NM4 ransomware virus is a well-designed malware infection that is focused on ciphering users’ files with a complicated combination of algorithms. NM4 virus belongs to the family of ransomware variants that employ both AES and RSA encryption to complicate the decryption process of electronic data, the same as RobinHood ransomware or Diablo6 Ransomware. This kind of ransomware infections proved to be extremely dangerous and difficult to decrypt.
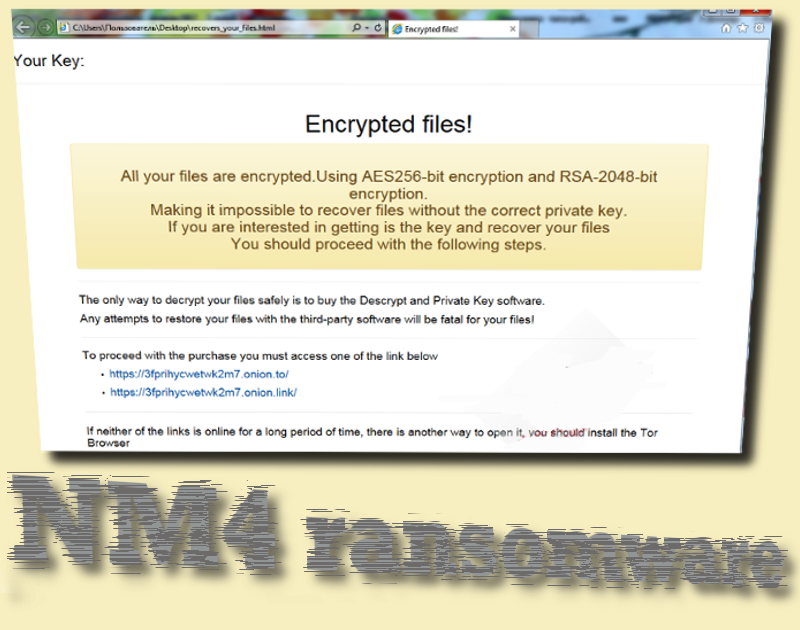
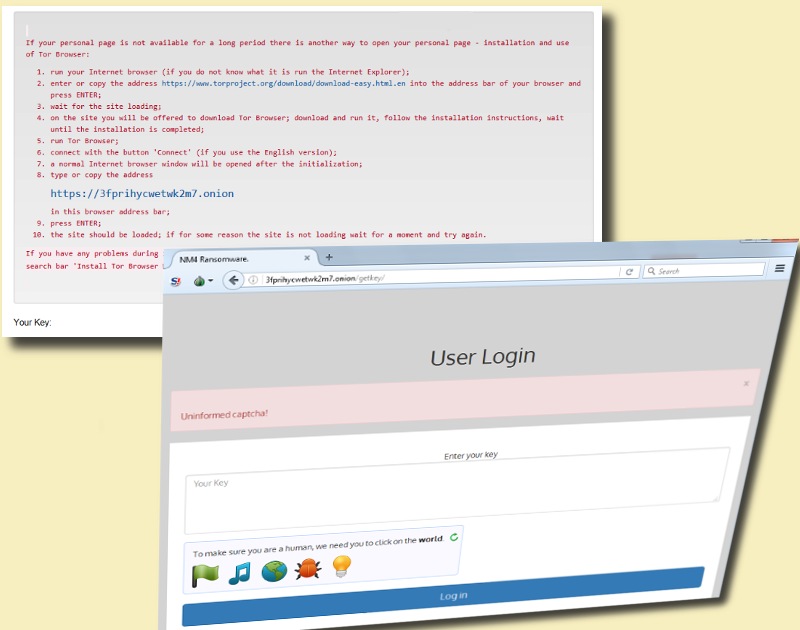
This specific piece of malware works together with two websites that can only be opened by TOR browser. This is another feature that could be related with many other infections that present their instructions for payment in html files, leading to online domains. Recovers_your_files.html executable is placed on victims’ desktops. If this file is launched, it will automatically open a website in your preferred browser (Internet Explorer or any other program). However, the presented note will instruct people to enter the two TOR-supported sites.
NM4 ransomware: main features discussed
NM4 ransomware was discovered earlier this month and as disclosed in a Twitter post is adding a .nm4 extension to encrypted files. It is believed that NM4 is an updated version of NMoneira, a.k.a. AiraCrop virus. Researchers from TripWire believe that it is a Version 4 of NMoneira ransomware.
Before NM4 crypto-virus can complete encryption with the two ciphers for encryption, it has to gain persistence in a device. In order to do this, the payload has to be secretively installed into an operating system. From that point forward, the malicious executable will aim to insert entries into Windows Registry Keys. This alteration will automatically launch NM4 virus after users turn on their devices. It is possible to notice a presence of a ransomware infection in Windows Task Manager, but this search is complicated by the fact that malicious executables can be posing as legitimate processes.
However, if malware has taken root into an operating system, it will suffer from irregularities like slowly-running applications. Windows Task Manager can indicate a high-percentage of utilized CPU resources. Once NM4 virus will obtain a position it requires, it will presumably contact its C&C server to exchange information. Then, encryption, supported by AES-256 and RSA-2048 ciphers, will have the perfect chance to take place. Malware will presumably choose from different files that will become a part of the encoded data. Ruined executables will feature an original extension, called .NM4 which is the reason behind the title of this ransomware infection.
The authors are not newbies in the business of ransomware. Their first sample was called R ransomware and they both demand to make a donation in exchange for the decryption key. While R infection required 2 BTC, hackers raised their price with the new variant. NM4 ransomware instructs people to pay 3 BTC which is approximately 3870.90 US dollars. This is a rather steep price and you should not make a transaction to the indicated bitcoin wallet. You will merely be offering financial support to hackers and giving them more opportunities to create additional ransomware viruses.
NM4 ransomware and the decryption options
NM4 virus is not decryptable at the moment. However, it might be that security researchers will generate a free tool for decryption. Until then, you are advised not to pay the ransom. Instead, you should get rid of this malware and continue with other possible tricks to restore your data. Simply run security scans with anti-malware tools like Spyhunter, Malwarebytes or Hitman and they will show which malicious applications need to be removed. Only after eliminating the malicious payload can you attempt to recover files. You should check whether Shadow Volume Copies have been destroyed. Additionally, there is a chance that universal file-recovery tools will recover some part of the data, marked with .NM4 extension.
What could be the reason for NM4 ransomware?
NM4 virus could use spam letter for its distribution. If you receive an email message from allegedly legitimate facilities that urge you to follow a link or to download an attachment, you should check this letter for suspicious details. If the email address that the message originated looks rogue, you should not follow its suggestions. The same applies if the letter contains a lot of grammatical mistakes or invites you to participate in activities that you did not sign up for. Additionally, try to surf more safely and avoid visiting domains that engage in suspicious services.
Nm4 Ransomware quicklinks
- NM4 ransomware: main features discussed
- NM4 ransomware and the decryption options
- What could be the reason for NM4 ransomware?
- Automatic Malware removal tools
- How to recover NM4 ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover NM4 ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover NM4 ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before NM4 virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of NM4 ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to NM4 virus. You can check other tools here.Step 3. Restore NM4 ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually NM4 virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover NM4 ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








