The ransomware, calling itself Globe, is another ransomware of the month, which, like the one named PokemonGo, is developed by some weirdo or weirdos dwelling in the cave of popular culture like some gypsies dwelling in the caves they call homes. This particular ransomware virus is based on the popular Purge series, telling an apocalyptic vision of todays postmodernism or, in other words,– the postmodern society of today’s world. Globe ransomware virus was discovered by Emsisoft cyber security researcher xXToffeeXx. We invite you to read the following to learn about this greasy cyber threat.
About Globe Ransomware
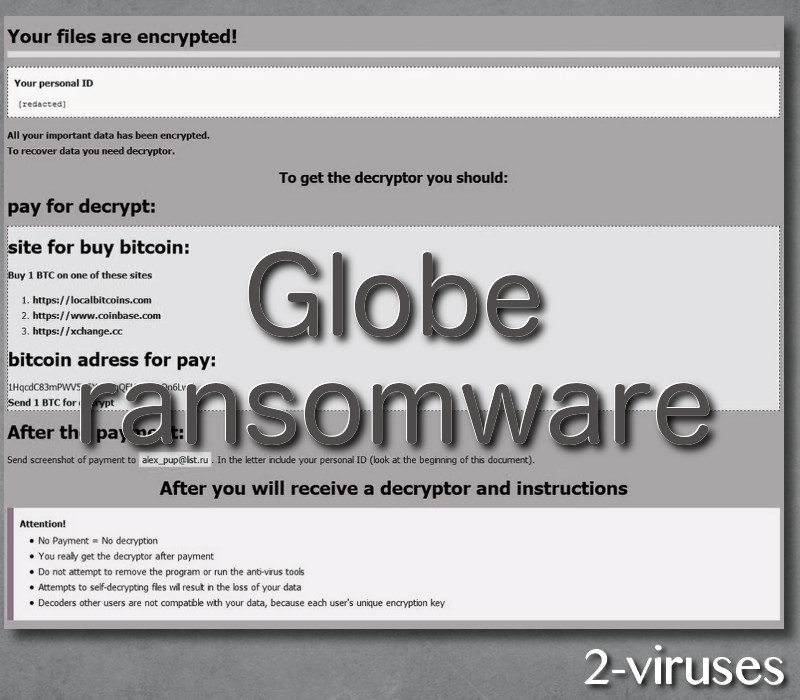
Globe cryptomalware is marching to the beat of a different drummer, and it does not associate with the rest of the modern ransomware viruses by using the Blowfish cipher instead of the popular AES encryption algorithm. Despite the fact that in the ransom note it says to damage the victim’s data with the standard asymmetric encryption. The manner it displays the ransom note is also different from the way the latest crypto-malwares show their messages. Unlike the conventional viruses of its type, which present the victim with a text and html files of ransom message, Globe virus displays the note in HTA or HTML. After it has finished, your desktop wallpaper will look like this:
It is a How_to_decrypt_your_files.jpg file which replaces your original desktop background. On an interesting note, if you have some sandbox software (isolating programs from the OS to prevent any unwanted data changes from happening) running on your operating system, the process initiated by the payload of Globe ransomware installed, that is the msiscan.exe executable file, will be terminated upon the initial stage. However, if you do not have any sandbox, the ransomware will start to encrypt your data. It will target the user profile, local drives, shared network folders and, finally, the desktop folder will be encrypted, displaying the picture presented above. The files, having the following extensions, are being aimed at:
aet, afp, agd1, agdl, ai, aif, aiff, aim, aip, ais, ait, ak, al, allet, amf, amr, amu, amx, amxx, ans, aoi, ap, ape, api, apj, apk, apnx, arc, arch00, ari, arj, aro, arr, arw, as, as3, asa, asc, ascx, ase, asf, ashx, asm, asmx, asp, aspx, asr, asset, asx, automaticdestinations-ms, avi, avs, awg, azf, azs, azw, azw1, azw3, azw4, b2a, back, backup, backupdb, bad, bak, bank, bar, bay, bc6, bc7, bck, bcp, bdb, bdp, bdr, bfa, bgt, bi8, bib, bic, big, bik, bin, bkf, bkp, bkup, blend, blob, blp, bmc, bmf, bml, bmp, boc, bp2, bp3, bpk, bpl, bpw, brd, bsa, bsk, bsp, btoa, bvd, c, cag, cam, camproj, cap, car, cas, cat, cbf, cbr, cbz, cc, ccd, ccf, cch, cd, cdf, cdi, cdr, cdr3, cdr4, cdr5, cdr6, cdrw, cdx, ce1, ce2, cef, cer, cert, cfg, cfp, cfr, cgf, cgi, cgm, cgp, chk, chml, cib, class, clr, cls, clx, cmf, cms, cmt, cnf, cng, cod, col, con, conf, config, contact, cp, cpi, cpio, cpp, cr2, craw, crd, crt, crw, crwl, crypt, crypted, cryptra, cs, csh, csi, csl, cso, csr, css, csv, ctt, cty, cue, cwf, d3dbsp, dac, dal, dap, das, dash, dat, database, dayzprofile, dazip, db, db_journal, db0, db3, dba, dbb, dbf, dbfv, db-journal, dbx, dc2, dc4, dch, dco, dcp, dcr, dcs, dcu, ddc, ddcx, ddd, ddoc, ddrw, dds, default, dem, der, des, desc, design, desklink, dev, dex, dfm, dgc, dic, dif, dii, dim, dime, dip, dir, directory, disc, disk, dit, divx, diz, djv, djvu, dlc, dmg, dmp, dng, dob, doc, docb, docm, docx, dot, dotm, dotx, dox, dpk, dpl, dpr, drf, drw, dsk, dsp, dtd, dvd, dvi, dvx, dwg, dxb, dxe, dxf, dxg, e4a, edb, efl, efr, efu, efx, eip, elf, emc, emf, eml, enc, enx, epk, eps, epub, eql, erbsql, erf, err, esf, esm, euc, evo, ex, exf, exif, f90, faq, fcd, fdb, fdr, fds, ff, ffd, fff, fh, fhd, fla, flac, flf, flp, flv, flvv, for, forge, fos, fpenc, fpk, fpp, fpx, frm, fsh, fss, fxg, gam, gdb, gfe, gfx, gho, gif, gpg, gray, grey, grf, groups, gry, gthr, gxk, gz, gzig, gzip, h, h3m, h4r, hbk, hbx, hdd, hex, hkdb, hkx, hplg, hpp, hqx, htm, html, htpasswd, hvpl, hwp, ibank, ibd, ibz, ico, icxs, idl, idml, idx, ie5, ie6, ie7, ie8, ie9, iff, iif, iiq, img, incpas, indb, indd, indl, indt, ink, inx, ipa, iso, isu, isz, itdb, itl, itm, iwd, iwi, jac, jar, jav, java, jbc, jc, jfif, jge, jgz, jif, jiff, jnt, jpc, jpe, jpeg, jpf, jpg, jpw, js, json, jsp, just, k25, kc2, kdb, kdbx, kdc, kde, key, kf, klq, kmz, kpdx, kwd, kwm, laccdb, lastlogin, lay, lay6, layout, lbf, lbi, lcd, lcf, lcn, ldb, ldf, lgp, lib, lit, litemod, lngttarch2, localstorage, log, lp2, lpa, lrf, ltm, ltr, ltx, lua, lvivt, lvl, m, m2, m2ts, m3u, m3u8, m4a, m4p, m4u, m4v, mag, man, map, mapimail, max, mbox, mbx, mcd, mcgame, mcmeta, mcrp, md, md0, md1, md2, md3, md5, mdb, mdbackup, mdc, mddata, mdf, mdl, mdn, mds, mef, menu, meo, mfw, mic, mid, mim, mime, mip, mjd, mkv, mlb, mlx, mm6, mm7, mm8, mme, mml, mmw, mny, mobi, mod, moneywell, mos, mov, movie, moz, mp1, mp2, mp3, mp4, mp4v, mpa, mpe, mpeg, mpg, mpq, mpqge, mpv2, mrw, mrwref, mse, msg, msi, msp, mts, mui, mxp, myd, myi, nav, ncd, ncf, nd, ndd, ndf, nds, nef, nfo, nk2, nop, now, nrg, nri, nrw, ns2, ns3, ns4, nsd, nsf, nsg, nsh, ntl, number, nvram, nwb, nx1, nx2, nxl, nyf, oab, obj, odb, odc, odf, odg, odi, odm, odp, ods, odt, oft, oga, ogg, oil, opd, opf, orf, ost, otg, oth, otp, ots, ott, owl, oxt, p12, p7b, p7c, pab, pack, pages, pak, paq, pas, pat, pbf, pbk, pbp, pbs, pcd, pct, pcv, pdb, pdc, pdd, pdf, pef, pem, pfx, php, pkb, pkey, pkh, pkpass, pl, plb, plc, pli, plus_muhd, pm, pmd, png, po, pot, potm, potx, ppam, ppd, ppf, ppj, pps, ppsm, ppsx, ppt, pptm, pptx, prc, prel, prf, props, prproj, prt, ps, psa, psafe3, psd, psk, pspimage, pst, psw6, ptx, pub, puz, pwf, pwi, pwm, pxp, py, qba, qbb, qbm, qbr, qbw, qbx, qby, qcow, qcow2, qdf, qed, qel, qic, qif, qpx, qt, qtq, qtr, r00, r01, r02, r03, r3d, ra, ra2, raf, ram, rar, rat, raw, rb, rdb, rdi, re4, res, result, rev, rgn, rgss3a, rim, rll, rm, rng, rofl, rpf, rrt, rsdf, rsrc, rsw, rte, rtf, rts, rtx, rum, run, rv, rvt, rw2, rwl, rwz, rzk, rzx, s3db, sad, saf, safe, sas7bdat, sav, save, say, sb, sc2save, sch, scm, scn, scx, sd0, sd1, sda, sdb, sdc, sdf, sdn, sdo, sds, sdt, search-ms, sef, sen, ses, sfs, sfx, sgz, sh, shar, shr, shw, shy, sid, sidd, sidn, sie, sis, sldm, sldx, slk, slm, slt, sme, snk, snp, snx, so, spd, spr, sql, sqlite, sqlite3, sqlitedb, sqllite, sqx, sr2, srf, srt, srw, ssa, st4, st5, st6, st7, st8, stc, std, sti, stm, stt, stw, stx, sud, suf, sum, svg, svi, svr, swd, swf, switch, sxc, sxd, sxg, sxi, sxm, sxw, syncdb, t01, t03, t05, t12, t13, tar, tax, tax2013, tax2014, tbk, tbz2, tch, tcx, tex, text, tg, tga, tgz, thm, thmx, tif, tiff, tlg, tlz, toast, tor, torrent, tpu, tpx, trp, ts, tu, tur, txd, txf, txt, uax, udf, uea, umx, unity3d, unr, unx, uop, uot, upk, upoi, url, usa, usx, ut2, ut3, utc, utx, uu, uud, uue, uvx, uxx, val, vault, vbox, vbs, vc, vcd, vcf, vdf, vdi, vdo, ver, vfs0, vhd, vhdx, vlc, vlt, vmdk, vmf, vmsd, vmt, vmx, vmxf, vob, vp, vpk, vpp_pc, vsi, vtf, w3g, w3x, wab, wad, wallet, war, wav, wave, waw, wb2, wbk, wdgt, wks, wm, wma, wmd, wmdb, wmmp, wmo, wmv, wmx, wotreplay, wow, wpd, wpe, wpk, wpl, wps, wsh, wtd, wtf, wvx, x11, x3f, xf, xis, xl, xla, xlam, xlc, xlk, xll, xlm, xlr, xls, xlsb, xlsm, xlsx, xlt, xltm, xltx, xlv, xlw, xlwx, xml, xpi, xps, xpt, xqx, xsl, xtbl, xvid, xwd, xxe, xxx, yab, ycbcra, yenc, yml, ync, yps, yuv, z02, z04, zap, zip, zipx, zoo, zps, ztmp, cry
There are 995 file types targeted in total. They are appended ‘‘.purge’’ extension to filename extensions of encrypted files. So, let’s say you have a file named ‘‘Book.pdf’’, after Globe encoder has made its dirty job, you will have ‘‘Book.pdf.purge’’ file, which is impossible to be read. When the data has been encrypted, How_to_restore_files.hta file is dropped in that affected folder. It is a file containing the ransom note, which reads as follows:
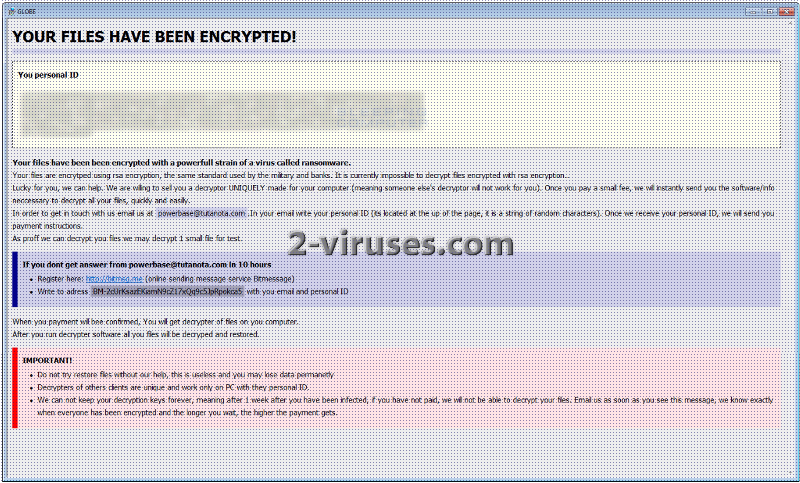
The How_to_restore_files autorun file will also be created so that the message was displayed automatically when the user logins to Windows. The contact e-mail address the note contains is [email protected] and the bitmessage address for paying the ransom is BM-2cUrKsazEKiamN9cZ17xQq9c5JpRpokca5. The size of the ransom remains unknown. Just the hackers behind Globe encrypter moderately state that it is ‘‘a small fee’’, if you believe them. You are given one week to transfer the payment and, then, supposedly receive the unique decryption key. After one week will have passed, you are threatened to lose your files forever. It is also mentioned that the longer you wait, the higher the payment gets.
