InfinityLock ransomware virus is a new product by extortionists that dream of receiving big profits from their malware infections. However, not everyone can generate such threats like WannaCry or Locky as most of the ransomware viruses are either based on HiddenTear projects or are considered as “junk ransomware” (The rise of low-quality ransomware) because of poor-coding. The payload of this infection is PremiereCrack.exe which is actually a malicious file, pretending to be Adobe Premier Crack (VirusTotal analysis).
Things to learn about InfinityLock crypto-virus
However, this crypto-virus is nor evasive nor professionally-made. Security researchers even claim that it is decryptable. Due to the lack of strong encryption and other features, we could describe this application as similar to WhyCry or BlackSheep ransomware viruses that are not treated as the biggest threats in the cyberspace.
Furthermore, victims of InfinityLock crypto-virus might feel confused because of the fact that this infection does not proceed with a specific extension for encrypted digital data. Instead, it examines CPU of each compromised computer and derives an original extension from devices’ hardware ID (What is hardware identification). Therefore, victims will notice different extensions.
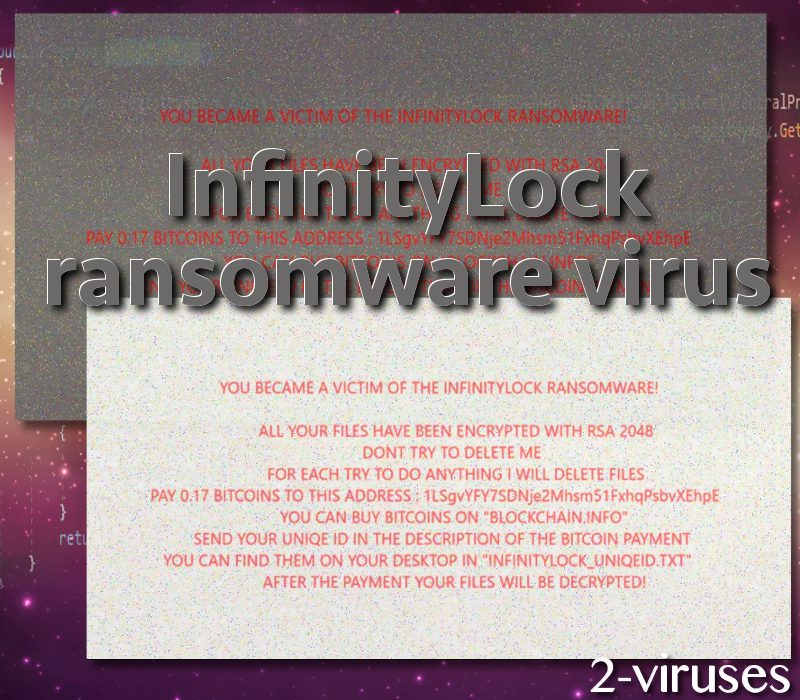
Also, victims desktop background are expected to be modified to feature an original wallpaper. It will contain a text, explaining that digital data has been ruined with RSA-2048 cipher. The demanded ransom is 0.17 BTC which currently equals 675.84 USD. Hackers’ bitcoin wallet, awaiting for transactions, is also mentioned on the desktop image. Every victim is supposed to find INFINITYLOCK_UNIQEID.txt files which will contain original IDs.
InfinityLock crypto-virus will also undergo the same stages that mostly all infections do. First of all, it will find a way to slither inside operating systems. There are multiple methods that the ransomware can exploit to its advantage. No wonder new types of crypto-viruses are being discovered.
First of all, it could be delivered in malicious spam campaigns (Malspam campaigns), urging people to download infectious attachments or visit malware-laden websites. In this case, it is very possible that email letters or pop-ups could be recommending users to download Adobe Premier Crack. Similar suggestions should be disregarded as they can be responsible for stealthy installations of malware. Even though Mac operating systems are more resistant when it comes to malware, even they have become targeted by ransomware.
Decryption, removal and prevention of ransomware viruses
Having your data encrypted is definitely not an enviable situation. However, we do believe that there is away of helping infected users restore their encrypted data. Michael Gillespie has been involved in generation of a number of file-recovery software. Contact him if your files have become encrypted by InfinityLock crypto-malware. There are also other methods to decrypt data, like restoring Shadow Volume Copies or retrieving files from backup storages.
Deciding to upload files into backup storages is a very good idea. If the original versions on your hard drive become encoded, you won’t have to suffer any inconveniences. All you will have to do is get rid of the ransomware using an anti-malware tool and retrieve files from a backup storage. Spyhunter is a scanner that will take care of malware threats. If you do not like backup storages, you can simply upload files into USB flash drives or use other methods (you can find them below).
Ransomware viruses are extremely malicious. They encode files and demand ransoms in exchange of their decryption. Hackers have already earned massive sums of money from these cyber crimes. We hope that you won’t be compromised by similar parasites. For instance, never open or download attachments from unknown email letters.
Your email address could have been involved in a data leakage which revealed you email address to hackers. Therefore, they might have been targeting that account for quite a while, hoping that you will open one of the malspam messages. Additionally, ransomware viruses can also arrive due to improperly protected RDPs. We hope that all of these recommendations will help you to stay malware free.
Infinitylock Ransomware Virus quicklinks
- Things to learn about InfinityLock crypto-virus
- Decryption, removal and prevention of ransomware viruses
- Automatic Malware removal tools
- How to recover InfinityLock ransomware virus encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover InfinityLock ransomware virus encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover InfinityLock ransomware virus encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before InfinityLock ransomware virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of InfinityLock ransomware virus
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to InfinityLock ransomware virus. You can check other tools here.Step 3. Restore InfinityLock ransomware virus affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually InfinityLock ransomware virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover InfinityLock ransomware virus encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








