Globe ransomware is still alive, only in different form and name. We have experienced a comeback of Globe ransomware with Globe Imposter and even though this infection was defeated really fast as cyber security researchers from Emsisoft released a decryptor dedicated to Globe Imposter.
Sadly, this ransomware infection is back and now it is called Globeimposter 2.0. It is upgraded and more advanced – might be more complicated to detect, remove and decrypt files. This new version of Globe ransmoware uses different extension to lock files – it’s .726, thus some cyber security researchers even call it .726 ransomware.
Once inside of your computer Globeimposter 2.0 will scan all files stored on a hard drive to identify the ones that can possibly be locked. After the scan, it will add .726 extension to most of your personal files and encrypt them this way. So, for instance, if you had a file named game.exe, now it will look like this – game.exe.726. Files encrypted by Globeimposter 2.0 are extremely difficult to decrypt since they use military level RSA-2048 cryptography.
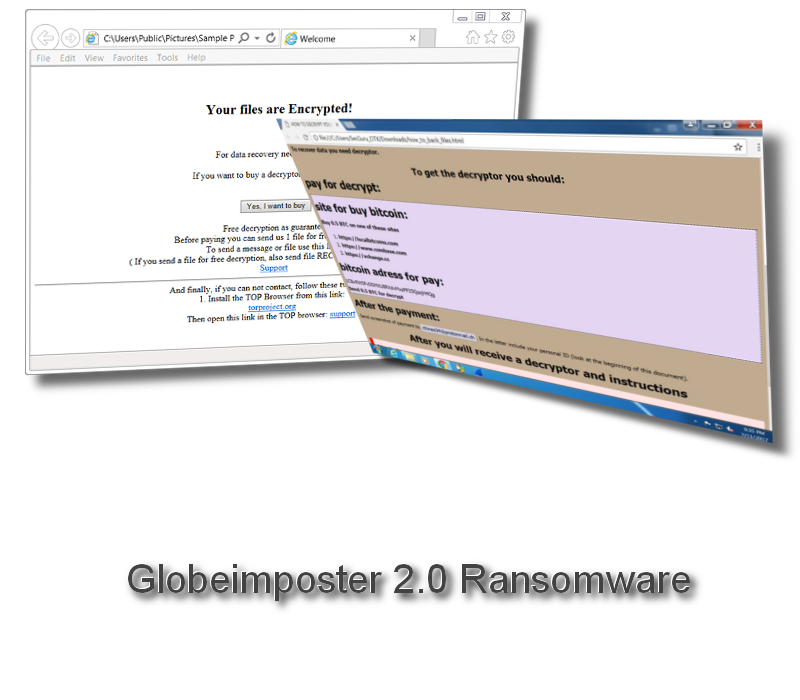
A file named ‘Recover-files-726.html’ will be placed on each and every folder with encrypted files. It is a ransom note, the information inside is supposed to give you directions towards decrypting your files. Original text of the note:
Your files are Encrypted!
For data recovery needs decryptor.
If you want to buy a decryptor, click the button
Yes, I want to buy
Free decryption as guarantee
Before paying you can send us 1 file for free decryption.
To send a message or file use this link.
(If you sen a file for free decryption, alse send file RECOVER-FILES.HTML)
And funally, if you can not contact, follow these two steps:
- Install the TOP Browser from this link:
torproject.org
Then open this link in the TOP browser.
You can tell by the poor spelling that creators of this ransomware are not a native English speakers. However, Globeimposter 2.0 virus is mainly targeted to users speaking English or Russian. As a motivation and proof of ability to decrypt files, you are offered to send 1 encrypted file to them so they could decrypt and send it back to you.
If you are willing to pay the ransom, you are supposed to visit their ransom website via Tor browser and follow instructions. First time you visit the page, ransom will be set to 0.37 Bitcoins, so at the current exchange rate it’s about $1200. In addition to that, you will be displayed a backwards clock with 24 hours ticking down. Once the number reaches zero, the ransom will be doubled to 0.74 Bitcoin. It’s a common technique to frighten users and force the to pay the ransom.
However, we suggest not to pay the ransom because there are no guarantees that you will retrieve your files anyways. Besides that, you would be contributing to the cyber criminals by paying the ransom and that’s not a good thing to do.
Globeimposter 2.0 ransomware is distributed as an attachment to email. This method is called malspam. Crooks send emails nto amed ‘Invoice’ and random numbers. Usually there is some .zip file attached to the letter. If you oppen that attachment, processes of the ransomware will be started automatically.
At the moment it’s impossible to decrypt .726 files encryption, so if you are not going to pay the ransom, the only way to retrieve locked files is to restore them from a backup. Regardless that, you have to eliminate Globeimposter 2.0 from your computer. That can be easily done with a reliable anti-malware application, such as Spyhunter. It will detect and remove the virus itself, all you have to do is to start a scan.
Globeimposter 2 0 Ransomware quicklinks
- Automatic Malware removal tools
- How to recover Globeimposter 2.0 Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Globeimposter 2.0 Ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Globeimposter 2.0 Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Globeimposter 2.0 Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Globeimposter 2.0 Ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Globeimposter 2.0 Ransomware. You can check other tools here.Step 3. Restore Globeimposter 2.0 Ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Globeimposter 2.0 Ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Globeimposter 2.0 Ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








