelphia crypto virus is programmed in the AutoIT scripting language and, thus, it can have weaknesses which would make this malevolent program code possible to be cracked. Fabian Wosar of Emsisoft, the most detested person by The Rainmaker, since he has decrypted the first two versions of Stampado ransomware, claims that Philadelphia virus can and will be decrypted.
About Philadelphia Ransomware
Philadelphia ransomware, as the majority of ransomware viruses, uses the asymmetric AES encryption to encrypt the victim’s files. This ransomware virus aims at fixed, removable and network drives, as well as drive root folders. The certain file types targeted include the following:
*.7z;*.asp;*.avi;*.bmp;*.cad;*.cdr;*.doc;*.docm;*.docx;*.gif;*.html;*.jpeg;*.jpg;*.mdb;*.mov;*.mp3;*.mp4;*.pdf;*.php;*.ppt;*.pptx;*.rar;*.rtf;*.sql;*.str;*.tiff;*.txt;*.wallet;*.wma;*.wmv;*.xls;*.xlsx;*.zip
Like Stampado, Philadelphia encrypter appends ‘‘.locked’’ extension (though it can be customized) to the encrypted files. Apart from the extension, it will turn the name of a data file into a random string of numbers and letters. For example, your ‘‘Presentation.ppt’’ file, after Philadelphia’s attack, will look something like this – 7B205C09B88C57ED8AB7C913263CCFBE296C8EA9938A.locked. After the encryption is over, the victim’s lock screen is covered with the following note:
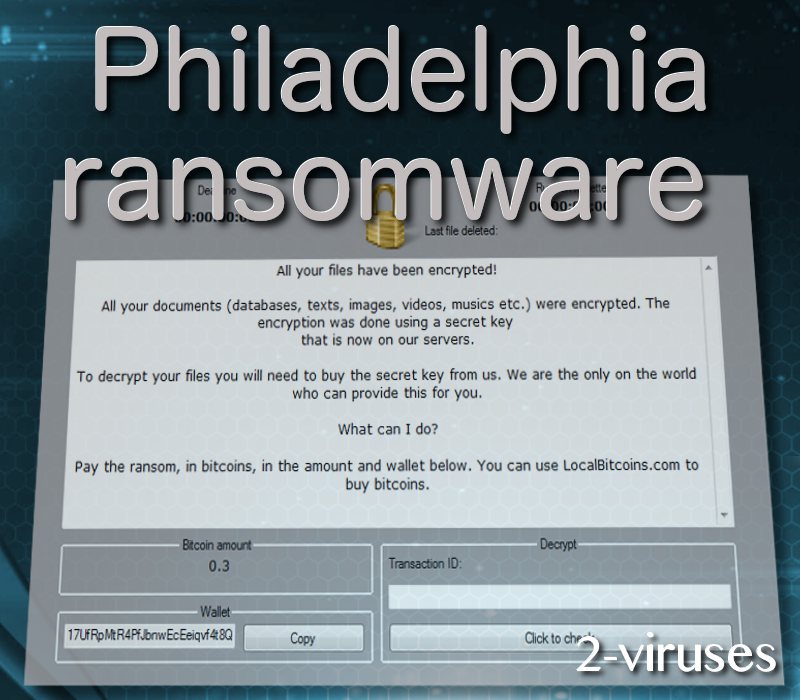
The curious property of Philadelphia encoder, addressed by The Rainmaker as ‘‘the coolest’’ feature, is that it does not use the usual C&C (Command and Control) servers. Instead, PHP scripts, called Bridges, are utilized for storing the encryption key, victim’s data, checking whether the ransom has been paid. A management client, called Philadelphia Headquarters, is another interesting trait of this communication through Bridges. This management console stores the data and has the functions needed for the implementation of an attack. It does also contain the ‘‘Give Mercy’’ button, which is supposed to be clicked by the merciful attackers. The console looks like this:
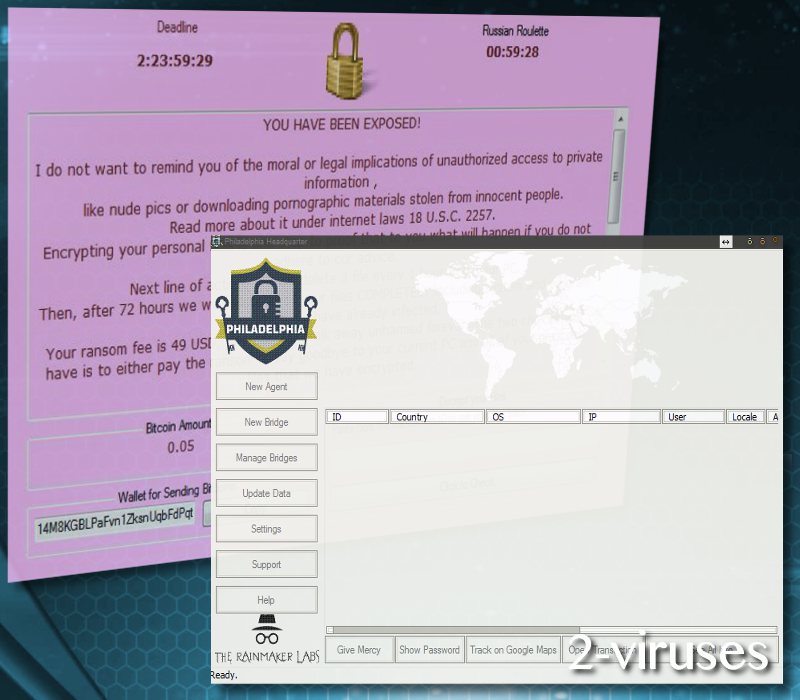
The other features, such as the targeted folders, the time period given to make the ransom payment (named ‘‘Russian roulette’’ – another allusion to Stampado ransomware), the size of the ransom, etc. – can all be customized by the bad lot, who has purchased this nasty program. Thus, the victim, attacked by Philadelphia file-encrypting virus, can never know how much he (she) is going to be asked for, what the deadline is going to be and whether he/ she can beg for mercy. But don’t you dare kneel down before these cyber crooks, especially, when you can almost smell the decryptor to be released.
