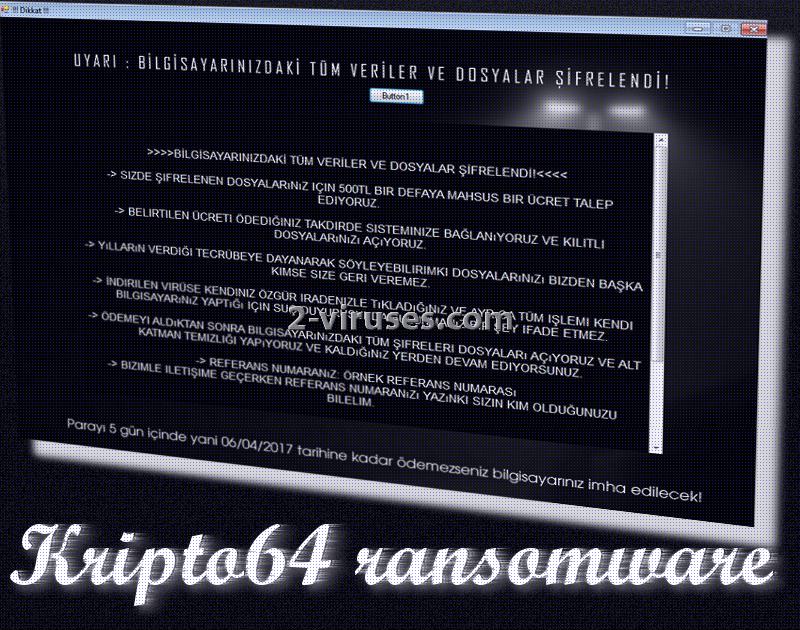
Kripto64 is a recent Turkish crypto-virus which explains its demands in this language. Since over 70 million people understand or regard it as their mother-tongue, the ransomware should not have any difficulties in finding victims to inflict on. Researchers have assigned this sample to the group of HiddenTear projects. This means that Kripto64 is an open-source virus: sometimes, this type of infection is less complex and developers’ mission of file-decryption becomes achievable. Kripto64 is selective when it comes to operating systems it wishes to invade: mainly devices, running 64-bit Windows. Currently, there is not a lot of information about this variant, only that it targets Turkish-speaking part of the Internet community and displays a screen-locker with threats and instructions. It requires a 500TL (Turkish Lira) which is, if converted to US dollars, 134.69.
Kripto64 ransomware: main aspects to consider
The payload of Kripto64 virus was ran through a number of security tools. Some of them detected this infection to be a variant of Ransom:MSIL/Ryzerlo. These are also based on HiddenTear open source codes. This theory is not yet confirmed since the ransomware requires more testing. However, if this is true, then the virus should target to encrypt files from UserProfile Desktop file path. The payload which was analyzed was named a11edd5e5ad59ecfe98158727a951cf2.virus, but its original filename is Kripto.exe. This is way the infection is referred to as Kripto with an addition of 64, meaning that it will target 64-bit Windows OS.
However, while reading the instructions that Kripto64 virus indicates in its ransom note, we cannot help but wonder that this variant is unfinished. There might be a .text file with additional instructions because the screen-locker does not include information, necessary to make a transaction of 500TL. It also does not feature an email address which could be used to contact hackers behind this Turkish crypto-virus. Therefore, with the provided information, it is not even possible for victims to pay the ransom and save their files.
To make matters worse, this ransomware threatens to disrupt affected devices even further and to delete the private key for decryption. When will such a drastic action take place? Victims will have a specific deadline to make a transaction which differs according to the date of becoming infected. If your files have become corrupted and the screen is locked with a message from Kripto64 virus, you have to act fast before the ransomware permanently deletes files.
What should you do? To escape the screen-locker, you are advised to restart your computer and run it in a Safe Mode. Then, you should copy all of the files that Kripto64 has influenced with encryption and upload to an alternative location. Then, proceed to the elimination of this ransomware. The most optimal decision would be to run a thorough security scan with a respectable anti-malware tool like Spyhunter, Malwarebytes or Hitman. Manually removing ransomware can be risky as you can damage your system.
Suggestions for completing the file-decryption process
For now, security researchers have not produced a tool to complete the decryption process. Kripto64 infection is not decryptable at this time. However, if the situation changes, we are sure to inform you. Good news is that there are alternative ways to recover files. For example, you can try file-recovery tools that have been designed before Kripto64 was released. In addition, you should check whether this Turkish variant deletes Shadow Volume Copies or leaves them. However, if you have stored your files in backup storage, you can simply delete the infection and retrieve files from the alternative locations.
Krypto64 ransomware: how does it spread?
This Turkish variant might use the most widely-known tricks that ransomware exploits for distribution. One of them: spam email campaigns. It is possible that your email inbox can become a source of ransomware. How? Well, if you open letters from the Spam category and download attachments inside. Additionally, exploit kits can also help distribute payloads of crypto-viruses. By exploring bizarre websites, you might unknowingly become compromised. After a ransomware gets inside, its stealthy mode allows it to remain undetected.
Kripto64 Ransomware quicklinks
- Kripto64 ransomware: main aspects to consider
- Suggestions for completing the file-decryption process
- Krypto64 ransomware: how does it spread?
- Automatic Malware removal tools
- How to recover Kripto64 ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Kripto64 ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Kripto64 ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Kripto64 virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Kripto64 ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Kripto64 virus. You can check other tools here.Step 3. Restore Kripto64 ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Kripto64 virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Kripto64 ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.