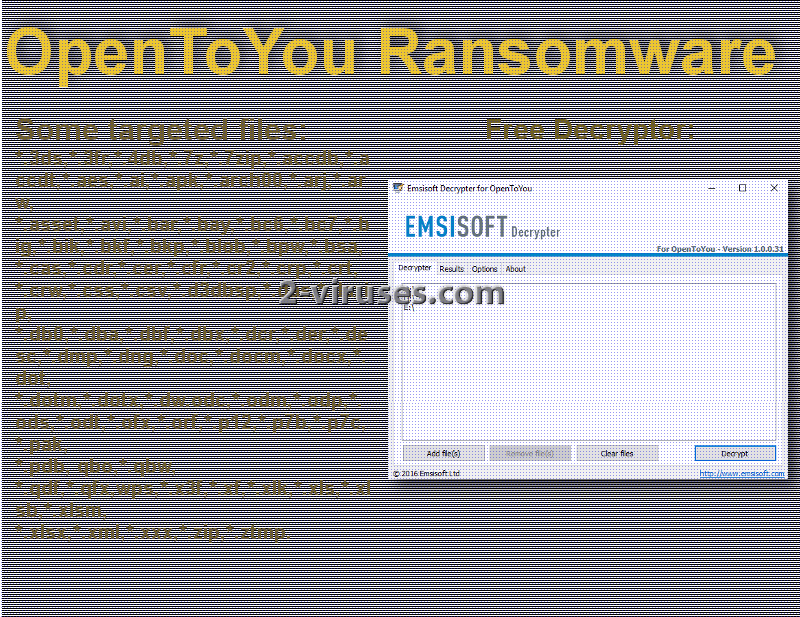
Introducing crypto-ransomware viruses that have been successfully conquered and sent to the grave yard is a real pleasure. OpenToYou virus is a sample that we dare to identify as defeated. We should mention that this infection is not old. Therefore, it is surprising that IT specialists managed to generate an appropriate decryption tool so quickly. Our praises travel to the developers of Emsisoft that introduced the tool for decryption just a couple of days ago, exactly before the New Years. We guess it is better to begin a new year with a fresh slate instead of battling demons from the past. Anyway, OpenToYou crypto-ransomware virus was noticed to infect devices and encrypt various types of data with RC4 cipher. The email contact left to contact the hackers is [email protected]. Despite being curious about what the hackers behind this attack have to say, you should not send them a letter. No amount of begging or threatening will force shady programmers to give away the secrets of decryption. Luckily, OpenToYou virus has been figured out and you can download the decryptor, constructed by Emsisoft.
What can more can we state about OpenToYou ransomware?
OpenToYou virus is put in the same group as any other crypto-ransomware. It is not picky when it comes to files that are suitable for its initiated encryption: an impressive (and disturbing) number of files can be selected to be encoded with RC4 nightmare. Nevertheless, OpenToYou virus might have been not a complicated example since security researchers did craft a functional and free tool, meant to restore the ruined data. Victims have indicated that all sorts of files were corrupted: from .doc, .docm, .docx, .odt, .png, .jpg to a few hundreds of other extensions that almost every files has.
