Pendor ransomware virus is classified in this specific category of malware due to the fact that it uses cryptography to encode users’ files and make them no longer accessible or readable. It was first detected at the beginning of September, but researchers needed some time before actually getting their hands on a proper sample. Titles of crypto-viruses are getting more and more vague and bizarre, like Bud or Potato ransomware variants. However, gaming-enthusiasts might recall the word ‘Pendor’ as it appears to refer to a specific mod.
Actions of Pendor computer virus
Pendor file-encoder is quite easy to detect and most security software find it as Gen:Trojan.Heur.DP.EGW@amGGGinc, Trojan.Heur.DP.ED91AC, HEUR:Trojan.Win32.Generic and other labels (VirusTotal analysis). The ransomware is expected to either display a lock-screen or change victims’ desktops to display ransom notes.
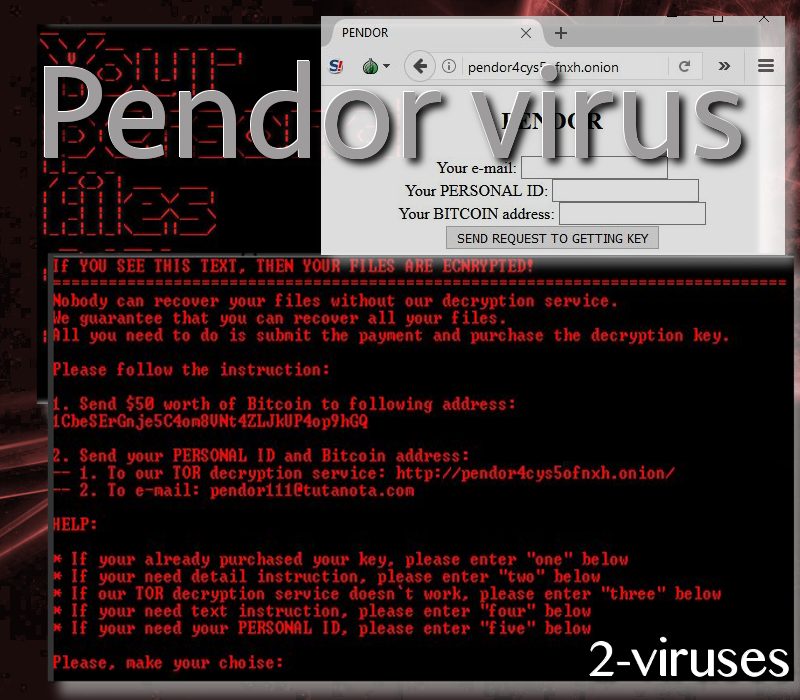
Additionally, it adds and READ_THIS_FILE_1.TXT file which will present instructions both in Russian and English languages. Also, just like ArmaLocky variant, Pendor crypto-virus demands victims to download TOR browsers (What is a TOR browser?) so they could enter these specific domains: pendor4cys5ofnxh.onion, pendorh4pamngr6t.onion and pendoru632ry2xiu.onion.
In the latter website, victims will be able to submit a request to receive a key for decryption of ruined digital data. Before the request can be made, users will have to enter their ID numbers and bitcoin wallets (to which hackers are demanded the payment to be sent). However, the amount required is not that high: 50 dollars. According to the current exchange rates of bitcoin, this sum equals 0.01272BTC.
Presumably, AES algorithm (How encryption molded ransomware) will be used to encode files. They will also all feature .pnr extension which is another indication, helping users realize which ransomware infection has infected their computer systems. Furthermore, victims can also contact hackers via [email protected] and [email protected] email addresses. Since the main keyword of this infection is mentioned so many times, we do not think that users will have any trouble determining which infection has infected them.
Pendor malware will follow the standard protocol of all ransomware viruses by modifying Windows Registry and making sure that the payload would be successfully auto-executed. The sample was determined to insert a lot of files into an operating system, like instructions.txt, pendor.exe, pendor_key.txt.
Goods news: ransomware appears to be decryptable
It is pleasant to find out that the damage that Pendor ransomware has made can be reversed. This is not yet fully confirmed, but Michael Gillespie has expressed such a possibility. If you are infected with this crypto-virus, then contact the mentioned security researchers. In other cases, we usually use these paragraphs to provide some information about techniques that can be used for the sake of recovering data even if security researchers do not find ways to create free decyption keys.
First of all, you could try to recover Shadow Volume Copies. However, this is usually prevented by ransomware as these preserved copies are deleted soon after encoders enter devices. Another option is to use universal file-recovery software. They are not always able to help, but it is worth a shot. However, if you were clever enough to store your valuable digital data in backup storages, then there is no need to worry. All you have to do is retrieve your files from a backup storage and enjoy them once again. The issue is that most people only have their files in hard drives.
There are several malware-distribution methods and this crypto-virus could be using. First of all, spam letters could transmit payloads in forms of attachments. You should never open letters from “spam” folder. Secondly, you should protect your RDP properly. Also, ransomware viruses can be distributed via pop-ups and exploit kits. It would be best to stay away from unknown domains and barely interact with online advertisements. Lastly, we provide options for the removal of ransomware: there is a manual version and automatic, supported by Spyhunter.
Pendor Ransomware Virus quicklinks
- Actions of Pendor computer virus
- Goods news: ransomware appears to be decryptable
- Automatic Malware removal tools
- How to recover Pendor ransomware virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Pendor ransomware virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Pendor ransomware virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Pendor ransomware virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Pendor ransomware virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Pendor ransomware virus. You can check other tools here.Step 3. Restore Pendor ransomware virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Pendor ransomware virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Pendor ransomware virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








