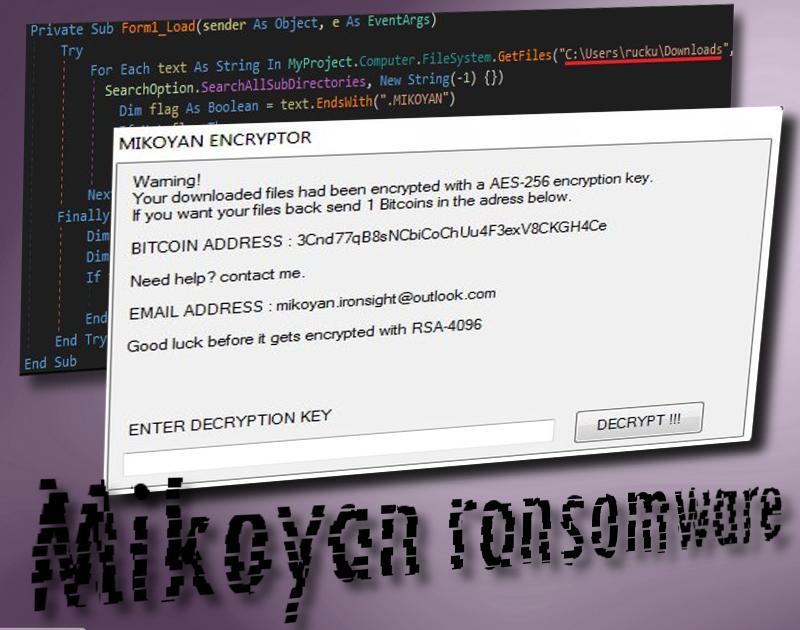
Mikoyan ransomware virus is one of the infections that function with carefully selected algorithms for encryption: sometimes a combination of ciphers is noticed. The title of this malware derives from the extension that is appended to the files that have become spoiled. .MIKOYAN mark is indicated to be preset as an additional extension after the original title of the encrypted files. AES-256 is chosen to turn files completely impractical and requiring decryption. Exactly 1 BTC is the requested ransom and once victims give up and send it to the crooks’ bitcoin wallet, they are welcome to announce about their decision in an email to [email protected] address. If users refuse to pay, the ruined data is explained to be re-encrypted with RSA-4096 which is not a common cipher to see.
How to recognize a Mikoyan ransomware?
Thankfully, we can walk you through the decryption process. Mikoyan was concluded one of those infections that contain significant errors in their structure or generate weak encryption. Considering this, security researchers renewed their Stupid Decrypter for the sake of it being adjusted to recovering files that have been corrupted by this ransomware infection. Surprisingly, the virus is only after executables, photos, videos, music records and other material that is found in one specific folder. “Downloads” folder which is located in the C disc is the main source for files to encode.
As for the payload of Mikoyan, MIKOYAN.exe file is concluded to be the malicious source for harmful activity. Compiler for it is Microsoft visual C# v7.0 / Basic .NET. Once inside, it will issue changes in Windows Registry Keys to gain persistence and be launched automatically with all of the programs that are set to be opened after a reboot. Once the content of Downloads folder is fully encrypted, the infection will launch a Mikoyan Encryptor application which will serve as the ransom note for the victims. As we have already explained, AES-256 cipher is exploited to corrupt data and 1 BTC (about 1466.21 US Dollars).
Taking into account the fact that the virus is not an elaborate infection, the demanded ransom is way too high. There is no reason to pay the fee as users can easily decrypt data by running the free decryption tool. We advise you to do so and never consider paying crooks. Giving in to the demands only encourages hackers to continue on creating ransomware samples. Before you begin the decryption process, we suggest removing every trace of Mikoyan virus. If it is still inside during the recovery of data, it might influence this procedure negatively. Run a scan with Spyhunter, Plumbytes or Hitman and these security tools will remove it.
Ransomware prevention
Do you wish to find out how ransomware infections can be defeated without a fight? All you have to do is simply have backups for your files. In case a crypto-virus ruins your data from hard drives, you will easily have another source for it. This is a much recommended action to do, especially if you have a lot of valuable data that you cannot afford to lose. Choose from a variety of backup storages that are available online, or simply place your files in an USB flash drive which will also serve as a safe location. Tip: do not keep your USB connected to your PC at all times since ransomware infections have been noticed to encrypt data that is linked with the infected device.
Distribution of ransomware infections like Mikoyan virus
Crooks have established a certain tactics for ransomware transmission. Malicious executables are usually distributed in forms of harmlessly looking files that are appended as attachments to emails. This spam is a very relevant problem at the moment and we hope you do not become involved in a malicious campaign. Always check whether senders’ of letters are recognizable and that the content of the messages are not suspicious. Additionally, be careful while browsing the Internet as a lot of websites would be modified to initiate drive-by downloads and infect you with a malicious payload.
Mikoyan Ransomware quicklinks
- How to recognize a Mikoyan ransomware?
- Ransomware prevention
- Distribution of ransomware infections like Mikoyan virus
- Automatic Malware removal tools
- How to recover Mikoyan ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Mikoyan ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Mikoyan ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Mikoyan virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Mikoyan ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Mikoyan virus. You can check other tools here.Step 3. Restore Mikoyan ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Mikoyan virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Mikoyan ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.