Another interesting point is that Globe ransomware has a debug mode, which allows the user to control the program. However, the mode must be entered by adding the following registry entry – HKCU\Software\Globe\ “debug” = “YES”. Thus, the affected users cannot make use of this Globe’s feature. It can only be exploited by security researches to analyze the way the ransomware operates.
How is Globe Ransomware Spread?
The ways Globe file-encrypting virus is distributed are still obscure. We may speculate that it can be spread via infected spam e-mails and their attachments or that the payload of this crypto malware is downloaded by some exploit kits, after the detection of the vulnerabilities of your operating system, when you visit some questionable domains or happen to come up with hacked legit websites. But that will only be hypotheses lacking proper grounding. The more so, as we know that Globe encoder wants to stand out in the crowd of ransomwares.
How to Decrypt Files Encrypted by Globe Ransomware?
Unfortunately, data encrypted by Globe crypto malware is not decryptable at this point in time. This malware deletes Shadow Volume Copies and disable Windows Startup Repair with the following commands:
vssadmin.exe Delete Shadows /All /Quiet
bcdedit.exe /set {default} recoveryenabled No
bcdedit.exe /set {default} bootstatuspolicy ignoreallfailures
Nevertheless, the cyber security researches do not intend to lay down their arms and surrender to this nasty creature. The executable of Globe virus has been successfully extracted and it has been put under analysis. We hope that soon there will be results to present you with. Meanwhile, use your backup, if you have any. Apply data recovery software such as Recuva, R-Studio, PhotoRec, Kaspersky, etc., if you do not have any backups and you cannot wait for the decryptor to be released. The latter must be done only after you have copied your infected drive and removed the malware with professional automatic malware removal tools such as Spyhunter or Malwarebytes. Removing the virus with the latter tools results in your computer’s system being fully inspected and cleaned. You can also follow the guide for the manual removal of Globe ransomware, which we give you free of charge. See below.
Update. The Globe decryptor can be downloaded from here.
Update of the 4th of December, 2016. The most recent version of Globe ransomware appends .lovewindows extension to the corrupted files and provides the victims with [email protected] e-mail for contacting.
