KKK ransomware virus is an offensive variant as it features a reprehensible symbol of the KuKlux Klan. From the technical point of view, the infection is not fully completed and is labeled as still in the stage of development. A variant of Jigsaw has been noticed to proceed with a .kkk extension, meant to be appended to encrypted digital data, but researchers have singled this new sample as a separate crypto-virus. As it has been discovered, it is based on the open source Hidden Tear project which could indicate that an AES algorithm for encoding is selected. As it appears, variant only encrypts files that have are found on the desktop.
More than a few anti-virus tools have clearly indicated that the suspected payload of this infection is malicious. From the looks of it, the file is shaped to look as if a program of Facebook. Analysis of Facebook.exe file showed that its creators included rather misleading descriptions into its properties: FaceBook app for computer. This statement is obviously false as this executable is actually a source of malicious activity.
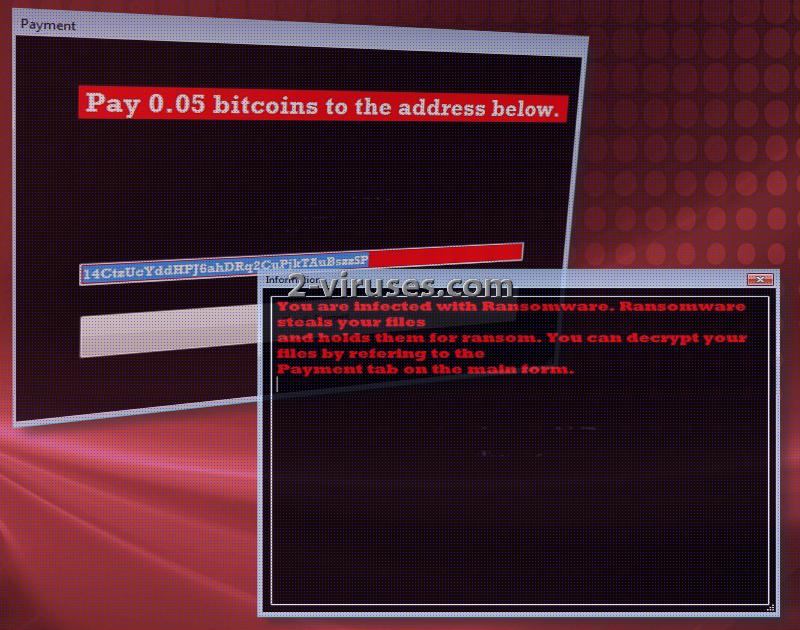
The main window that should get loaded after files are corrupted and joined by .kkk extension explains the situation rather briefly. Victims are instructed to click on the “Information” section to learn that their operating systems are under attack by a ransomware infection. It directs victims to the “Payment” section that indicates that 0.05 BTC is demanded as the ransom for file-decryption. This sum equals 142.35 dollars at the moment. A hackers’ bitcoin wallet is also mentioned.
Never dare to pay the ransoms that authors of crypto-viruses choose to demand. Even if you do send the required fee, you might not be provided with a functional software of a key for decryption. Crooks are unreliable and negotiations should not take place. Especially, victims should refuse to abide by the rules that are raised by hackers.
Additionally, it has been mentioned that the virus can launch a website with a timer. This means that victims will have a limited amount of time to react to the ransomware before the crypto-virus either deletes all encrypted data or destroys the decryption key. However, such threats are not included into the provided information.
Security researchers are not indicating that this infection would be an extremely well-structured or novel variant. The only thing that makes it stand out from the other infections is that hackers dared to incorporate a highly disrespectful sign.
File-decryption, transmission of ransomware viruses and their removal
Since this variant is still in development, hackers should not be distributing it just yet. If anything changes, we will let you know. Before security researchers indicate to have created a free tool for file-decryption, you could try to restore files in other ways. For instance, if the crypto-virus would not affect Shadow Volume Copies, then it would be possible to restore data. Additionally, you can try recovering executables with the help from file-recovery applications that already exist.
Of course, if you were clever enough, you might have stored your digital data in more than one location. Therefore, even if the samples from your hard drive are no longer available for usage, you still can find them in a storage. You can upload files into online backup storages or simply use your USB flash drive as a free container.
Before you try to recover files, it is extremely important to get rid of the ransomware first. This elimination can be done either manually, or with Spyhunter or Hitman. The latter tools are indicated as the better choice for ransomware-removal.
We can predict the most plausible techniques that ransomware can exploit for distribution. One of the most popular strategies is to launch malicious spam campaigns. They will distribute email letters that contain payloads of crypto-viruses. On the other hand, such infections can travel because of vulnerable websites and tainted online advertisements.
Kkk Virus quicklinks
- File-decryption, transmission of ransomware viruses and their removal
- Automatic Malware removal tools
- How to recover KKK virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover KKK virus encrypted files

Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover KKK virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before KKK virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of KKK virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to KKK virus. You can check other tools here.Step 3. Restore KKK virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually KKK virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover KKK virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.