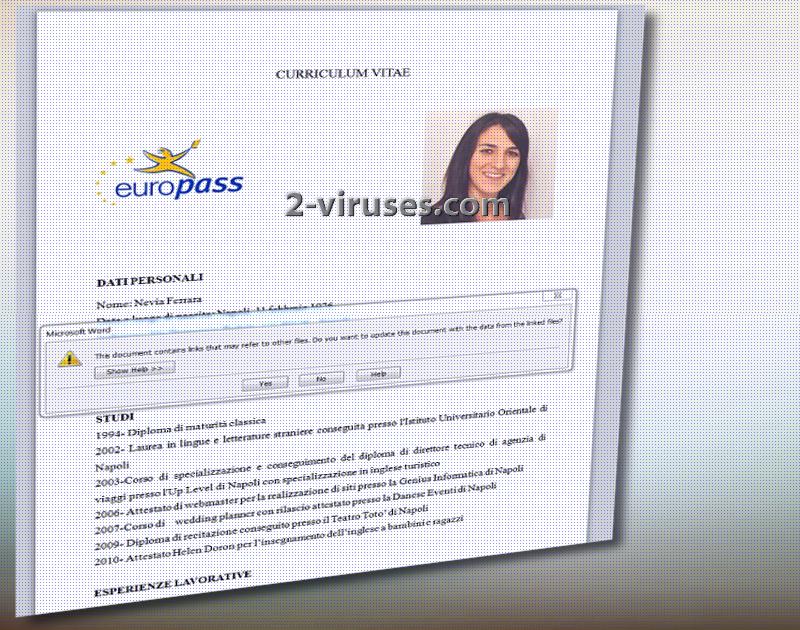
PEC 2017 crypto-virus is identified as one of the crappiest ransomware samples and it was first believed to have been built using Delphi object-oriented, visual programming environment. However, after some analysis, this assumption was denied. Security researchers explain that this variant might be less complicated than infections are coded by professionals. It has already been distinguished that ransomware uses .doc document as a payload and the seemingly harmless file hides malicious macros inside. The exploited vulnerability is known by the ID of CVE-2017-0199 and it refers to a flaw in Microsoft Office and WordPad applications. The detrimental document of PEC 2017 virus is supposed to allow hackers to launch arbitrary codes through it. Evia_ferrara_analista_contabile_eu.rtf is the document which presents a “CURRICULUM VITAE” text which upon clicking launches Windows word executable.
Analysis of PEC 2017 ransomware
The payload of PEC 2017 virus contacts one host. Its IP address is 145.14.145.44 and it is assigned to Netherlands. Msofficed.000webhostapp.com is the contacted domain. After analyzing the payload, several questionable aspects were detected. The infection encrypts data with AES-256 algorithm for encryption which is a common cipher to exploit. PEC 2017 appears to be an Italian ransomware, which might be the reason behind the fact that the malicious executable reads information about supported languages.
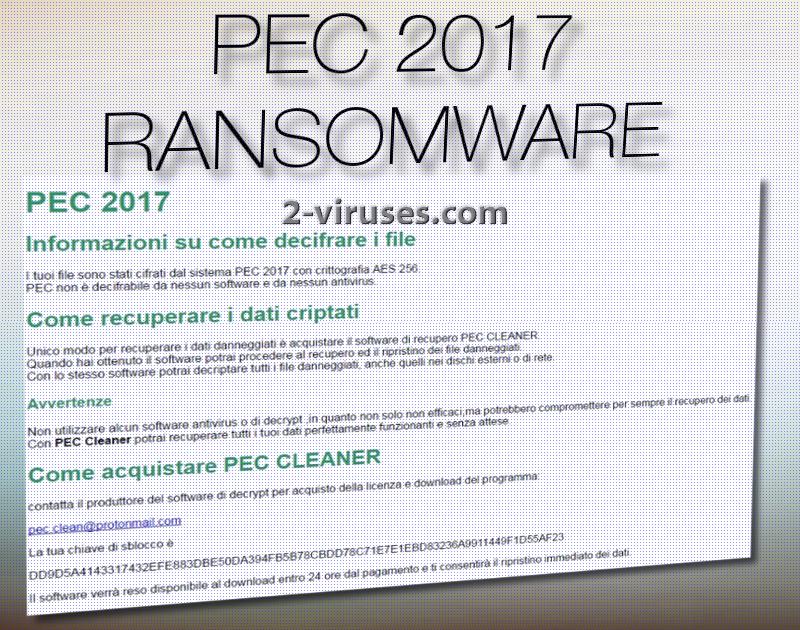
Another file which is related to PEC 2017 ransomware is the one that serves the purpose of the note with instructions. AIUTO_COME_DECIFRARE_FILE.html opens up in browsers and presents text in Italian language. Pec.clean@protonmail com is indicated to the email address that users can contact if they wish to consult with crooks and inform them that they are willing to negotiate. During this conversation, hackers will presumably indicate the exact ransom note as this detail is left out of the .html executable. The ransomware appends .pec extension and wishes victims to abide by hackers’ rules. However, we are stressing out the importance of not sending money to hackers.
The Ransomware will require some participation from the victim if it wishes to start file encryption. Users have to run this file and enable editing which will act as an activation of the executable. You are to never launch applications or files that seem suspicious or out of place. Malicious macros in Word Documents is a very trendy way to infect operating systems with ransomware. From the analysis of the payload, it might be possible that a variant, targeting Mac devices, could also be circulating. Therefore, every Internet surfer should be careful.
Ways to secure files from PEC 2017 ransomware
Speaking of decryption of files that have been appended with .pec extension: there is no positive news. A free decryption tool is yet to be generated. However, there are other options that could help you restore data. For instance, you can check whether Shadow Volume Copies have been influenced/deleted. Of course, if you have stored your files in other locations than your hard drive, you are a very lucky user. All you have to do is get rid of the infection and move on to the retrieval of files from the online storage/flash drive that holds your data.
Before that, we advise you to run a full security scan with an anti-malware tool. Spyhunter, Malwarebytes and Hitman should have no issue in detecting a malicious application. For more information about decryption/removal, pay attention to the part below the paragraph about distribution.
How does PEC 2017 ransomware spread?
PEC 2017 crypto-virus will presumably target users with a campaign of malicious spam letters. Messages that discuss certain job opportunities or similar content could be the source for this infection as the distributed attachment could be indicated as a CV. We advise people to never open email letters from unknown sources. There is also a possibility to become infected with ransomware from unreliable websites or malicious online advertisements.
Pec 2017 Ransomware quicklinks
- Analysis of PEC 2017 ransomware
- Ways to secure files from PEC 2017 ransomware
- How does PEC 2017 ransomware spread?
- Automatic Malware removal tools
- How to recover PEC 2017 ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover PEC 2017 ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover PEC 2017 ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before PEC 2017 virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of PEC 2017 ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to PEC 2017 virus. You can check other tools here.Step 3. Restore PEC 2017 ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually PEC 2017 virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover PEC 2017 ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.