Internet Security virus is a fake antivirus program that belongs to the family of extremely aggressive rogue parasites. It is a clone of the Internet Security 2012 omitting the year number in the name. It is one more program that displays falsified information and imitates checking your system for infections while in fact it cannot detect anything. The program is installed to a random system through Trojan viruses and it is straight away configured to start automatically when computer is rebooted.
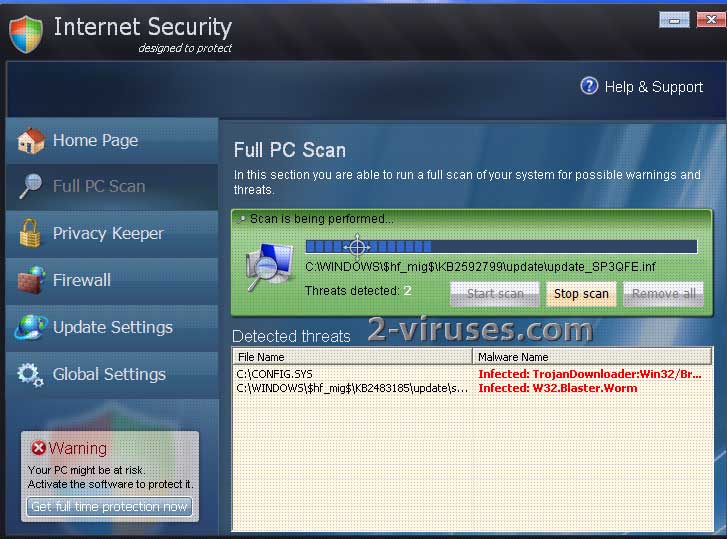
Internet Security virus launches its scanner with every login to Windows. The program imitates looking for infections and warns that your system is badly infected. Unfortunately, since Internet Security is not able to detect real threats, it displays non-existing files and presents them as infections. The program uses generic names of parasites and this way it prevents computer users from getting any information about them. The “parasites” “detected” by this malware include W32.Blaster.Worm, Email-Worm.Brontok, W32/Child-Porn.PROXY/Server, Mal/Generic-A, various TrojanDownloader versions. It is unlikely that any of these parasites are on your system, except, ironically, the TrojanDownloader which downloads Internet Security malware in first place. However, it will not be detected.
In addition, Internet Security scam warns that your system is at risk by displaying various security notifications and pop up ads which inform about system threats and recommend activating Internet Security in order to protect your computer.
You should remove Internet Security virus from your system as soon as you notice it there. Have in mind that this malware can try to block your legitimate antispyware tools and block these executables, it will also kill browsers and most of other applications. However, There are several ways to remove Internet Security from your system without resorting to system reinstal.
Special instructions for removing fake Internet Security
- You will need to kill malware processes before launching any anti-malware program or downloading it. To do so
- Press Start->Run. Enter taskkill /F /IM isecurity.exe in the field and press enter. Repeat this step several times, till malware window closes.
- If the window does not close, try running taskkill /F /IM amsecure.exe . This is an updated file name for the rogue’s 2013 version. It might also be that you are facing a version 2013 Pro, in such a case use taskkill /F /IM indefender.exe.
- Another way is to press ctrl+shift+esc. The command will open task explorer. Normally the latter should be killed by Internet Security malware. However, if you are quick enough to press “End program” button while your PC is busy, you can kill malware process too. Please note that this method is not the most reliable one.
- You can also fake-register malware with the key Y86REW-T75FD5-U9VBF4A or Y86REW-T75FD5-9VB4A and any email.
- Scan your PC with couple decent anti-malware programs to identify really infected files. I recommend spyhunter or Malwarebytes Anti-Malware for that. Delete malware with full version of program or delete the file manually.
- Remove Malware startup entry by launching msconfig and unchecking the malware process from startup list.
Note Internet Security Virus uses multiple process names names now (2013). The names used are : isecurity.exe , amsecure.exe, indefender.exe,tdefender.exe, ildefender.exe, ihdefender.exe. If the window does not closes during steps 2/3, try using these file names.
Video guide of Internet Security removal instructions
Remember that full legitimate anti-malware program like Malwarebytes Anti-Malware or spyhunter can prevent your system from being infected with this kind of infections.
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
One response to “Internet Security virus”