A new crypto-ransomware figure has emerged from the gloom of hackers’ lair. The first report about this sample reached security researchers a couple of days ago and the victim provided primary information about the infection. It was decided to name the incoming ransomware variant LoveServer due to an email address, indicated in the ransom note. You should not look forward to flowers, chocolates and other lovey-dovey stuff since LoveServer is not interested in expressing affection in any possible form. Prioritized actions include infiltration into users’ devices and secretive deeds that follow. Not a lot of information can be presented, but some general aspects about LoveServer virus are to be revealed in this article. Virus uses an unknown cipher for encryption of files and transfers this data into a one locked file. Former variants of similar viruses indicate [email protected] email address as the one to contact. LoveServer virus submits [email protected] address and similarities between these two are evident.
Further examination of LoveServer ransomware
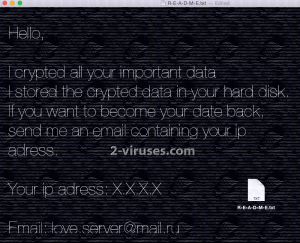
LoveServer differs from other samples of ransomware viruses with its tendency to encrypt files and combine them all in one, usually gigantic, file that is going to store the encrypted data. Folders that used to contain all sorts of executables of documents, photos, music, videos or other files look deserted as they appear to be wiped out by the LoveServer virus. The main file that the ransomware constructs does not have an original extension: in fact, it does not feature an extension at all. It is simply called “BACKUP DONT DELETE” to suggest that the deletion of this huge file would result in a permanent loss of your data. The ransomware also drops R-E-A-D-M-E.txt executable which contains a short message from the creators of LoveServer virus. Their implications reveal the main aspects about the infection: files suffered from encryption and are stored in one big file with no extension. As this ransomware is quite recent, researchers have not received enough information to construct a more clear image of this variant. Despite not being able to elaborate more on the technical side of the LoveSever, we can surely advise you to never contact crooks and become involved in their affairs. In the ransom note, victims are expected to send their IP address via email for the sake of hackers giving more specific instructions for further actions.
Is it possible to retrieve files that are encrypted and compressed by LoveServer ransomware?
Not enough analysis has been done about LoveServer virus to determine the possible methods for file decryption. Since ransomware not only encrypts files, but compresses them into one executable, the possible decryption might be a complex matter. However, you should never initiate conversations with crooks by providing them with the information they demand. You will only be wasting money on their requested ransom. Many victims that follow the instructions and send BTC to hackers for the decryption of their files are left disappointed. Hackers do not bother too much about whether their provided codes/software functions and manages to restore all of the encoded data. That is one of the reasons why paying the ransom is not wise. In addition to that, you will be providing financial support to these people and they might create more ransomware viruses in the future.
Journey of LoveServer ransomware from the hackers to your device
An exact trick to get LoveServer virus distributed is not recognized. It is possible to download a payload of ransomware straight from your email inbox. Letters that are uploaded with malicious executables frequently travel around accounts and are indicated as one of the leading sources of ransomware. If you are frightened by these viruses, never open random letters even though they are scaring you with urgent topics/issues. Recent researches suggest that it is possible to get infected even by opening an infectious email letter.
Spyhunter or Malwarebytes are anti-malware fighters that won’t leave any malware viruses in your system. A thorough scan should inform you about the state of your device and introduce possible solutions. Incorrect manual removal of ransomware viruses can have a negative impact on your device. For this reason, you are more advised to exploit reliable programs for the elimination process.
Loveserver Ransomware quicklinks
- Further examination of LoveServer ransomware
- Is it possible to retrieve files that are encrypted and compressed by LoveServer ransomware?
- Journey of LoveServer ransomware from the hackers to your device
- Automatic Malware removal tools
- How to recover LoveServer ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover LoveServer ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover LoveServer ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before LoveServer ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of LoveServer virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to LoveServer ransomware. You can check other tools here.Step 3. Restore LoveServer ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually LoveServer virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover LoveServer ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