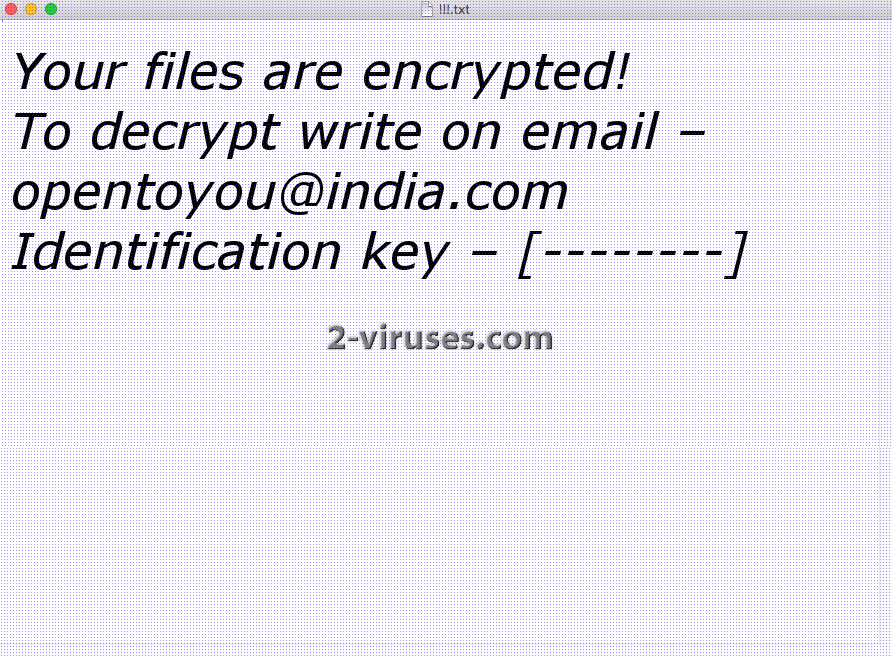
The research about OpenToYou virus also discovered that even those files that did not have any extensions were selected for encryption. To separate the encoded data from the normal executables, every piece of data is going to be appended with [email protected] email address of the hackers. We guess this is another encouragement to contact the creators of OpenToYou ransomware and learn their true intentions, since the presented ransom is not that informative (its called !!!.txt). The message from hackers is going to be seen in two places: as a new background and in the .txt executable. The latter one is also going to contain an original identification key which will be different for every victim of OpenToYou ransomware.
However, even though the ransomware poses a threat to a lot of file types, it is important where in the system is the executable stored. OpenToYou virus seems to avoid some folders and leave its data intact. Examples of such categories: Program Files, Intel, Boot, PerfLogs, Driver, Windows, Logs and couple of others. This means that data in these sections is safe from this ransomware infection. However, data in other folders is more than available for encryption.
Good news: you can decrypt files that have been corrupted by OpenToYou ransomware
OpenToYou virus can be added to the variants that have been cracked: you can download a free tool for decryption from Emsisoft official website. If you are having trouble detecting the exact place, simply click here and we will redirect you to a proper part. This means that if you are infected with OpenToYou ransomware, you won’t have to suffer from majors financial or data losses. However, this positive news cannot be applied to all of the ransomware around. Some of them are difficult to crack. That means that it is important to know appropriate ways how to protect your data from algorithms for encryption. If you have your precious files stored in backup storages, you won’t care if their originals will get encrypted: you will be able to retrieve copies of those files that function just fine.
Aspects, concerning the transmission of OpenToYou ransomware
It is possible that the payload of OpenToYou ransomware is distributed in malicious email letters. This a tip for the future as well: never open letters that are announced to be extremely urgent, but their grammatical mistakes and email address indicate that this might not be a reliable letter. Most of the time, email letters will contain an attachment that you will have to download in order to get infected with a ransomware. However, new research discovered that hackers are able to infect people after they simply open the emails they receive.
Spyhunter are the professional tools you have been missing: these anti-malware programs will automatically take care of the OpenToYou ransomware. Further sections explain manual removal and decryption, but that should not concern you since you should take advantage of the tool, generated by Emsisoft.
Opentoyou Ransomware quicklinks
- What can more can we state about OpenToYou ransomware?
- Good news: you can decrypt files that have been corrupted by OpenToYou ransomware
- Aspects, concerning the transmission of OpenToYou ransomware
- Automatic Malware removal tools
- How to recover OpenToYou ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover OpenToYou ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover OpenToYou ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before OpenToYou ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of OpenToYou ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to OpenToYou ransomware. You can check other tools here.Step 3. Restore OpenToYou ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually OpenToYou ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover OpenToYou ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








