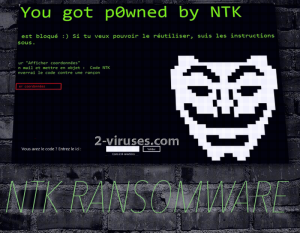
‘You got p0wned by NTK’ is the statement, witnessed by victims of NTK ransomware. Many samples from this malware category incorporate the strategy of locking users’ systems from access, but certainly not all of them. NTK virus is one of those infections that do keep the entire system as a hostage. This repression cannot be welcomed positively: victims will have to immediately consider possible methods of escaping this lock screen, featuring an icon of anonymous group. Surprisingly, we are unsure whether this ransomware goes that extra mile to encrypt files, but there are certain signs to suggest that NTK virus does not include file encryption or algorithms for encryption into its mix. If it would, we are sure that there would be at least a mention of corrupted files in the ransom note. The actual content of the message indicates that an infected device is locked and specific instructions have to be followed to be able to fully load the system.
Particular features of NTK ransomware
NTK sample is not the only ransomware-product that does not actually encrypt files but rather base its threats on the difficulties that people can face because their systems won’t load up properly. Victims will be stuck with an awkward image of a ransom, written in the French language. Because of this characteristic, it could be assumed that French-speaking users are the main audience to be exposed to NTK ransomware. However, this is not confirmed and basically anyone can find themselves mired down. It is very unfortunate to become labeled as a victim of a ransomware and we do express expectations that our visitors will do everything in their power to steer clear of such disruptive viruses. Unfortunately, ransomware is thriving and we are forced to watch over a never-ending production of such infections.
NTK virus commands its victims to follow a three-step instructions to receive a code to unlock their systems. Firstly, they are urged to click on ‘Show Coordinates’ button in the ransom note which is supposed to provide information about the email address that victims are advised to contact. Your sent message is required to contain such a text: NTK Code. Then, if the negotiation goes exactly how hackers anticipated, they allegedly will provide victims with the necessary password to unlock their devices. Would you trust these shady programmers to be true to their word? We certainly would not find such people as exemplary representatives of efficiency and faithfulness. At the end of the day, crooks are only after money, and after you make a transaction of bitcoins to their wallet, you will no longer interest them. It is a frequent tragedy that people convert their money into bitcoins, make transactions but are forsaken by the hackers that made promises to be merciful if victims pay. We are discouraging you from sending the ransom: there might be other ways to unlock your device and destroy every strain of NTK ransomware.
Techniques to become immune to ransomware infections
Even though NTK ransomware does not appear to be encrypting files (this might change), but other variants do. If you wish to secure your data from getting tampered with, you are advised to upload it in more than one location. This will allow you to retrieve your files from a secondary source in case the original versions are ruined by algorithms for encryption. Various online storages will do just fine, but you can also simply keep your valuable data in USB flash drives.
Nuances of NTK ransomware and its propagation
Creators of NTK ransomware could be exploiting all of the popular methods to distribute their beloved project. It might be transmitted even via social networking sites. You might have noticed that sometimes users get tagged in bizarre posts or you might have received an odd message from your friends. In addition to that, malicious executables can reach you through misleading email letters that are sent with the intention of convincing users to download attachments inside them. If you value your security and would not appreciate seeing your device jeopardized, we are recommending you to regularly clean your email inboxes from spam. Exploit kits can also be used to affect certain websites in order to transform them into distributors of ransomware as well. As you can see, NTK virus can be lurking anywhere. You are forced to face the music and keep your potentially dangerous activity to a minimum.
If NTK virus has managed to announce its existence, then you should remove it from your system as soon as possible. You can reboot your computer in a Safe Mode and proceed with its elimiantion from there. Spyhunter or Hitman will help you to remove the ransomware without any issues. In case this version starts encoding data, we also append instructions for file-recovery. Step-by-step guide for a manual removal are also included.
Ntk Ransomware quicklinks
- Particular features of NTK ransomware
- Techniques to become immune to ransomware infections
- Nuances of NTK ransomware and its propagation
- Automatic Malware removal tools
- How to recover NTK ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover NTK ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover NTK ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before NTK virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of NTK ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to NTK virus. You can check other tools here.Step 3. Restore NTK ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually NTK virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover NTK ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.