Update of the 14th of December, 2016. Globe ransomware spotted using [email protected] extension.
Update of the 16th of December, 2016. Globe crypto-malware now uses , extension.
Update of the 9th of January, 2016. Surprisingly, Globe ransomware has been noticed to tryout new fields: C/C++. It appends .locked extension to casualties. In addition to that, security researchers have discovered a way to restore files that have been encrypted with Globe variants that append .decrypt2017 and .hnumkhotep extensions to the files it corrupts. Find it here.
Update of the 27th of March, 2017. A decrypter for the third version of Globe has been released. Emsisoft is the one that produced this tool. Victims can download the decrypter from here.
Globe Ransomware quicklinks
- About Globe Ransomware
- How is Globe Ransomware Spread?
- How to Decrypt Files Encrypted by Globe Ransomware?
- Automatic Malware removal tools
- How to recover Globe Ransomware encrypted files and remove the virus
- Step 1. Restore system into last known good state using system restore
- 1. Reboot your computer to Safe Mode with Command Prompt:
- 2.Restore System files and settings.
- Step 4. Use Data Recovery programs to recover Globe Ransomware encrypted files
Automatic Malware removal tools
(Win)
Note: Spyhunter trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions,
(Mac)
Note: Combo Cleaner trial provides detection of parasites and assists in their removal for free. limited trial available, Terms of use, Privacy Policy, Uninstall Instructions, Refund Policy ,
How to recover Globe Ransomware encrypted files and remove the virus
Step 1. Restore system into last known good state using system restore
1. Reboot your computer to Safe Mode with Command Prompt:
for Windows 7 / Vista/ XP
- Start → Shutdown → Restart → OK.
- Press F8 key repeatedly until Advanced Boot Options window appears.
- Choose Safe Mode with Command Prompt.

for Windows 8 / 10
- Press Power at Windows login screen. Then press and hold Shift key and click Restart.

- Choose Troubleshoot → Advanced Options → Startup Settings and click Restart.
- When it loads, select Enable Safe Mode with Command Prompt from the list of Startup Settings.

2.Restore System files and settings.
- When Command Prompt mode loads, enter cd restore and press Enter.
- Then enter rstrui.exe and press Enter again.

- Click “Next” in the windows that appeared.

- Select one of the Restore Points that are available before Globe Ransomware has infiltrated to your system and then click “Next”.

- To start System restore click “Yes”.

Step 2. Complete removal of Globe Ransomware
After restoring your system, it is recommended to scan your computer with an anti-malware program, like Spyhunter and remove all malicious files related to Globe Ransomware. You can check other tools here.Step 3. Restore Globe Ransomware affected files using Shadow Volume Copies
If you do not use System Restore option on your operating system, there is a chance to use shadow copy snapshots. They store copies of your files that point of time when the system restore snapshot was created. Usually Globe Ransomware tries to delete all possible Shadow Volume Copies, so this methods may not work on all computers. However, it may fail to do so. Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, and Windows 8. There are two ways to retrieve your files via Shadow Volume Copy. You can do it using native Windows Previous Versions or via Shadow Explorer. a) Native Windows Previous Versions Right-click on an encrypted file and select Properties → Previous versions tab. Now you will see all available copies of that particular file and the time when it was stored in a Shadow Volume Copy. Choose the version of the file you want to retrieve and click Copy if you want to save it to some directory of your own, or Restore if you want to replace existing, encrypted file. If you want to see the content of file first, just click Open.
b) Shadow Explorer It is a program that can be found online for free. You can download either a full or a portable version of Shadow Explorer. Open the program. On the left top corner select the drive where the file you are looking for is a stored. You will see all folders on that drive. To retrieve a whole folder, right-click on it and select “Export”. Then choose where you want it to be stored.

Step 4. Use Data Recovery programs to recover Globe Ransomware encrypted files
There are several data recovery programs that might recover encrypted files as well. This does not work in all cases but you can try this:- We suggest using another PC and connect the infected hard drive as slave. It is still possible to do this on infected PC though.
- Download a data recovery program.
- Install and scan for recently deleted files.