How is Philadelphia Ransomware Distributed?
Philadelphia ransomware uses the same old tactics of trojan viruses. It is being spread via spam e-mails, disguised as an overdue payment notice from the Ministry of Finance of Brazil. This fact may imply that this particular ransomware threat was specifically designed for carrying onslaught on the Brazilian users. But, in fact, the previous spam e-mail can pop in the e-mail box of any user from any part of the world. The fake notice looks like this:
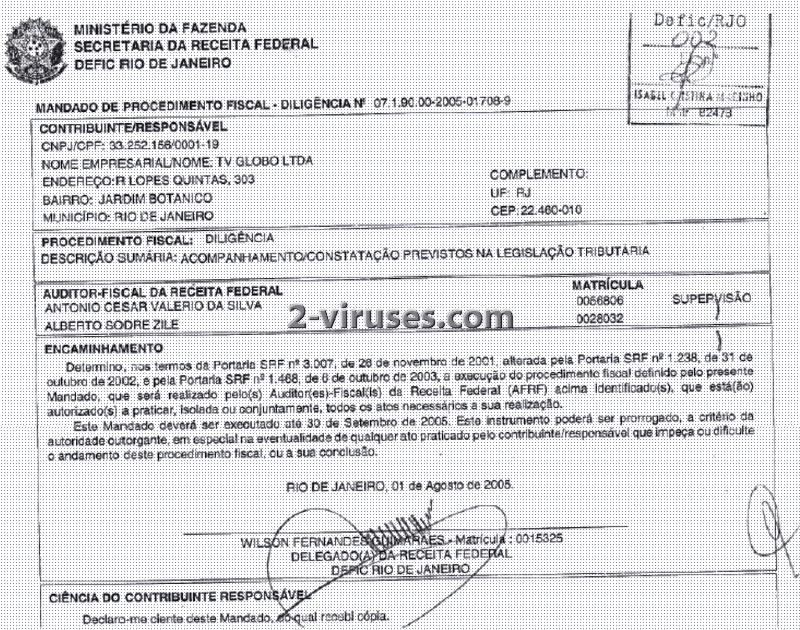
These phishing e-mails enclose a link, which clicked on, activates the malicious JavaScript that downloads and runs the payload of the Philadelphia crypto malware on the victim computer’s system. This is how the users are being punished for their excessive curiosity.
How to Decrypt Files Encrypted by Philadelphia Ransomware?
While we are all patiently waiting for the upcoming decryptor to be realesed, those, who were not so lucky to be plagued by Philadelphia malicious software, cannot wait for the latter to happen. We can advise to use external backup in the form of removable drives, which were not connected to the computer during or after the attack. The affected users can also check the Shadow Volume Copies, since it is still unknown whether this ransomware deletes them or not. As the last resort, professional data recovery tools can be employed. We are talking about such software as R-Studio, PhotoRec, Recuva, software by Kaspersky Lab, etc.
But before rushing with the restoration of your ruined data, copy the infected drive (you will need something to be used on the would-be decryptor) and, most importantly, remove Philadelphia ransomware applying one of the tools: Spyhunter or Malwarebytes. This powerful malware removal software will scan and clean the whole of your computer’s system so that no malicious program code is able to regenerate itself. The manual removal instruction for the removal of Philadelphia malware are rendered just below.
UPDATE: Philadelphia ransomware Decryptor has been released. To use it you will need a file pair with both an encrypted file and its non-encrypted original version. TO distiguish them, simply compare file sizes. Tee size of encrypted files will be rounded up to the next 16 byte boundary of the original file. Select both the encrypted and non-encrypted file and drag and drop both of them onto the decrypter file in your download directory.
Philadelphia Ransomware quicklinks
- About Philadelphia Ransomware
- How is Philadelphia Ransomware Distributed?
- How to Decrypt Files Encrypted by Philadelphia Ransomware?
- Automatic Malware removal tools
- How to recover Philadelphia Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Philadelphia Ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Philadelphia Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Philadelphia Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Philadelphia Ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Philadelphia Ransomware. You can check other tools here.Step 3. Restore Philadelphia Ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Philadelphia Ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Philadelphia Ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








