GX40 crypto-virus belongs to the type of malware that is the most difficult to treat and to erase from infected machines. Cleaning systems from infections is difficult as it is, but ransomware threats put up a more persistent fight than other samples. First of all, they conceal their presence until the encryption process is fully completed. Before that, victims usually have no clue about the underground activity being initiated. GX40 ransomware is a variant that exploits AES ciphers to support the encryption process. It appears to be that the public key for encryption and the public one for decryption will be generated uniquely for every victim. To receive it, the GX40 ransomware variant might require the infected device to be connected to the Internet. While contacting the C&C server of crooks, an exchange of important information occurs.
More details that should be mentioned about GX40 ransomware
GX40 ransomware wishes to receive the ransom in a virtual currency, popularly selected by ransomware developers. Bitcoins are the system that almost every this type of malware incorporates into its instructions, unless different form of money is chosen. It appears that that the authors of GX40 virus generate unique bitcoin addresses for every victim. Each and every one of them will be forced to make a transaction of bitcoins in no longer than 2 days time. If payment is not submitted through the time period of 48hour, the demanded ransom will be raised. If the ignorance continues for 7 days straight, hackers will no longer show interest and will delete the decryption code permanently.
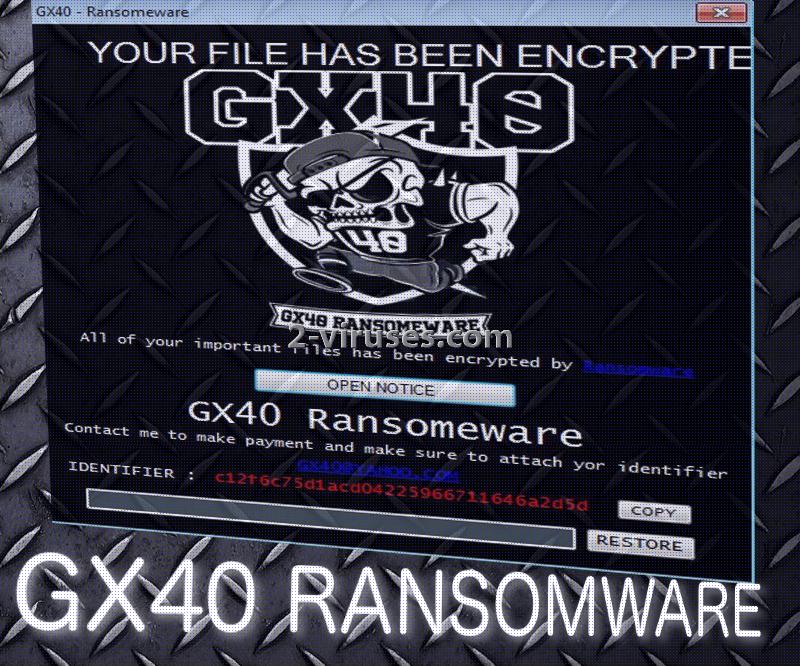
Authors of GX40 ransomware specify that they are expecting to receive approximately 0.07214 BTC which is 83.36 US dollars, according to the current rates. People that are compromised by GX40 infection will have a chance of contacting hackers via [email protected] email address. Additionally, all victims will be marked by a specific identifier which is a code of numbers and letters. This ID is supposed to be sent via the email address we mentioned before.
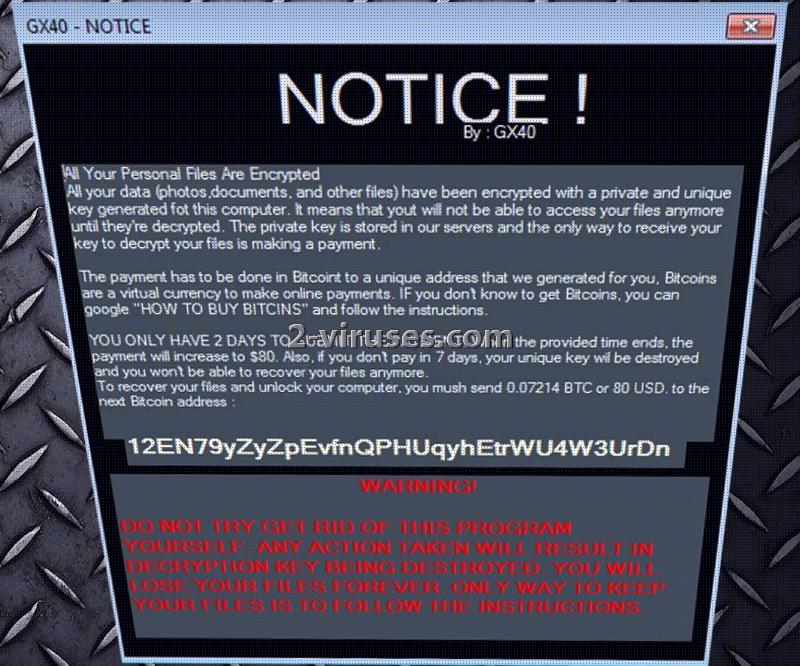
12EN79yZyZpEvfnQPHUqyhEtrWU4W3UrDn is the bitcoin wallet that belongs to hackers and could be one of the destination accounts, ready to be filled with victims’ money. It is possible that the payload of this virus is hiding under a fake name. For instance, it can be found under a file Validator.exe. However, it is also possible that the infection reveals its name by inserting GX40.exe. Academyx40.com website is somehow related with the hackers of GX40 crypto-virus. This was discovered after analysis of the link in the source. The page was determined to be an exclusive facebook group.
Encryption, decryption and other aspects, related to GX40 ransomware
The issues of GX40 ransomware has not been solved yet. For now, this infection is in development, which means that it is not finished just yet and might start to contain different features after further improvement. It adds .encrypted extension which is a rather commonly selected one. Ransomware infections should be feared and victims should realize that it is much more beneficial to take care a couple of things first so the future would be safer. For instance, you could store your data in backup storages or other alternative places that will provide you with easy access to your files. In case you lose your data from hard drives, you will be able to restore files from the backup.
GX40 ransomware and is road to success
Hackers of GX40 will decide which way should their virus be distributed. It is possible that this variant will be spread via vulnerable sites that it manages to influence with malicious scripts. Content that is capable of infecting you with ransomware might be found in malicious email letters that are sent to random email accounts. If you do wish to have your security compromised, you are not to open letters recklessly or download the attachments they provide. Links to websites can also be incorporated into email letters and they might lead to damaging domains.
Spyhunter, Plumbytes and Hitman are the tools that will efficiently clean your system from malware and other relevant threats. For possible decryption, you are to consider the options, explained in the following part.
Gx40 Ransomware quicklinks
- More details that should be mentioned about GX40 ransomware
- Encryption, decryption and other aspects, related to GX40 ransomware
- GX40 ransomware and is road to success
- Automatic Malware removal tools
- How to recover GX40 ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover GX40 ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover GX40 ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before GX40 virus has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of GX40 ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to GX40 virus. You can check other tools here.Step 3. Restore GX40 ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually GX40 virus tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover GX40 ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








