LightningCrypt ransomware virus is a dreadful infection that exploits sophisticated cryptography to prevent digital files from opening. Specifically, this infection has selected AES algorithm to carry out the process of file-encoding. This virus does not appear to be a dominating infection, but people still need to learn to recognize it. Ransomware does target all of the widely-utilized executables, from potentially important Word documents to sentimental photos that are saved in .jpg or .png formats. As soon as such files are ruined, this data will stand out because of its .LIGHTNING extension. Also, on victims’ desktops, a LightningCrypt_Recover_Instructions.txt file will be noticed.
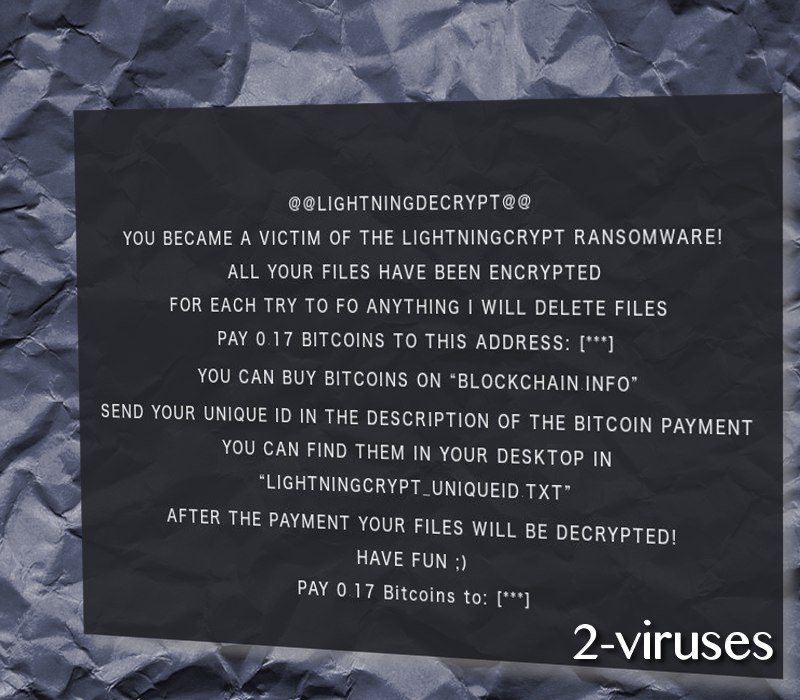
The infection’s aim is to force people to send 0.17 BTC to an indicated bitcoin wallet. 423.78 US Dollars should not be voluntarily send to crooks’ accounts as this will only encourage them to pursue ransomware projects in the future. At the moment, there is no way of restoring virtual data that the infection might have corrupted, but we do insist to never pay the demanded ransoms. It is possible that security researchers are currently working on a file-recovery tool and will introduce it during the next couple of days or weeks. In general, hackers can trick you and never produce a decryption key.

A payload of LightningCrypt virus has been investigated by our team of researchers and we have noticed certain tendencies. According to our analysis, one of the presumable payloads is a chkdsk.exe file. This source of malicious behaviour will commence or will be able to commence a number of suspicious actions, including the conventional configurations in Windows Registry Keys, opening files with dangerous rights and contacting hosts. It also appears that the payload will opt to send DNS request to an IP address from Germany. Could this indicate that authors of this infection are from the latter country? Arizonacode.bplaced.net website is the domain that payload attempts to connect to.
How many people have already become victims of this infection is unknown. However, we are not noticing any massive numbers of reports that would require assistance in the file-recovery process. If such a necessity takes place, we do hope that security researchers will be able to find ways of helping people get back their files without having to pay the ransom.
We can play our part by recommending a couple of techniques for file-recovery.The instant options to try after a ransomware hits your device will be discussed in this paragraph. First of all, you should check whether your Shadow Volume Copies are still intact. If they are, then this is one of the ways of restoring data. Additionally, there are a number of universal tools that could be functional. To learn more about the possible ways of restoring data, scroll down to the very end of the page. The steps of a manual removal are also explained in the same section. However, we do think that it is more effective to get rid of ransomware with anti-malware tools. Spyhunter or Malwarebytes will detect sources of malicious behaviour and offer a clean elimination process. Consider this option very carefully.
How are ransomware infections usually distributed? The answer has to be divided into a couple of parts. Spam campaigns are the first distribution method that hackers exploit for transmission of malicious executables. Deceptive email letters can end up in one’s email account and insist that it is crucial to download an appended attachment. We discourage you from opening such files as they could contain malicious macros. Furthermore, avoiding following links as well. You could be redirected to unknown websites and have your operating system compromised. Malicious executables have been known to be distributed thanks to drive-by strategy.
Lightningcrypt Ransomware quicklinks
- Automatic Malware removal tools
- How to recover LightningCrypt ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover LightningCrypt ransomware encrypted files

Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover LightningCrypt ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before LightningCrypt ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of LightningCrypt ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to LightningCrypt ransomware. You can check other tools here.Step 3. Restore LightningCrypt ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually LightningCrypt ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover LightningCrypt ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








