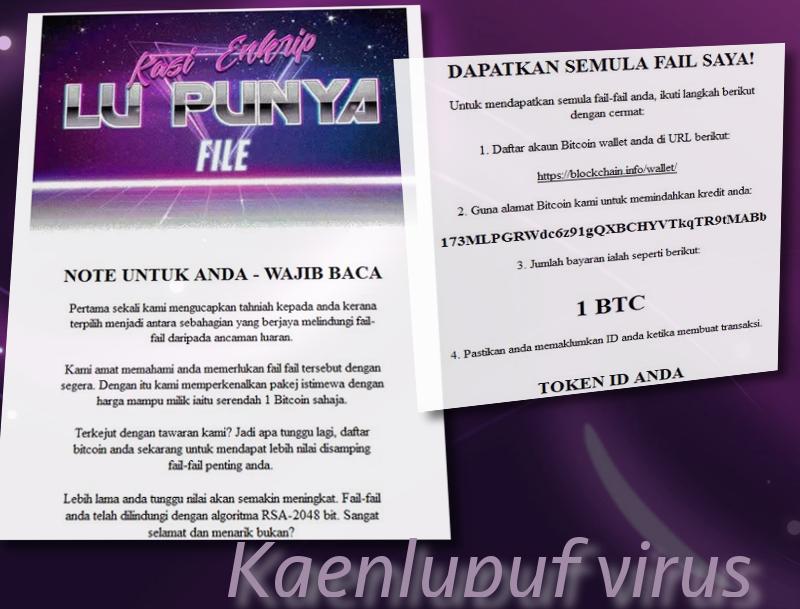
Kaenlupuf crypto-virus emerges from Malaysia and its ransom-note is written in the Malay-language. Surprisingly, the presented kaenlupuf-note is written in an unexpectedly friendly manner. Despite the fact that the files are corrupted with AES-128 cipher, the hackers responsible for this variant attempt to spin this situation as an opportunity to get a “special package”. Upon registering in the alleged service, users will not only decrypt their files, but will receive protection in the future. Of course, these are just empty words. Kaenlupuf is a deceptive ransomware infection and it is only interested in receiving profit from file-encryption. Since the ransom is written in the Malay-language, we suspect that only users that would understand this language are targeted. In addition to that, this virus places another text file which will suggest an opportunity of joining a top-secret group called KAENLUPUF.
Report about Kaenlupuf virus
Kaenlupuf claims that it exploits RSA-2048 cipher, but it is more presumably to corrupt files with AES-128 algorithm. However, since the file that initiates encryption is called ajaw-rsa.exe, it could be debated which algorithm is actually put to use. It mostly targets Windows operating systems and tries to intimate people to purchase 1 BTC and send it to the provided bitcoin wallet: 173MLPGRWdc6z91gQXBCHYVTkqTR9tMABb. 1 BTC is approximately 1174.61 US dollars and 5238.17 Malaysian Ringgits. The distribution of this variant is not considered extremely active, but the threat to become infected remains.
Kaenlupuf is currently in-development, which means that it is only to be functioning fully. We are aware of the existence of this infection, but not a lot of details can be clearly identified just yet. For example, it is yet unknown whether the encrypted data is marked with a unique extension. However, even though knowing whether the Kaenlupuf ransomware modifies filenames, it is not difficult to separate it from other variants.
In one of the images it displays, a huge black-and-white dragon can be noticed. Netsvc.exe file is identified to be the payload of Kaenlupuf virus and it will presumably run in the background. To obtain such a position, the ransomware will have to insert entries into Windows Registry Keys. Take a look at the ransom note which is presented by this ransomware. For you convenience, we have translated it into English language.
IMPORTANT FOR YOU – READ
First of all, we congratulate you on choosing one of the best file-protection from external threats.
We understand that you need the files immediately. We will provide you with a special package at an affordable price for only 1 bitcoin.
Are surprised by our offer? So what are you waiting for, register your bitcoin now to get a valuable addition to your important files.
The longer you wait, the greater the amount will become. Your files are protected by the RSA-2048 algorithm. Very good and interesting, is it not?RETURN MY FILES!
To retrieve your files, follow these steps:
1. Register your account in the google-purse at the following URL:
https://blockchain.info/wallet/
2. Use our bitco-address to transfer the payment:
173MLPGRWdc6z91gQXBCHYVTkqTR9tMABb
3. The amount of payment is as follows:
1 BTC
4. Be sure to report your ID when making a transaction.
YOUR TOKEN ID
Decryption of data, ruined by Kaenlupuf virus
Do not believe the promises that Kaenlupuf virus makes. It is doubtful that your payment will help to get your hands on the decryption key. Hackers do not usually waste their time with the victims after the ransom has been sent. To avoid getting deceived, we discourage you from sending 1 BTC to the specified bitcoin wallet. More appropriate course of action would be to try universal file-recovery tricks, like checking whether this Malaysian variant is programmed to delete Shadow Volume Copies. If that does not work, you can try using various universal tools. More information about these options can be found below.
What does Kaenlupuf virus hijack computer devices?
The payload of Kaenlupuf ransomware can be waiting for you in various places. For example, your email account might be targeted to receive malicious spam letters. Sometimes it is quite easy to separate a reliable message from a fake one, but if you are having any difficulties, we should offer you some tips. Always check whether the email address which is identified as the author is legitimate. Furthermore, the title of the letter should not be messy or incoherent. If you open the received message, you should not be surprised by the amount of errors in the displayed text. Lastly, if an email has an attachment, never open/download them without being certain of its innocence.
Anti-malware tools can help you detect and remove every trace of Kaenlupuf crypto-virus. To keep your device running without any obstacles, we advise you to try Spyhunter or Malwarebytes. To read more about manual removal/file decryption, look down.
Update. Surprisingly, this ransomware has already received attention from security researchers. As a consequence, a free decryption website helps people recover their data. Click here to enter the mentioned domain. As you can see, it requires a password of some sort. This is the ID number you receive from the hackers. Type it in and continue.
Kaenlupuf Virus quicklinks
- Report about Kaenlupuf virus
- Decryption of data, ruined by Kaenlupuf virus
- What does Kaenlupuf virus hijack computer devices?
- Automatic Malware removal tools
- How to recover Kaenlupuf virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Kaenlupuf virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Kaenlupuf virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Kaenlupuf ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Kaenlupuf virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Kaenlupuf ransomware. You can check other tools here.Step 3. Restore Kaenlupuf virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Kaenlupuf ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Kaenlupuf virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.