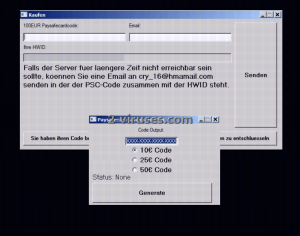
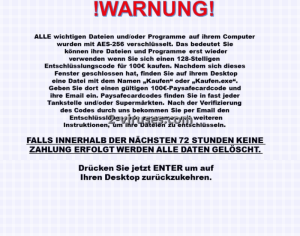
PaySafe Generator, a brand-new ransomware virus has spread its wings and left the nest. Now it is a fresh threat which targets the neat German nation (at least we can make this assumption from the fact that its ransom note is written in this language). Its moves are no different from other ransomware infections, but a more detailed analysis is certainly a must. According to the note, encryption is done with the AES-256 cipher. This symmetric encryption algorithm is a very frequent guest in our articles since crooks choose this specific cipher to encrypt files and make them of no use. This is the leverage that crooks create over victims’ heads: files are unable to be launched and the only way to restore them is to surrender money to the shady programmers. PaySafe Generator virus is not the first variant to be crafted specially for Germans. Versiegelt ransomware is also a quite recent infection that we have analyzed. Since there are no language selections, it might be that if the payload of PaySafe Generator infiltrates into a device with different language preferences, it is presumable that the malicious file will silently remove itself.
About PaySafe Generator Ransomware
Ransomware viruses have a very specific goal: to influence users’ data and demand a ransom for their reconstruction. This basically means that PaySafe Generator virus creates a problem and them demands money to fix it. This illegal way of getting money has become very popular among shady programmers. Developing ransomware viruses is not an extremely difficult task, but another aspect is whether the crafted variants are able to stand the test of time.
Thanks to security researchers that put efforts into such projects like NoMoreRansom, these infections are being taken down one by one. PaySafe Generator virus is a new example, but its profile is very similar to its brothers and sisters. It uses AES-256 encryption to make all of your files completely worthless: no matter how many times you attempt to run the affected data, it won’t budge. PaySafe Generator virus will add a specific extension to all of the files sent to heaven: .cry_. If you want to have a chance in restoring your files, continue on reading this article. Some smart tricks are going to be mentioned in the following parts, and at the very end, a more technical guidelines are made available for your convenience.
How is PaySafe Generator Ransomware Distributed?
The payload of PaySafe Generator virus can be downloaded from file-sharing centers that easily agree to distribute software. For this reason, users can be convinced that they are downloading a reliable products, while in fact, they are welcoming a malicious executable into their system. This variant of ransomware can be hiding behind a seemingly helpful software that deals with PaySafe codes. Always get software from sources that do not randomly accept to feature programs in their domains. We should also mention that PaySafe Generator virus, like the majority of these infections, can be traveling with infectious email letters. Be very careful not to click on messages that seem to be completely out of the ordinary.
How to Decrypt Files Encrypted by PaySafe Generator Ransomware?
The decryption of PaySafe Generator virus is not a settled matter. This ransomware has emerged recently and security researchers did not have enough time to prepare an appropriate decryptor. However, we are convinced that such tool is going to be crafted in the future. Paying the demanded 100 euros is not a smart idea. You will only be wasting resources on a lost cause. Hackers do not have the best reputation when it comes to decrypting files after they have been strongly influenced by algorithms for encryption. They usually disappear with the money and that is the last time you hear from them. If you are wondering about the ways how to become immune to ransomware viruses, you should consider creating copies of your valuable data and keeping it in trustworthy backup storages. Before wondering about possible methods for decryption, you should remove PaySafe Generator virus without any delay. Spyhunter or Malwarebytes will help you to successfully pursue this goal.
Paysafe Generator Ransomware quicklinks
- About PaySafe Generator Ransomware
- How is PaySafe Generator Ransomware Distributed?
- How to Decrypt Files Encrypted by PaySafe Generator Ransomware?
- Automatic Malware removal tools
- How to recover PaySafe Generator Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover PaySafe Generator Ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover PaySafe Generator Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before PaySafe Generator Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of PaySafe Generator Ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to PaySafe Generator Ransomware. You can check other tools here.Step 3. Restore PaySafe Generator Ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually PaySafe Generator Ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover PaySafe Generator Ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.