A common enemy to us all has flared up and demonstrated its true colors. Probably the most fundamental and most important aspect to discuss is the characterization of HugeMe crypto-virus as a ransomware. These accusations are not weakling as this infection has showed essential symptoms of an ransomware threat. This seems to be a currently active variant. Therefore, we advise our visitors to proceed with caution. It has been confirmed that HugeMe infection is based on an open-source project called HiddenTear. An assumption to be made from this fact is that this ransomware is manipulating AES encryption ciphers to use them in the file-encryption process. Threat controls not one, but three email addresses that people supposedly should contact in case of an emergency with HugeMe virus. If you need some assistance with file-decryption and removal, you should move to the end of the article and review the instructions we have appended. However, we do dare to say that reading the full article is beneficial as well.
Creating an image of HugeMe ransomware
HugeMe virus will obviously impact your computer system: it simply depends on whether you are observant enough to notice it in time. Actually, not just anyone can sharply foresee encryption and prevent it from happening. The major downside in these viruses is that they manage to secretive get their affairs in order without alarming the user. For this reason, many people that become infected end up having their data scrambled like a breakfast omelette. As you can guess, it is better to stay safe from ransomware than to be forced to fight it.
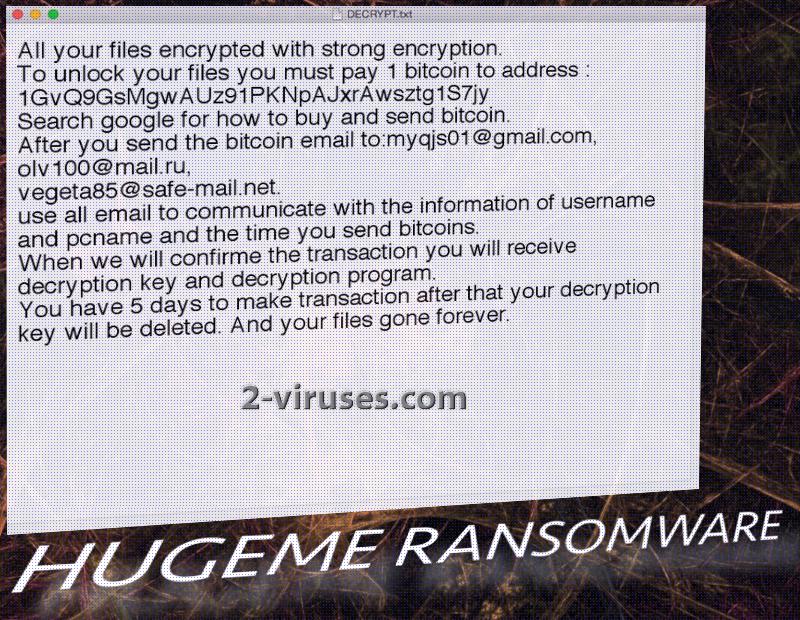
Speaking of HugeMe virus, it will feel no doubt or hesitation with regard to the morality of its course of action. It slithers into devices like a poisonous snake and spreads its venom wherever it manages. Firstly, it will place Hugeme.exe as a payload and its plan is to kick things of by inserting entries in Windows Registry Keys which will be responsible for consistently launching the payload in the background. Then, the ransomware will act-by-the-book and contact its creators via C&C server and after that, it quickly direct its attention to scans, aimed to detect files for encryption. More than one hundred types of files can potentially be ruined for the sake of gaining leverage over the computer owner. Data that suffers from AES cipher is also joined by an .encrypted extension right after its original one. For instance, mytrip.jpg will be noticed as mytrip.jpg.encrypted. In addition to that, the ransomware will also add an DECRYPT_ReadMe.txt file which will encourage people to pay 1 BTC for file-decryption and contact hackers via three email addresses: [email protected]
[email protected] and [email protected]. The message also informs that the victim has only 5 days to make the transaction and update crooks about it. If the time passes and no payment has been made, presumably, the decryption key will be permanently deleted.
Has the mystery of HugeMe ransomware been solved?
For now, security researchers are not announcing about a free decryption software. Since this option is not available at the moment, you could try other methods that might revive files and make them accessible again. It is possible that HugeMe virus does not impact Shadow Volume Copies. If this turns out to be true, your files could be restored. In addition to this option, you also could try file-recovery tools that already exist. We cannot promise that they are going to work, but it is worth a try. As for people that have not encountered ransomware viruses before, you should keep it this way. Adopt a habit of storing your files in backup storages or keeping copies of them in USB flash drives. This will make you immune to ransomware infections. Since defeating these viruses is a rather complicated mission, we advise you to spend some time to secure your data rather than suffer from losing them all.
HugeMe ransomware: where does it come from?
It would be no news to become aware of a malicious spam campaign that delivers the payload of HugeMe ransomware. This is a very common trick to spread viruses among Internet surfers. Most of the time, the messages that reach people are constructed in an urgent manner, suggesting than user has no time to spare. However, this is just a wretched attempt to viciously deceive. If your inbox happens to welcome an odd message, never download the attachments from it. Currently, Microsoft Word documents with malicious macros are extremely popular files to be appended to email letters. Of course, HugeMe ransomware could be distributed via exploit kits or social networking: basically, there is a number of ways to invite a malicious payload into your system.
Spyhunter or Malwarebytes are the tools to count on when it comes to malware removal. These anti-malware programs will detect and remove HugeMe virus. Before that, you should make copies of the encrypted data in case the payload manages to delete it. Suggestions for manual removal and decryption are, as we mentioned earlier, below this article.
Hugeme Ransomware quicklinks
- Creating an image of HugeMe ransomware
- Has the mystery of HugeMe ransomware been solved?
- HugeMe ransomware: where does it come from?
- Automatic Malware removal tools
- How to recover HugeMe ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover HugeMe ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover HugeMe ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before HugeMe virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of HugeMe ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to HugeMe virus. You can check other tools here.Step 3. Restore HugeMe ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually HugeMe virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover HugeMe ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.